Creating a key for every door

You have a log-in for Facebook, for online banking, for Twitter, for Gmail and still more for every service, website or app you use. If you're vigilant, you'll have a strong, separate password for each one, but if you're like most people, then you'll have the same one for almost everything, or make simple alterations for each site that are easy to guess.
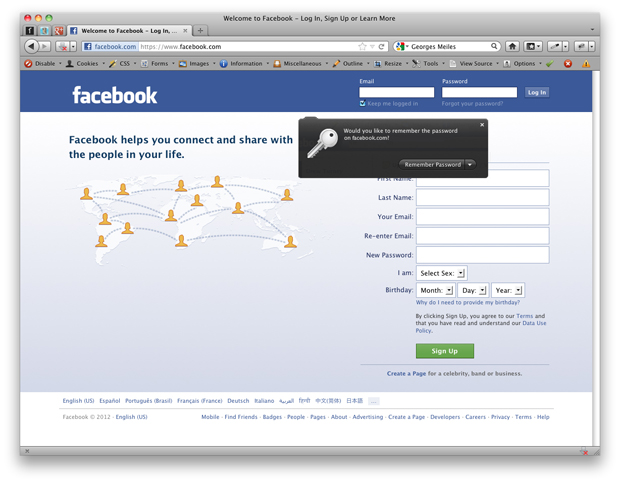
(Screenshot by Drew Turney/ZDNet Australia)
Steve Kirsch, CEO of identity provider OneID, thinks we're sick of it. "Many users are identifying this as the number one problem they have using the internet."
An alternative is to have a single online identity, a software or policy tool that gives you one point of entry for everything you log in to online. It sounds handy, but the risks and challenges are enormous. Who do you trust with all of your important online credentials, for example? And how does a single tool or service get access to the myriad application programming interfaces (APIs) that it needs to act on your behalf?
"Single-portal" services, like those offered by Google (covering email, maps, calendars, news and documents), are a start, and it's a world that we're used to, according to Solutionary regional technical manager Erik Barnett. "We've been preconditioned for this opportunity. If you use Apple, your single sign-on ID is your iTunes account information."
There's also the trend for websites to give users access to their services using your Facebook log-in, which makes Facebook a de facto identity clearinghouse.
But convincing users to do the same with information for more sensitive memberships, like bank account log-ins, is a very different matter.
"Although these tools have gained widespread acceptance, I think the general public is reluctant to use them for fear of fraud or identity theft," says Andrew Schrage of financial advice website MoneyCrashers.com.
The other possibility is allowing a tool to use an API without revealing log-in information. For example, if a user leverages HootSuite to post to Facebook, Twitter and other social media sites, they authorise HootSuite to make a virtual "handshake" with the relevant website without learning their password for that particular service. The downside is that the service still has to come to them for every transaction, rather than relying on a third party who has their credentials.
"Even with such third-party authorisation in place, letting a tool access sensitive accounts would require the user to authorise each transaction and negate any improvement in the user experience," says Layer 7 chief architect François Lascelles.
The only way to find a balance between security and ease of use, according to Identropy chief architect Nishant Kaushik, is to engage multiple layers that don't make a pain of themselves every time you use them. "The third-party identity must be enhanced by additional factors of authentication," he says. "But it needn't always be disruptive to the user experience.
"Some systems combine criteria, like device identification, geo-location or sensors with security badge access, to create risk scores. It allows for a more subtle experience, and users are encouraged to up-level their authentication only when the risk score shows that some variable has changed. If the system doesn't prompt that every time, we tend to be far more understanding about the extra protection."
So far, there are two such systems that have been widely adopted online.
The first is OpenID, a standard that sets out technological and policy parameters much like Bluetooth. The US-based OpenID Foundation promotes decentralised authentication, where a user signs up once with an OpenID identity provider, and uses it to sign in to any website that accepts OpenID authentication.
The second major system is OAuth, which works more like a "log-in lite" system. OAuth allows for the issuing of one-time-only log-in "tokens" that share data between specific websites or users for a limited time without giving up full account access. Originally developed to share Twitter data, the microblogging site is now one of OAuth's most widespread services, with Facebook, Foursquare, Google, Microsoft LinkedIn and more making use of it.
Yet, to use this sort of authentication for higher-risk services, governments likely need to take a hand, and they are already considering the online identity issue. In Sweden, for instance, the government has adopted a different option: the XML-based Security Assertion MarkUp Language (SAML) standard. But — as usual, when it comes to online technology — all eyes will be on the US. While there's no set policy or officially sanctioned toolset yet, the US government thinks it's an important area, with the National Strategy for Trusted Identities in Cyberspace (NSTIC) website calling for the development of interoperable technology standards and policies where "individuals, organisations and underlying infrastructure — such as routers and servers — can be authoritatively authenticated".
Whatever the governments do, they'll have to tread carefully. One security hole in an entrenched system might undermine the entire online ecosystem, with e-commerce alone worth $963 billion globally in 2013, according to Goldman Sachs.
For example, just last month, a Microsoft research paper identified two bugs in OpenID. A Google blog post also warned, "an attacker could forge an OpenID request that doesn't ask for the user's email address, and then insert an unsigned email address into the IDP's response. If the attacker relays this response to a website that doesn't notice that this attribute is unsigned, the website may be tricked into logging the attacker in to any local account."
Jason Ding, security researcher for Barracuda Labs, doesn't think that we're anywhere near ready to be able to use one password for everything. He agrees that the tools exist, but he says that they're simply not safe. "Not one single online identity provider can claim immunity after at least 18 severe breaches in the last two years impacting several millions of users."
However, despite the issues, some believe that we have to take the risk.
"People are hugely ready," Covisint chief security officer Dave Miller said, saying that the "identity weary" won't wait much longer.