New tool detects AWS intrusions where hackers abuse self-replicating tokens

Security firm CyberArk has released a new tool called SkyWrapper that can detect a certain class of intrusions and malicious activity inside AWS (Amazon Web Services) computing environments.
These intrusions aren't the fault of a vulnerability in the AWS infrastructure. They occur after developers expose their AWS access tokens and credentials online, usually by hardcoding them into their application's source code.
Hackers scan for these exposed AWS credentials, gain access to an AWS account, and then either steal data or install malware on a customer's infrastructure.
A crucial part of these types of attacks is that hackers can retain access to a compromised environment as much as possible.
New technique abuses AWS STS
In two reports published over the past month, security firms CyberArk and NetSPI have detailed a new technique that hackers are now utilizing to hide their presence in compromised AWS environments.
As described by the two, the technique relies on hackers abusing the AWS Security Token Service (STS) to issue temporary tokens. These STS temporary tokens are meant to last between a few minutes to several hours and are usually employed to create temporary AWS infrastructure in case of an overload.
CyberArk and NetSPI say that hackers are using scripts that create temporary tokens in a loop -- using the existing (and soon-to-be-expired) temporary token to generate a new one to use going forward.
The technique allows hackers to keep their intrusions secret as regular STS activity -- which many AWS account owners aren't accustomed to investigate for suspicious activity.
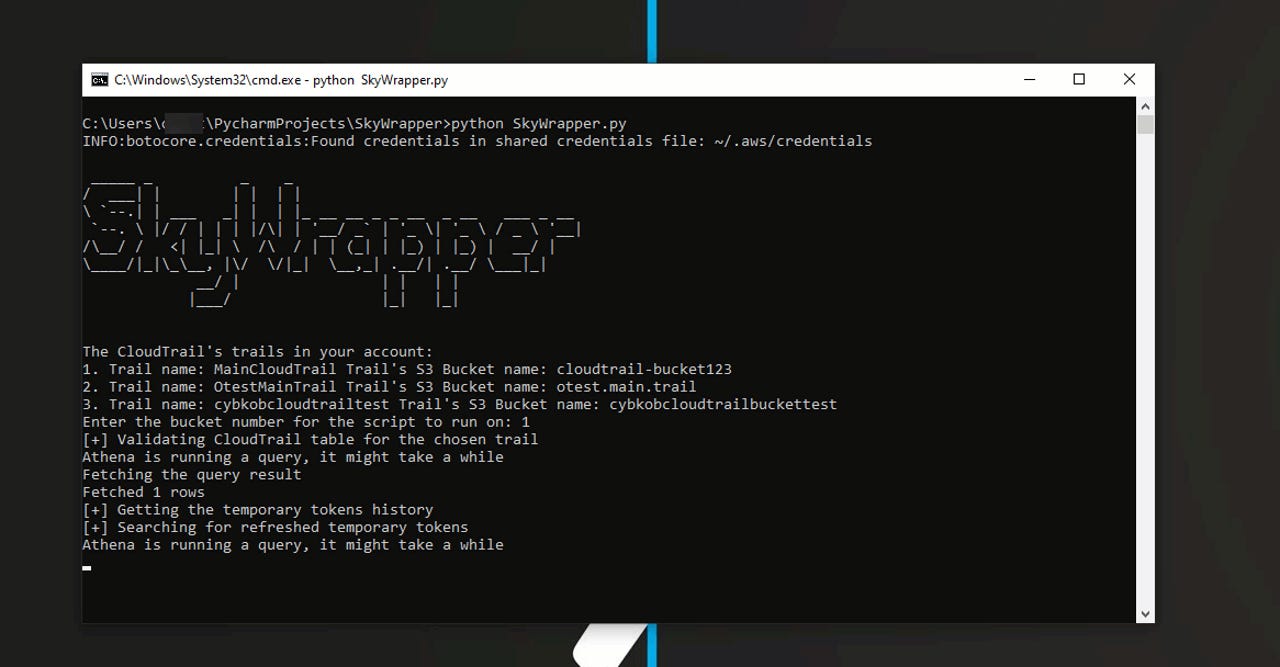
But this is where the new SkyWrapper tool comes to help. Open-sourced on GitHub, SkyWrapper allows AWS account owners to investigate STS activity for spikes in the issuance of temporary tokens.
The tool works by generating an Excel spreadsheet that lists all the currently active temporary tokens, but also the AWS access keys that were used to generate the temporary ones.
If a particular AWS (AKIA) access key generates a large number of temporary (ASIA) keys, then it's very likely that the AKIA key has leaked or has been compromised.
"I encourage you to run SkyWrapper and get a better view of the temporary tokens that exist in your environment, detect the privilege ones, and handle the ones which marked as suspicious. You will be surprised to see how many temporary tokens you have in your account," the CyberArk team said.