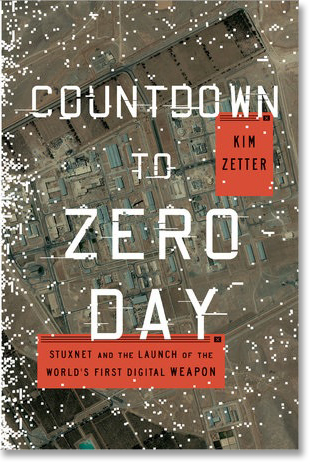
Countdown to Zero Day, book review: Dispatches from the first cyberwar

In the 1970s Broadway musical The Me Nobody Knows one of the children in the cast asks what it says about us that men and rats are the only two species that eat their own kind...and we eat rats.
The line came to mind while reading Kim Zetter's Countdown to Zero Day: Stuxnet and the Launch of the World's First Digital Weapon because, as she says, the United States and Israel are the only nations known to have used a cyber-weapon to attack another sovereign nation.
The result may have been, as intended, to slow Iran's ability to generate sufficient quantities of enriched uranium to make nuclear bombs, but the collateral damage was intense: the US and Israel lost the moral high ground from which to argue against cyber-warfare; the weapons they built are now out there and reusable by others; and other nations now see such strategies as legitimate. That's a pretty big 'oops'.
In Countdown to Zero, Zetter, an award-winning security journalist for Wired, recounts in meticulously researched and referenced detail the development, deployment and aftermath of Stuxnet, the aforementioned cyber-weapon, and its successors, Flame, Duqu, and Gauss. This is not easy material, since it involves not only understanding information technology and its inner workings, but also the technical detail of centrifuges and the process of uranium enrichment.
Unprecedented detail
The story begins as a multi-sided mystery. In Natanz, Iran, centrifuges are mysteriously failing at an unprecedented rate, requiring replacement. In Russia at Kaspersky and in the US at Symantec, researchers studying captured malware find an attack of unprecedented detail and complexity. Zetter follows both to their single cause: Stuxnet.
It's common in the first flush of panic when an attack happens to overestimate its destructiveness and cleverness. Not so in this case. Zetter takes apart, for example, the myriad convoluted layers of encryption with which Gauss was cloaked, both to protect it from being reverse-engineered by researchers and to ensure that it reached only its intended target -- customers of banks in Lebanon. The precision engineering involved here should be enough to scare anyone. No wonder, in the aftermath of Flame, that F-Secure chief technology officer Mikko Hypponen wrote openly that "consumer-grade antivirus products can't protect against targeted malware created by well-resourced nation-states with bulging budgets".
This is an important book: security researchers and practitioners need the detail, while policy-makers need the broad picture. As Zetter writes, given the choice between bombing countries at great expense, destroying buildings and killing people, and mounting a cyber-attack at much lower cost, it's not surprising that the military would have chosen this route.
And yet even their own people had warned them of the bigger risk of a cyber-weapon: "Somebody can pick it up and fire it right back at you." And that somebody, reusing the code that's already out there, does not need to be either as brilliant or as well resourced as the NSA.