FireEye, Fox-IT launch free service to combat Cryptolocker ransomware

FireEye and Fox-IT have launched a free tool to assist victims of the CryptoLocker ransomware.
Announced on Wednesday, the new service, dubbed DecryptCryptoLocker, is available for free to assist those impacted by the CryptoLocker ransomware.
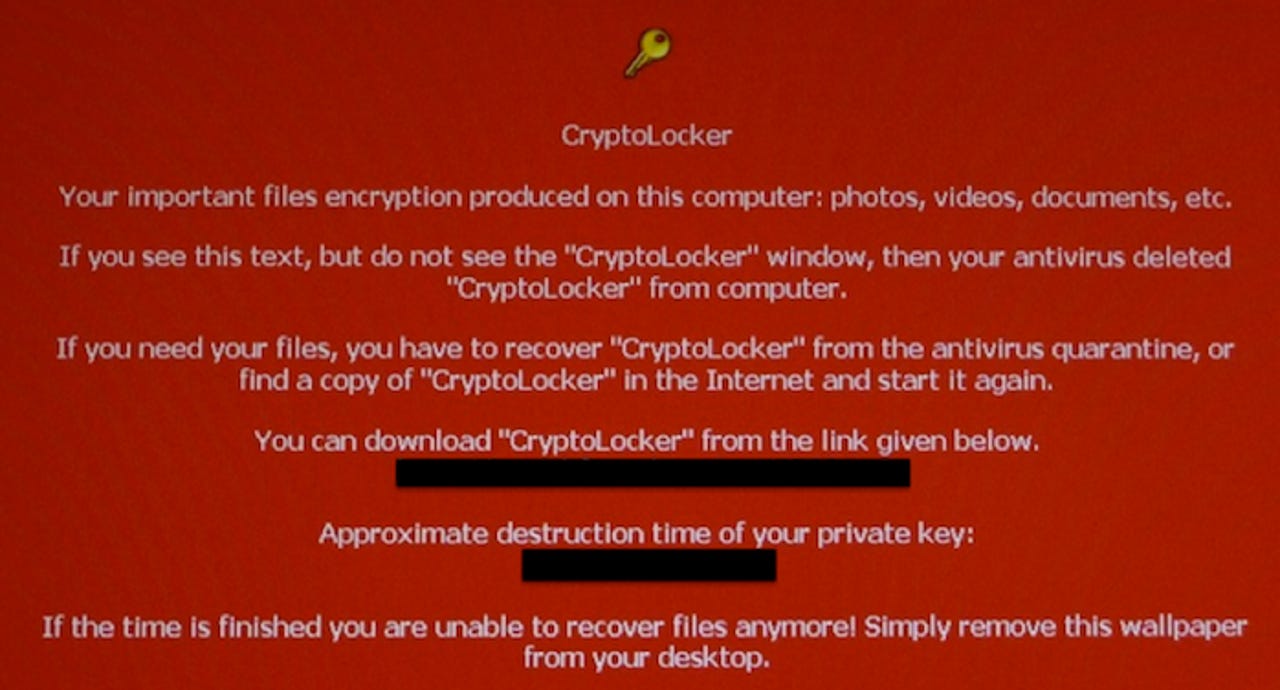
CryptoLocker is Windows-based malware that arrives on a system through means including phishing campaigns and watering hole attacks. The malware then aggressively infects the machine -- and in some cases, backups if mounted to such a system -- and encrypts the user's files. An onscreen timer then demands payment within 72 hours, typically around $300. If the victim pays up, they are sent a private key to unlock their files.
In December last year, Dell SecureWorks estimated that CryptoLocker has managed to infect 250,000 victims. The US Department of Justice has reported that the CryptoLocker crime wave has been stopped and neutralized, this has still often left victims without access to their files if they refused to pay the ransom.
In order to use the DecryptCryptoLocker tool, users need to:
- Identify a single, CryptoLocker-encrypted file that they believe does not contain sensitive information.
- Upload the non-sensitive encrypted file to the DecryptCryptoLocker portal.
- Receive a private key from the portal and a link to download and install the Decryptolocker.exe decryption tool which can be run locally on their computer.
- Finally, run the decryption tool locally on their computer, using the provided private key, to decrypt the encrypted files on their hard drive.
"We are excited to work with Fox-IT to offer a free resource that can help thousands of businesses affected by the spread of CryptoLocker over the last few months," said Darien Kindlund, director of threat intelligence at FireEye. "No matter the type of cyber breach that a business is impacted by, it is our goal to resolve them and get organizations back to normal operations as quickly as possible."
DecryptCryptoLocker is available worldwide. There are several variants of CryptoLocker, and so the tool may not be able to successfully decrypt every file.
Chris Boyd, Malware Intelligence Analyst at Malwarebytes told ZDNet:
"Anything that prevents victims of Cryptolocker from paying the ransom would mean the criminals behind these attacks may abandon this method as it could become less profitable over time. Having said that, information about the specifics of this tool are currently thin on the ground and it may not work on all forms of Ransomware."