Cybercriminals hijack Twitter trending topics to serve malware
The campaign, spreading since last week, is relying on a growing number of automatically registered bogus Twitter accounts, which combine trending topics and hashtags with custom messages and pre-defined Tinyurl links, all leading to identical fake codec which is droping three different malware samples.
Let's dissect their activities, and find a common pattern of exploitation.
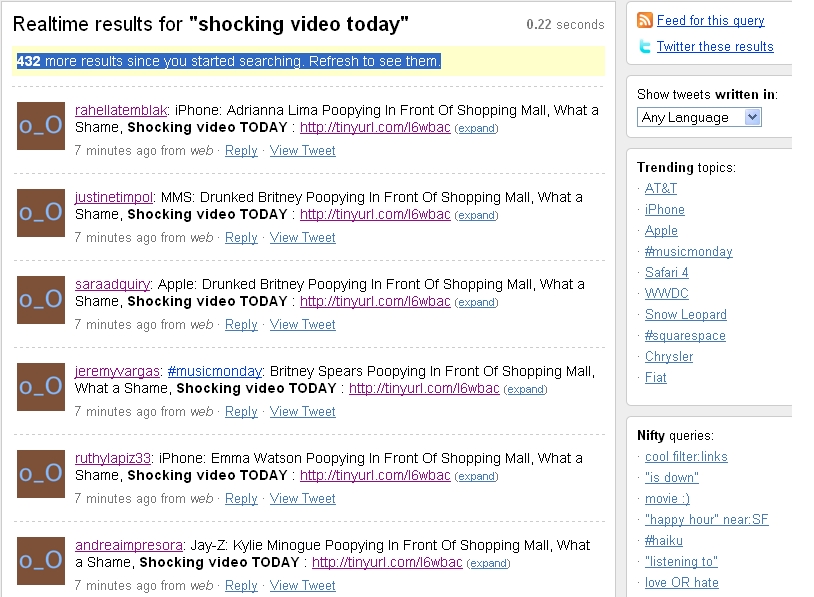
The tweets are generated by using popular hashtag or Trending topics combined with their campaign message and a relatively static Tinyurl link.
Here are some of the topics currently used in the campaign:
- Shocking video today, Headline news video, Shocking news theme
- Airplance crashes theme, for instance, Jumbo Jet 747 on fire, 280 deaths, Little Cessna crash in Vancouver, Airbus A330-200 Crash Video, Young childred killed in car crash, Terrible car crash in Fresno, CA, 15 deaths, online video, Airbus A330-200 Crash Video, AA AIRBUS A340 CRASH in Auburn, 189 fatalities
- Celebrities in front of shopping mall theme
- Rape theme - Raped Tonight by 20 skinheads - HEADLINE News Video, Pedophile raped over 580 children, Rihanna Raped Tonight by 20 skinheads in Maryland State. VIDEO
Cybercriminals adapt pretty fast, for instance, last week's campaign was using the bit.ly URL-shortening service which does cross-check submitted URLs for possible maliciousness using community-driven databases.
The effectiveness of this common sense technique is best described with the "Warning - this site has been flagged by SURBL and may contain unsolicited content." message served for the very same domain that the malicious parties are now freely redirecting to through TinyURL.