Citizens Financial sued for insufficient E-Banking security
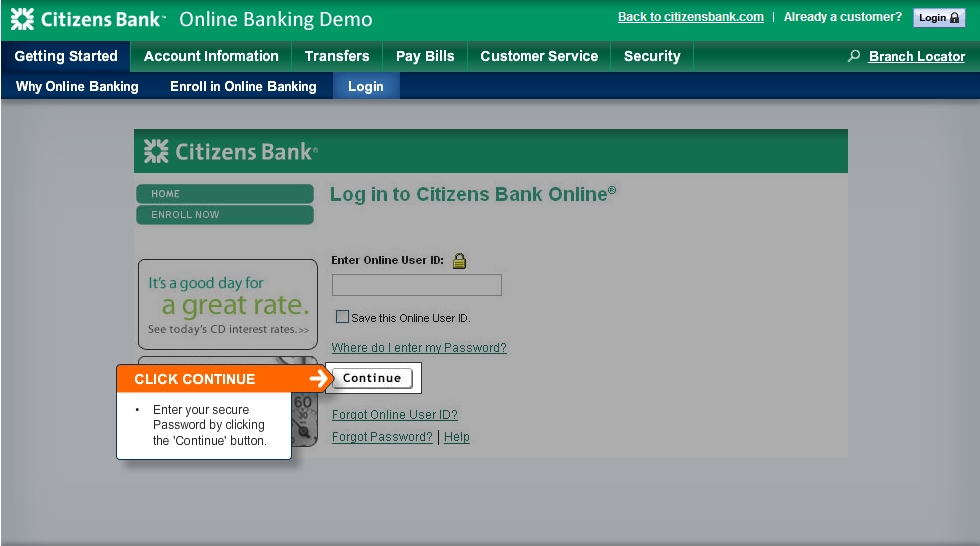
In the Shames-Yeakels vs Citizens Financial lawsuit, a couple that lost $26,500 due to a compromised account, may have all the good reasons to blame their bank's outdated E-banking authentication process, which in 2009 is a combination of SSL connection next to a user name and a password, with no sign of two-factor authentication in place:
At the time of the theft, Citizens had been in the process of issuing such tokens to customers, but the plaintiffs say they were too slow in rolling out this security measure. They pointed to a 2005 document from the Federal Financial Institutions Examination Council, which concluded that single-factor authentication was inadequate, and said that Citizens lagged behind other banks in offering this feature.
Citizens used a company named Fiserv to provide its online banking services, including information security services, and argued that Fiserv had a solid reputation in the banking industry and that its security measures were not the cause of the money transfer.
Would two-factor authentication have made any difference at the first place? That largely depends on the banker malware/crimeware that the customer gets infected with, since three of the most popular crimeware applications that used to proprietary tools in the arsenal of the sophisticated cybercriminal a couple of years ago, are not just publicly available nowadays, but are all capable bypassing badly implemented two-factor authentication solutions in place.
The success of these crimeware applications is so evident, that the number of managed crimeware services offering access to banker malware infected hosts, or raw logs of their E-banking authentication process for the purpose of session hijacking, is increasing and is therefore lowering the entry barriers into a market segment that used to be reserved for the more technically sophisticated cybecriminals a couple of years ago.
- Go through related posts: 75% of online banking sites found vulnerable to security design flaws; HSBC sites vulnerable to XSS flaws, could aid phishing attacks; CardCops: Stolen credit card details getting cheaper; Scammers caught backdooring chip and PIN terminals; Scammers introduce ATM skimmers with built-in SMS notification; Diebold ATMs infected with credit card skimming malware; Antivirus vendor introducing virtual keyboard for secure Ebanking; No security software, no E-banking fraud claims for you
SSL connections combined with "secure user name" and a password can't protect against sophisticated cybercriminals, in fact they can't even protect you from the average ones still relying on outdated approaches of obtaining accounting data through the use of keyloggers. What two-factor authentication and a decent understanding of the current/emerging threats can do, is mitigate a significant percentage of the risk that would have otherwise resulted in a successful compromise with less efforts on behalf of the cybercriminal.
What do you think? Who's to blame for the fraudulent transaction in this case - the couple which apparently was E-banking from a crimeware infected computer, or the bank for not offering two-factor authentication at the first place?
Talkback.