eBay solutions provider Auctiva.com infected with malware
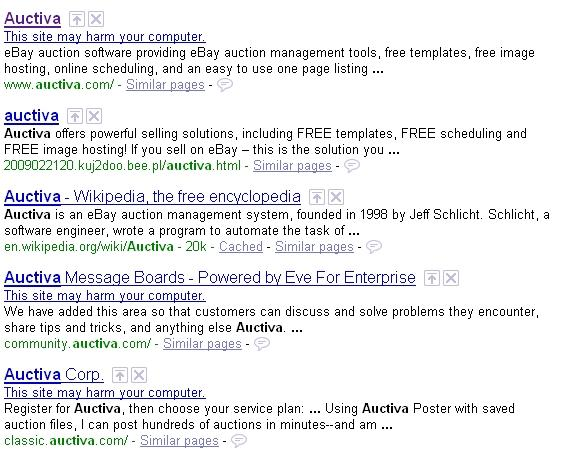
Following the complaints of users who started receiving antivirus software warnings appearing upon visiting Auctiva.com, the company took measures to ensure the transparency of the clean-up process which they finalized yesterday.
According to Auctiva's update log:
"Our engineering team is still investigating this situation but, at this point, it appears the reason these virus alert warnings started showing up on our site is because some of our machines were injected with malware originating in China. The malware we believe to be at fault has also hit a number of other high profile websites over the past 6 months. If our current suspicions about what happened are correct, we know some things we can do to prevent this from happening again, but some additional investigation will be required before we reach a conclusive determination.
The affected machines are no longer in our rotation so it is currently safe to navigate the Auctiva website, however, if you did visit our site between Thursday evening and Saturday afternoon at about 2 PM PT, as a precautionary measure, we recommend taking the following actions to ensure that your computers are not infected."
Let's assess the campaign and find out who's behind it. Auctiva.com appears to have been embedded with malware on the 18th of February, several days ahead of the company's announcement according to affected users. The exploits serving URLs, luckffxi .com and auctlva .com -- both domains parked at the same IP 67.229.127.42 -- are typical exploits serving sites courtesy of Chinese attackers which despite the fact that several Russian web malware exploitation kits are already localized to Chinese, continue using the same descriptive file structure for the client-side exploits in a manual fashion. For instance:
luckffxi .com/flash.htm luckffxi .com/14.htm luckffxi .com/office.htm luckffxi .com/real.htm
With last week's active exploitation of MS09-002 by Chinese attackers, next to Adobe Acrobat's zero day where another Chinese link could be easily established, this may well be the kick-off month for 2009's malicious activity courtesy of Chinese cybecriminals. What are they after? Passwords for massively multiplayer online role-playing games (MMORPGs), at least in Auctiva.com's campaign.