Blue screen of death saved Windows XP from WannaCry ransomware, say security researchers

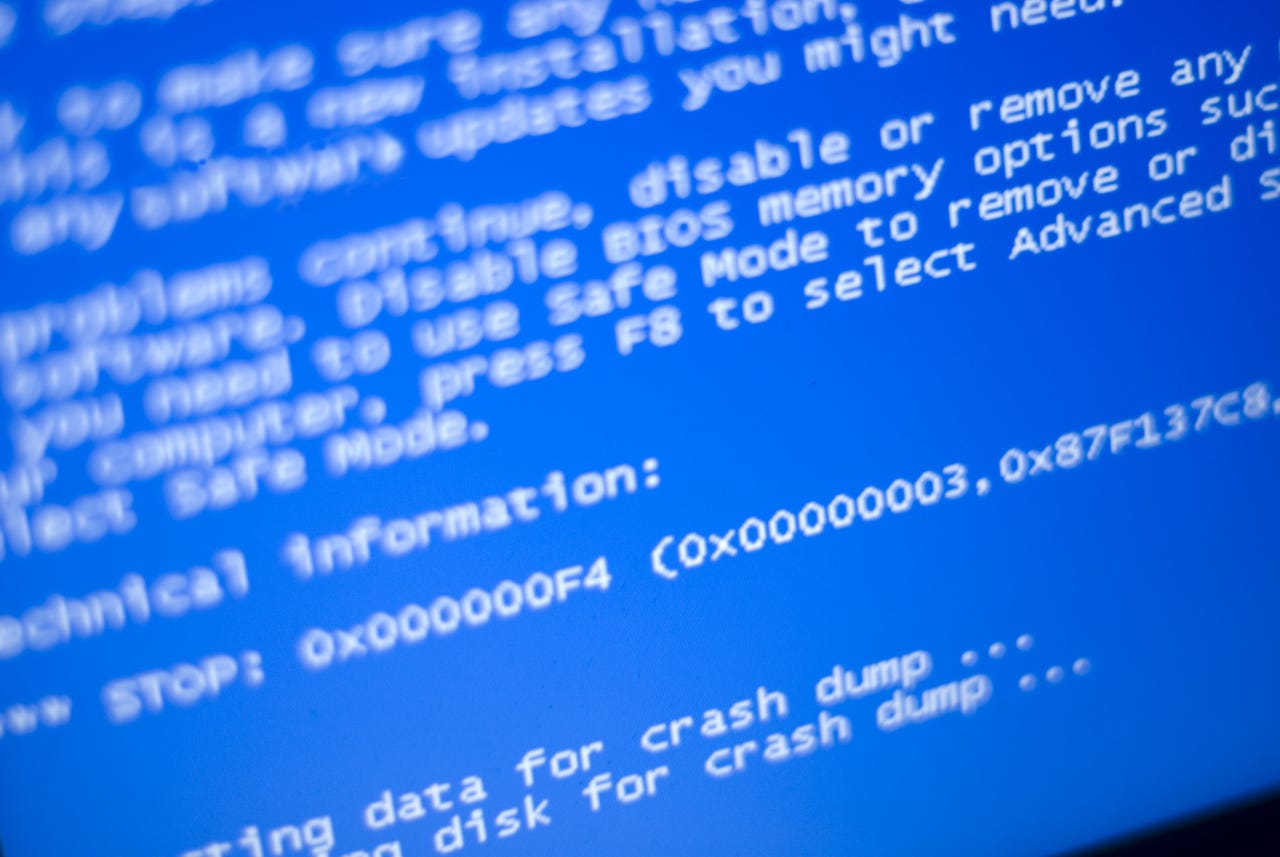
For many WannaCry victims using Windows XP, the worst-case scenario was a blue-screen of death, say researchers.
When WannaCry hit the world in mid-May, much focus was put on how the widespread use of the out-of-date Windows XP operating system helped it spread so fast.
The UK's National Health service was one of the highest-profile victims of the cyberattack -- and many of its bespoke systems still rely on Windows XP -- while Microsoft were quick to release a security patch for the long unsupported operating system.
And while Windows XP systems were among those affected by WannaCry, later analysis suggests that 98 percent of victims were running Windows 7.
ransomware attacks
But that's not to say WannaCry wasn't problematic for targets using Windows XP, with a new report by cybersecurity researchers at Kryptos suggesting that while the operating system was mostly immune from falling victim to the ransomware, many failed attacks resulted in computers crashing and displaying the 'blue-screen of death' and requiring a hard reset.
Researchers tested WannaCry ransomware against a number of operating systems running in a test environment: Windows XP with Service Pack 2, Windows XP with Service Pack 3, Windows 7 64 bit with Service Pack 1, and Windows Server 2008 with Service Pack 1.
While attacks against Windows 7 successfully installed WannaCry, after a number of attempts the supposedly vulnerable Windows XP was much more resilient to the ransomware than expected, with the OS running Service Pack 2 not becoming infected at all.
However, Windows XP running SP 2 was affected, but rather than becoming infected with WannaCry and requesting a ransom in return for locked files, the system kept blue-screening and rebooting itself.
"The worst-case scenario, and likely scenario, is that WannaCry caused many unexplained blue-screen-of-death crashes," say researchers.
While this phenomenon will have no doubt been frustrating for organisations which found their machines repeatedly crashing, at least they hadn't been infected by ransomware.
However, that doesn't mean Windows XP isn't vulnerable, as completely unpatched systems can still fall prey to WannaCry. The operating system remains a popular target for cybercriminals looking to exploit weaknesses in the many systems which have never been updated.
While WannaCry caused Chaos across the globe, the ransomware hasn't been particularly lucrative for its creators, only making around $110,000 in the almost three weeks since the initial outbreak -- a poor return for such a widespread campaign.
While the identity of those behind the WannaCry campaign remains unknown, researchers at cybersecurity firms including Symantec and Kaspersky have tentatively linked the attack to the Lazarus Group, a hacking operation which is believed to have acted in support of North Korea.
Meanwhile, linguistic analysis of ransom notes displayed to WannaCry victims suggests the author -- at least of the ransom demand -- is a natural or extremely fluent Chinese speaker. Both the authorities and cybersecurity firms continue to look for answers surrounding the origins of this destructive ransomware.
READ MORE ON WANNACRY
- Why was the WannaCry ransomware attack so widespread?
- Ransomware: An executive guide to one of the biggest menaces on the web
- Windows XP hit by WannaCry ransomware? This tool could decrypt your infected files
- How to defend yourself against the WannaCrypt global ransomware attack
- Ransomware: WannaCry was basic, next time could be much worse