Google quintuples maximum bug bounty to $20,000

Google today announced it is rolling out updated rules for its Vulnerability Reward Program, in celebration of the program's recent anniversary. These include new reward amounts for the various bugs security researchers disclose. In fact, the company is more than quintupling the maximum amount from the previous top reward of $3,133.70, which the company announced in July 2011.
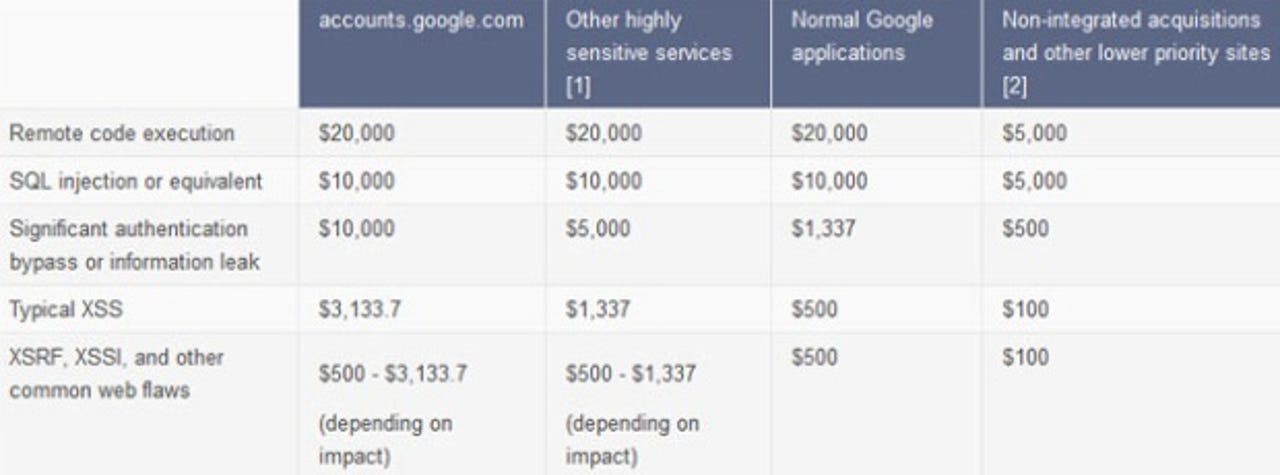
Here are three of the new reward amounts Google chose to highlight (the full table is embedded above):
- $20,000 for qualifying vulnerabilities that the reward panel determines will allow code execution on our production systems.
- $10,000 for SQL injection and equivalent vulnerabilities; and for certain types of information disclosure, authentication, and authorization bypass bugs.
- Up to $3,133.7 for many types of XSS, XSRF, and other high-impact flaws in highly sensitive applications.
There aren't just bounty increases in the new rules. Google has also implemented reduced rewards for vulnerabilities discovered in non-integrated acquisitions, for lower risk issues, and where the potential risk to user data is significantly smaller.
Google says this move will "help focus the research on bringing the greatest benefit to our users." The search giant gave the example of likely issuing a higher reward for a cross-site scripting vulnerability in Google Wallet than one in Google Art Project.
Mountain View also took the opportunity to say that it has so far received over 780 qualifying vulnerability reports that span across the hundreds of Google-developed services, as well as the software written by 50 or so companies it has acquired. In just over a year, the program has paid out around $460,000 to roughly 200 individuals.
See also:
- CanSecWest Pwnium: Google Chrome hacked with sandbox bypass
- Google patches 14 high-risk Chrome browser holes
- Google Chrome gets another security makeover
- Google shells out $10,000 to fix 10 high-risk Chrome browser flaws
- Google Chrome gets last-minute bandaid before Pwn2Own
- With Pwn2Own looming, Mozilla and Google ship browser patches