Fake "Conficker Infection Alert" spam campaign circulating
The event-based social engineering campaign is also impersonating various Microsoft security departments in order to improve its truthfulness. This is the second attempt in recent weeks to hijack anticipated traffic, following last week's campaign consisting of typosquatted conficker removal tool domains aiming to impersonate the legitimate ones.
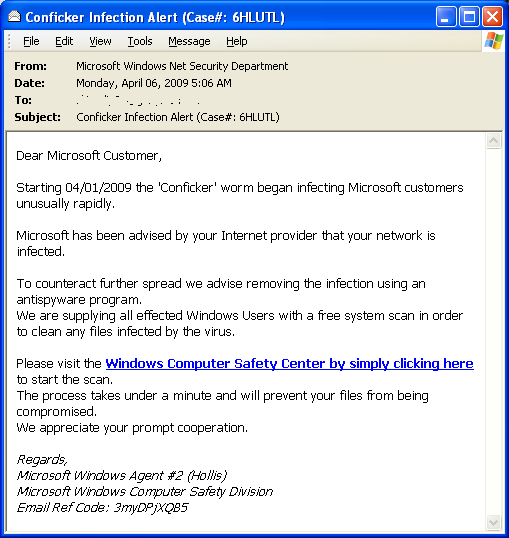
Here's the message, its associated subjects and related rogue security software domains used in the spam campaign:
"Dear Microsoft Customer,
Starting 04/01/2009 the 'Conficker' worm began infecting Microsoft customers unusually rapidly. Microsoft has been advised by your Internet provider that your network is infected.
To counteract further spread we advise removing the infection using an antispyware program. We are supplying all effected Windows Users with a free system scan in order to clean any files infected by the virus.
Please visit the Windows Computer Safety Center by simply clicking here to start the scan. The process takes under a minute and will prevent your files from being compromised. We appreciate your prompt cooperation.
Regards, Microsoft Windows Agent #2 (Hollis) Microsoft Windows Computer Safety Division Email Ref Code: RANDOM NUMBER"
Typical messages include: Infection Alert; Conficker Infection Alert; Microsoft Alert; Security Breach, with the end user redirected to the following scareware domains upon clicking on the links: antivirus-av-ms-check .com; antivirus-av-ms-checker .com; ms-anti-vir-scan .com; mega-antiviral-ms .com.
Such event-based scareware/malware/spam campaigns are constantly evolving from the static theme picked up from the front page of a major news portal, to the real-time syndicating of hot keywords and hijacking of popular titles in order to occupy the top search positions at a specific online video sharing service. Ironically, the original Conficker variant was directly aiming to monetize the infected hosts by pushing rogue security software and earning revenue in the process, at least temporarily until the affiliate network went in a cover-up phase, and Conficker introduced a new variant that was no longer generating so much noise that could potentially result in more leads to the original authors -- they wish.
Ignoring the Conficker copycats and the scareware distributors for a second, yesterday, the latest Conficker variant introduced a new payload with TrendMicro continuing to investigate its real intentions. These cosmetic changes are prone to take place in the weeks to come, until the Conficker authors start monetizing the infected hosts by either partitioning the botnet, or directly start offering managed cybercrime facilitating services.
TrendMicro's assessment proves one thing - that the cybercrime ecosystem is way too small even for big botnet operators to avoid each other. The changes made to WORM_DOWNAD.E. attempts to download another encrypted file from a well known domain of the Waledac botnet, which on the other hand is also known to have been sharing infrastructure with the original Storm Worm botnet.