Chromium DNS hijacking detection accused of being around half of all root queries

In an effort to detect whether a network will hijack DNS queries, Google's Chrome browser and its Chromium-based brethren randomly conjures up three domain names between 7 and 15 characters to test, and if the response of two domains returns the same IP, the browser believes the network is capturing and redirecting nonexistent domain requests.
This test is completed on startup, and whenever a device's IP or DNS settings change.
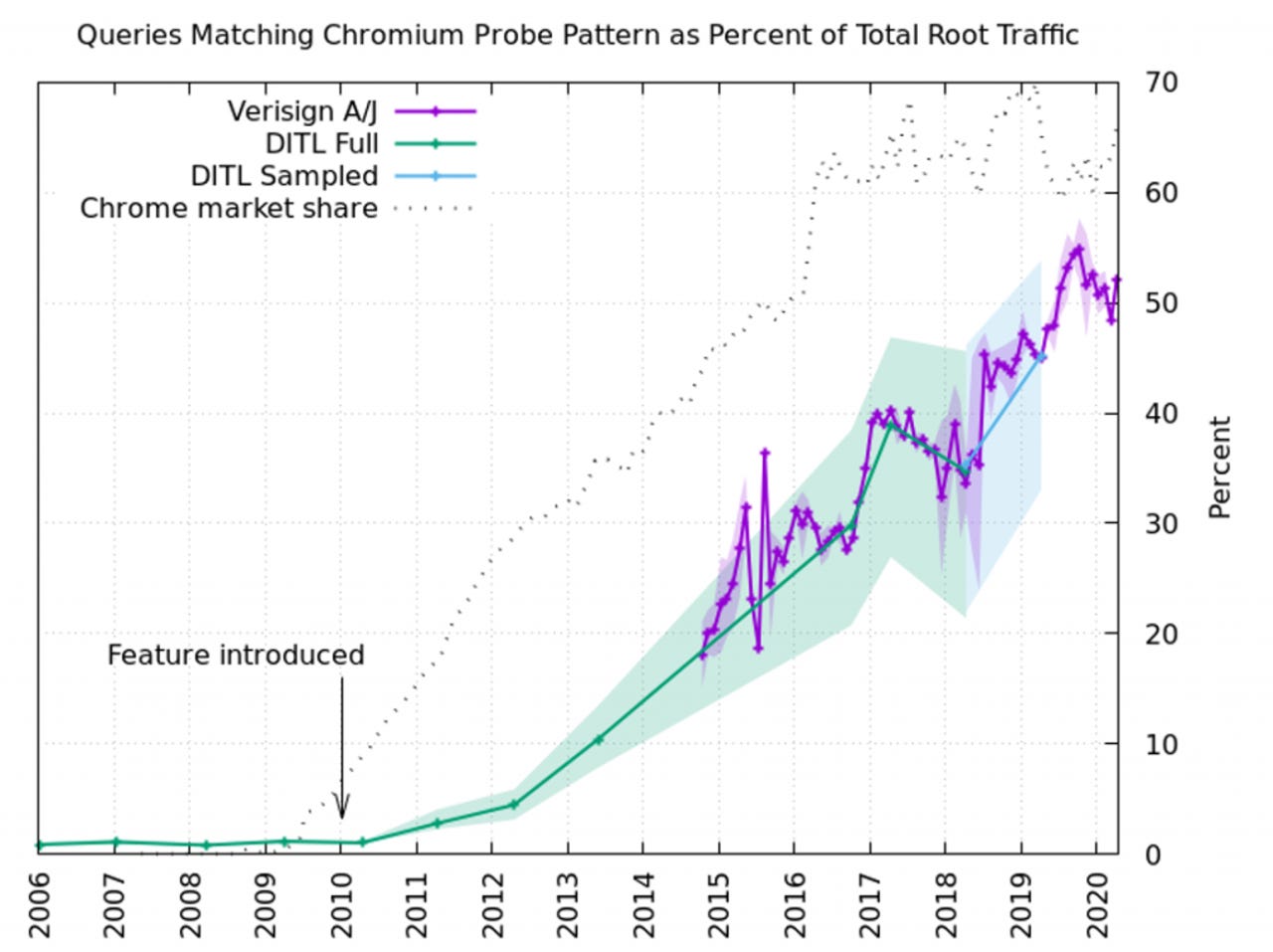
Due to the way DNS servers will pass locally unknown domain queries up to more authoritative name servers, the random domains used by Chrome find their way up to the root DNS servers, and according to Verisign principal engineer at CSO applied research division Matthew Thomas, those queries make up half of all queries to the root servers.
Data presented by Thomas showed that as Chrome's market share increased after the feature was introduced in 2010, queries matching the pattern used by Chrome similarly increased.
"In the 10-plus years since the feature was added, we now find that half of the DNS root server traffic is very likely due to Chromium's probes," Thomas said in an APNIC blog post. "That equates to about 60 billion queries to the root server system on a typical day."
Thomas added that half the DNS traffic of the root servers is being used to support a single browser function, and with DNS interception being "certainly the exception rather than the norm", the traffic would be a distributed denial of service attack in any other scenario.
Earlier in the month, Sans Institute dean of research Johannes Ullrich looked into how many of the world's 2.7 million authoritative name servers it would take to disable 80% of the internet.
"It only takes 2,302 name servers or about 0.084%!" Ullrich wrote.
"0.35% of name servers are responsible for 90% of all domain names."
Ullrich found GoDaddy was responsible for 94.5 million records, Google Domains had 20 million, the trio of dns.com, hichina, and IONOS had 15.6 million each, while Cloudflare had 13.8 million records.
"Using a cloud-based DNS service is simple and often more reliable than running your name server. But this large concentration of name services with few entities increases the risk to the infrastructure substantially," he said.
To lower the risk of a provider outage making parts of the internet inaccessible, Ullrich said people should run secondary name servers in-house, and make sure to use more than one DNS provider.
Telstra provided an example of how a DNS failure can appear as an internet outage to users, in this case, the telco successfully performed a denial of service attack on itself.
"The massive messaging storm that presented as a denial of service cyber attack has been investigated by our security teams and we now believe that it was not malicious, but a Domain Name Server issue," the telco said at the start of the month.
Last month, Cloudflare provided a similar example on a much bigger scale.