Cybercriminals offer bogus fraud insurance services
Security researchers from Trusteer have spotted a clever new technique used by cybercriminals interested in optimizing their malicious campaigns in an attempt to earn more revenue.
Here's how it works:
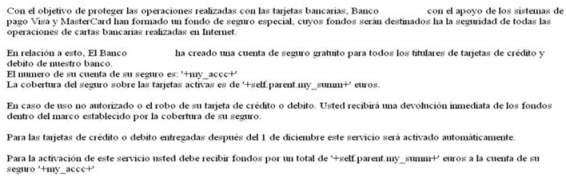
The recent attack we discovered uses the Tatanga malware platform. In the configuration file we captured, Tatanga notifies the online banking victim via a web browser injection that their bank is offering free insurance protection against online fraud.The victim is then presented with a fake insurance account that claims to cover the total amount of funds in their bank account. This fake insurance account is actually a real bank account that belongs to a money mule. The victim is told that they will be protected against any losses from online fraud by this insurance coverage. In the final step, the victim is prompted to authorize a transaction that they believe is to activate the insurance coverage. In all likelihood, the victim does not expect any funds will be transferred out of their account.To approve the transaction the victim enters a one-time SMS password that is sent to their mobile device. Unfortunately, the victim is actually approving a transfer of funds from their account to the fraudster’s money mule account.
Despite the technological implementation behind the success of the campaign relies on the Tatanga malware platform, a central role for the success of the concept is played by money mules.
Recruited though bogus 'work at home' job offers offering up to 45% revenue sharing schemes for amounts starting from $5000 and going up to $7000, thousands of average Internet users unknowingly become active participants in the cybercrime ecosystem. The process, now largely standardized, relies on bogus companies set up for the purpose of recruiting unaware Internet users into processing fraudulently obtained funds.
Trusteer's latest discovery is another indication that the cybercrime ecosystem isn't short on creative and new techniques to optimize hosts that are already infected with malware.
Find out more about Dancho Danchev at his LinkedIn profile, or follow him on Twitter.