Bogus IQ test with destructive payload in the wild
Upon execution, the malware will attempt to spread through removable media using a time-based logic bomb, and overwrite the MBR (Master Boot Record) of all available drives after 40 days for variant A, and 20 days for variant B, making the host's data inaccessible.
More info on the malware:
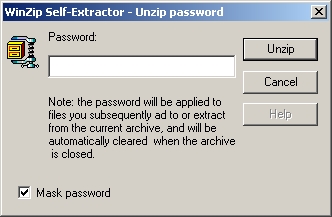
The worm uses two ways to spread – either via embedding in legitimate websites, in the form of a self-unpacking ZIP file or as an IQ test program, or via Exchangeable media, such as USB devices. The fact that it relies on USB devices to propagate is responsible for its rapid dissemination, which is likely to increase even further.
To date, the worm’s two variants - Win32/Zimuse.A and Win32/Zimuse.B differ in the method of spread and the timing of activation. While the A-variant needs 10 days to start spreading via USB devices, its B-variant needs only 7 days since infiltration. Moreover, the time needed for the execution of the destructive routine is shortened in the B-variant from the original 40 days to 20.
Moreover, once executed, the malware will also issue the following, typical for scareware/fake security software error message, in what appears to be an attempt by the malware authors to make the infected users contact the hosting provider of a particular site stating that it infected them with malware:
"System Defender - Kernel Error 0xC00000005
This problem is unambigously cause by malicious contents in IP packers in transport layer from website: www.offroad-lm.szm.sk. To bee patient, Windows Defender scan your hard drive(s) for bugs caused by system incompatible code. To recovery of system press OK button. Wait to successfull end of scanning. Inform about this administrator on www.szm.sk and incriminated web site."
BitDefender points out that due to the digitally signed drivers in 64-bit versions of Windows Vista and Windows 7, the worm would fail to install. A video demonstrating the infection has been released, as well as a Zimuse removal tool, available for free download.