Department of Parliamentary Services says February attack was 'detected early'

The claimed state actor that hit Australia's Parliament and its major parties last month was detected early, Secretary for the Department of Parliamentary Services (DPS) Rob Stefanic has said.
Writing in a submission [PDF] to the Joint Committee of Public Accounts and Audit Cyber Resilience inquiry, Stefanic said the incident was "addressed rapidly".
"During the remediation, the parliamentary network was unavailable for less than three hours in the early hours of the morning of February 8, highlighting our resilience to continue operations and respond effectively during a major cyber incident," he said.
"This event tested our processes and highlighted a number of issues which will be the target for future and ongoing improvement."
In the wake of the attack, DPS will re-examine its security controls.
The inquiry is following up on a July 2018 Auditor-General's report that focused on the security posture of the Department of the Treasury, National Archives of Australia, and Geoscience Australia, with DPS added later on.
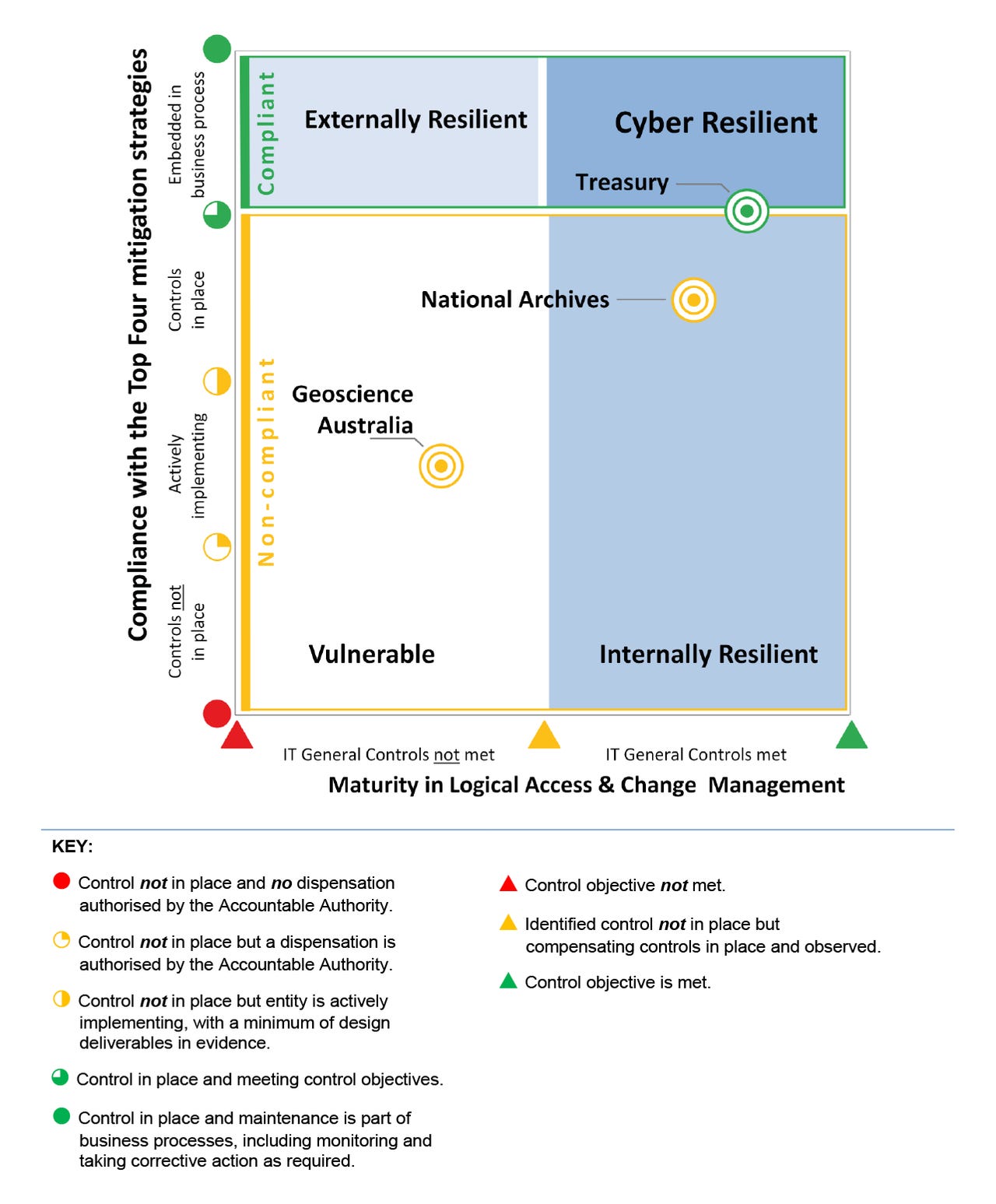
The report found Treasury was compliant with the Australian Signals Directorate's (ASD) Top 4 mitigated strategies and was cyber resilient, the top level available, while the National Archives had "sound ICT general controls" but was not compliant with the Top 4, and Geoscience Australia was found to be vulnerable to cyber attacks.
"All three entities had implemented only one of the four non-mandatory mitigation strategies in the Essential Eight, and were not well progressed in considering an implementation position for the other three strategies," the audit said.
In February 2017, the ASD extended its Top Four strategies into an Essential Eight.
Using the Auditor-General's labels, DPS said it was "in transition from internally resilient to that of cyber resilient" -- effectively meaning it had work to do fighting external threats.
"DPS has undertaken a shift in focus away from protecting systems to the protection and treatment of information as a strategic asset. An information audit is under way to identify the key information sources within the department," Stefanic said.
The secretary said DPS is unique within government agencies, and it needs to be able to be flexible yet secure.
"This presents a greater challenge compared to government departments, where controls and restrictions are easier to implement and enforce to achieve cyber resiliency," he said.
"DPS is committed to pursuing the optimum point between security and flexibility. However, it is highly likely in the coming months and years the level of security, control, and restrictions required will need to be increased in order to ensure security and the integrity of the ICT environment within which the Parliament operates."
DPS is responsible for the Parliament House network, as well as electorate and Commonwealth Parliament Offices, which accounts for over 5,000 users, 5,000 PCs and laptops, 1,000 servers, and over 2,000 mobile devices. It is currently constructing a dedicated parliamentary cyber centre.
For its part, Geoscience Australia said it will complete a security improvement program in June 2020 that will implement the Top Four, with the non-mandatory parts of the Essential Eight to be "configured appropriately". By the end of the 2019 fiscal year, Geoscience Australia intends to deploy application whitelisting, it said.
Related Coverage
Australia should name parliament cyber attackers
In the case of such a blatant attack on Australia's institutions of government, we should stand ready to point the finger and impose some real costs on the adversary.
Australia isn't buying local cyber and the rest of the world might soon follow
Early Stage technology investor and partner at Amadeus Capital, Alex van Someren, has warned the encryption-busting legislation hasn't made Australia an attractive place to buy cyber from.
Australian government computing network reset following security 'incident'
Department of Parliamentary Services says there is no evidence to suggest data has been taken or accessed, or that the incident is part of a plan to influence electoral processes.
Australian political parties also hit by state actor in parliamentary network attack: PM
Prime Minister Scott Morrison has said a sophisticated state actor also hit the networks of Australia's political parties when it attacked the parliamentary network.
Australia's Huawei ban a 'resolved' question: Payne
Australia has made its sovereign decision, says Marise Payne. Other nations will make their own.