Chinese hackers launch targeted attacks against foreign correspondents
The attacks coincide with the upcoming nation-wide celebration of the 60th anniversary of the PRC, and appear to be directly connected to the GhostNet cyber espionage network exposed earlier this year.
Key findings of the assessment include:
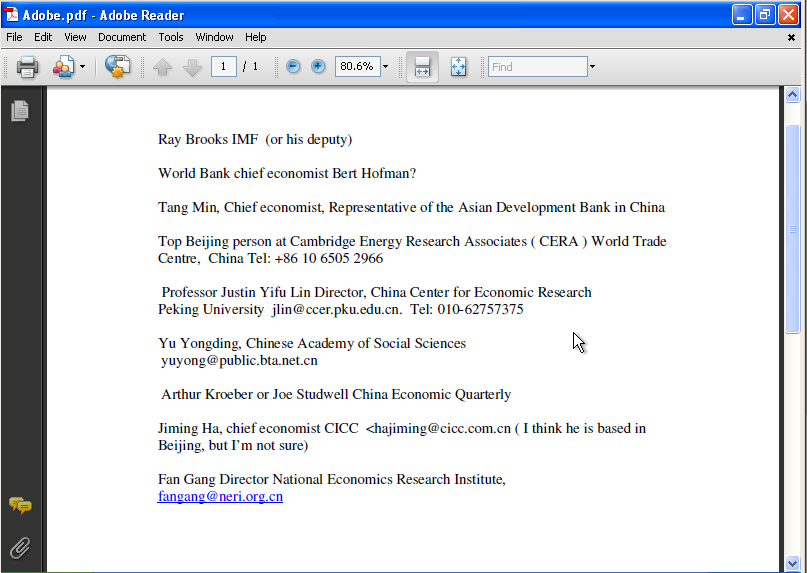
- The content of the email, and the accompanying malicious attachment, are in well written English and contain accurate information. The email details a reporter’s proposed trip to China to write a story on China’s place in the global economy; all the contacts in the malicious attachment are real people that are knowledgeable about or have a professional interest in China’s economy.
- The domain names used as “command & control” servers for the malware have been used in previous targeted attacks dating back to 2007. The malware domain names, as in previously documented cases, only resolve to real IP addresses for short periods of time. The malware exploits vulnerabilities in the Adobe PDF Reader, and its behaviour matches that of malware used in previous attacks dating back to 2008. This malware was found on computers at the Offices of Tibet in London, and has used political themes in malware attachments in the past.
- The IP addresses currently used by the malware are assigned to Taiwan. One of the servers is located at the National Central University of Taiwan, and is a server to which students and faculty connect to download anti-virus software. The second is an IP address assigned to the Taiwan Academic Network. These compromised servers present a severe security problem as the attackers may have substituted their malware for anti-virus software used by students, employees, and faculty at the National Central University.
The most logical approach to obtain the emails of the targeted correspondents in order to facilitate this social engineering based malware attack, would be to compile a list based on publicly obtainable data. The same practice was in planning stage but never got executed during the coordinated Russia vs Georgia cyber attack, when emails corresponding to government agencies were "harvested" for potential targeted malware attacks.
- Go through related posts: Chinese hackers deface the Russian Consulate in Shanghai; China detains web site defacer spreading earthquake rumors; China busts hacking ring, managed to penetrate 10 gov't databases; Chinese female hacking group spotted; Chinese Hacktivists Waging People's Information Warfare Against CNN; The DDoS Attack Against CNN.com
However, the researchers behind the assessment make an interesting observation. According to a Reuters article stating that the names of the targeted correspondents do not appear on public news reports and that they were hired through an agency that reports to China's Foreign Ministry, they raise an element of suspicion regarding the ways in which the attackers obtained emails that were supposedly not available to the public. In reality, though, this appears to be a simple data mining process relying on either already compromised hosts of foreign of Chinese journalists, or on the use of public search engines allowing the malicious attackers to easily build their "hit lists".
Whether a trend or an isolated incident coinciding with the 60th anniversary of the PRC, China's cyber espionage ambitions remain as high as ever.