Fake CNN news items malware campaign spreading rapidly
A currently active malware campaign taking advantage of a known social engineering tactic, namely, to entice the spammed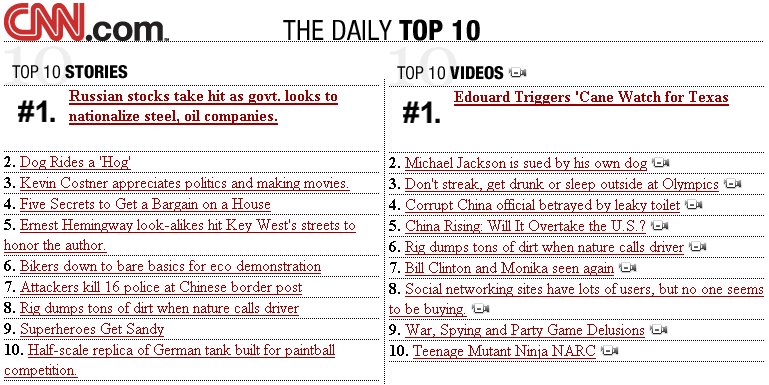
"Heads up on a new, very high volume Fake CNN News Update spam run that is making the rounds. The subject of the email is "CNN.com Daily Top 10." Our Threat Operations Center has seen over 5 million of these just in the last hour alone and over 80 million in the last 24 hours. This new CNN tactic is likely to be more successful than the single-line spam tactic that we had been seeing over the past several weeks as this message looks like it could be an news update email sent by CNN. This new message also attempts to trick the user into believing that they signed up to receive it because of their email preference settings at the CNN web site. If you see this message come into your inbox, delete it immediately."
Approximately, a thousand legitimate and on purposely registered to be abused in the attack domains are currently participating, with the malware authors continuing to use retro client-side exploits like the following detected by ThreatFire's assessment at the end of July, so an end user susceptible to any of these might not even get the chance to deny the download attempt of the binary itself :
"- Old reliable MS06-014 MDAC Vulnerability (nothing new here) - The fresh new Microsoft Office Snapshot Viewer ActiveX control race condition - The one year old Online Media Technologies NCTsoft NCTAudioFile2 ActiveX buffer overflow - A one year old stack overflow in GomManager - The recent RealPlayer.Console heap vulnerability - The 2006 ancient WebViewFolderIcon.setSlice integer overflow vulnerability"
From a social engineering perspective, rogue media codecs started getting replaced by fake Windows Media Players and
Moreover, despite that the campaign is faily easy to detect since it's using a static message next to the numerous different topics within the message itself, taking into consideration the fact that just like the majority of today's malware campaigns are taking advantage of outdated and already patched vulnerabilities, ensuring that you're not going to get exploited with last year's security vulnerability is highly recommended. Too bad that millions of Internet users could in fact be exploited in such a way.