Google to introduce warnings for potentially hackable sites
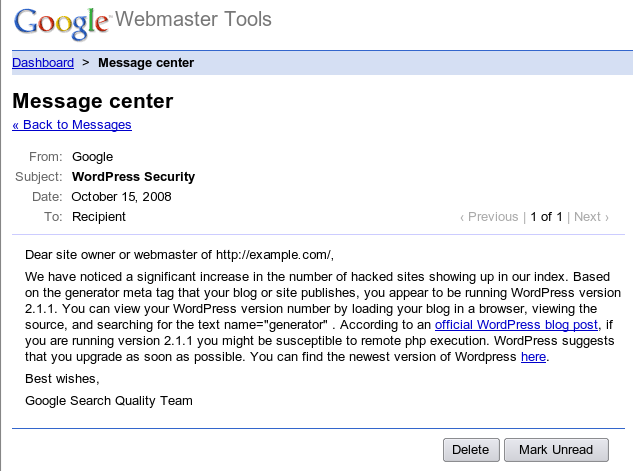
"Recently we've seen more websites get hacked because of various security holes. In order to help webmasters with this issue, we plan to run a test that will alert some webmasters if their content management system (CMS) or publishing platform looks like it might have a security hole or be hackable. This is a test, so we're starting out by alerting five to six thousand webmasters. We will be leaving messages for owners of potentially vulnerable sites in the Google Message Center that we provide as a free service as part of Webmaster Tools.
One of the most popular pieces of software on the web is WordPress, so we're starting our test with a specific version (2.1.1) that is known to be vulnerable to exploits. If the test goes well, we may expand these messages to include other types of software on the web."
Whereas the upcoming feature is a great proactive measure, WordPress isn't necessarily the blogging platform of choice for the majority of cybercriminals and blackhat search engine optimizers looking for efficient ways to acquire traffic. In fact, the current tools and tactics that they take advantage of, attempt to inject their presents onto each and every known to be remotely exploitable web application. This automated approach often building hit lists through search engines reconnaissance, is many steps ahead of Google's anticipated feature, so if they truly want to slow down the automated reconnaissance process, they could easily start challenging these automated crawlers.
In May, Google introduced the Safe Browsing diagnostic as a reactive response to the increasing number of web sites hosting or redirecting to malware, so the key to providing value to webmasters using the new warnings feature, would be to diversify the list of vulnerable web applications, and perhaps most importantly - emphasize and point out to related tools and services aiming to allow webmasters to self-audit their web sites.