GameOver Zeus botnet seized; Two week window to protect yourself, say authorities

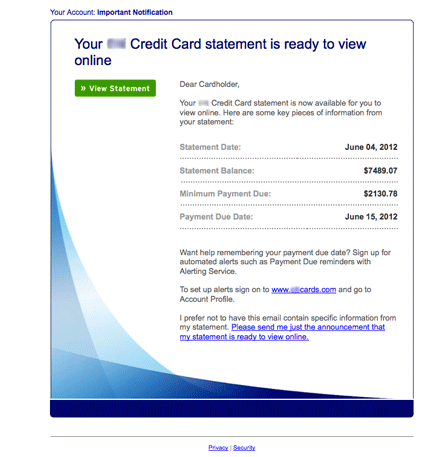
U.S. authorities---the Department of Homeland Security, Federal Bureau of Investigation and Department of Justice---say they have disrupted the systems of the GameOver Zeus botnet, which allows cybercrooks to steal banking credentials.
The move by authorities means there's a two-week window for enterprises and consumers to protect themselves before a wave of botnets is about to hit. GameOver Zeus (GOZ) operates on a peer-to-peer network that's decentralized and can take over Windows PCs (Windows 95, 98, Me, 2000, XP, Vista, 7, 8 and Windows Server 2003, 2008, 2008 R2 and 2012).
GOZ typically infects a machine via a phishing attack and other bogus emails.
U.K.'s National Crime Agency put the botnet in simple terms:
Action taken by the NCA to combat the threat will give the UK public a unique, two-week opportunity to rid and safeguard themselves from two distinct but associated forms of malware known as GOZeuS and CryptoLocker.
Members of the public can protect themselves by making sure security software is installed and updated, by running scans and checking that computer operating systems and applications are up to date.
The NCA’s alert is part of one of the largest industry and law enforcement collaborations attempted to date. Activity in several countries, led by the FBI in the US, has weakened the global network of infected computers, meaning that action taken now to strengthen online safety can be particularly effective.
Meanwhile, the NCA reckons that more than 15,500 computers in the UK are already infected.
According to U.S.-CERT, GOZ infected machines can participate in attacks, send spam and swipe user data. To prepare, U.S.-CERT recommended that antivirus software is used and maintained, passwords are changed and patches are updated.