Can you do this?

The raging debate over NAC included one aspect that I want to dwell on. That is the perception held by some that NetFlow is a tool for countering denial of service attacks. Certainly, the original NetFlow vendors, Arbor and Mazu, got their starts by countering denial of service attacks and a large percentage of their revenue still comes from ISPs that use their tools to identify sources of attacks and block them at the edge. But NetFlow is much too powerful a tool to be pigeon holed in the DoS defense category. Read my just published column at DarkReading: Getting to Know NetFlow.
And look at this output from a NetFlow management console that Lancope provided me with. Can you get this kind of image of your network?
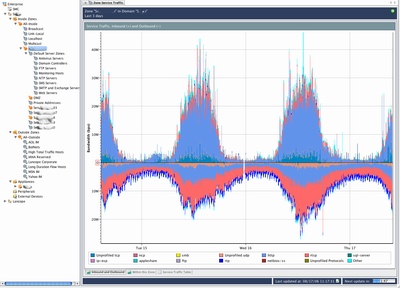
Click here for full size image.
It is not surprising that web traffic is the bulk of what this large corporation sees on their network. The RTSP, real time streaming protocol, is more revealing, it indicates that video and audio is making up a lot of the bandwidth utilization. With a good NetFlow console you can drill in to find a lot of interesting detail. I can’t imagine doing any capacity planning or even network debugging without the power of NetFlow. Read my article for the internal security benefits that come from NetFlow