Did Adobe hide 400 vulnerability fixes in latest Flash Player patch?

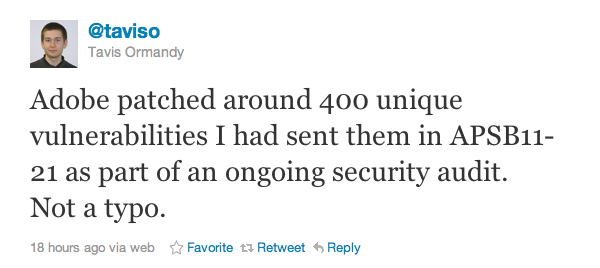
A high-profile Google researcher has accused Adobe of hiding the fact that it patched a whopping 400 unique vulnerabilities in yesterday's critical Flash Player update.
According to Tavis Ormandy, an information security engineer at Google who has a history of controversial vulnerability disclosures, the 400 unique Flash Player vulnerabilities were sent to Adobe as part of an ongoing security audit but there's no documentation on these fixes in the new update.
"Apparently that number was embarrassingly high, and they're trying to bury the results, so I'll publish my own advisory later today," Ormandy said on his Twitter feed.
Adobe's advisory that accompanies the Flash Player update does in fact acknowledge Ormandy's work:
Adobe would also like to thank Tavis Ormandy and the Google Chrome team for their great work on several improvements to this Flash Player release.
However, only 13 unique vulnerabilities are documented in the release and this prompted a series of snippy back-and-forth Twitter messages between Ormandy and Adobe spokeswoman Wiebke Lips.
"Tavis, please do not confuse sample files with unique vulnerabilities. What is Google's agenda here?" Lips said. (This Twitter message has since been deleted).
Ormandy's response:
"I don't know what Google's agenda is, but my agenda is getting credit for my work and getting vulnerabilities documented."
Almost lost in the public spat is the fact that Adobe's ubiquitous Flash Player contains vulnerabilities that could lead to remote code execution attacks. The security flaws, described as "critical," affect Adobe Flash Player 10.3.181.36 and earlier versions for Windows, Macintosh, Linux and Solaris, and Adobe Flash Player 10.3.185.25 and earlier versions for Android.
"These vulnerabilities could cause a crash and potentially allow an attacker to take control of the affected system," Adobe warned.
Adobe also shipped separate advisories to warn about security holes in Shockwave, Flash Media Server, Photoshop and RoboHelp.
- APSB11-19 – Security update available for Adobe Shockwave Player (Critical Severity)
- APSB11-20 – Security update available for Adobe Flash Media Server (Critical Severity)
- APSB11-22 – Security update available for Adobe Photoshop CS5 (Critical Severity)
- APSB11-23 – Security updates available for RoboHelp (Important Severity)
* See more from Computerword's Gregg Keizer on the Ormandy/Adobe spat.