Hackers claim they can now jailbreak Apple's T2 security chip

By combining two exploits initially developed for jailbreaking iPhones, security researchers claim they can also jailbreak Macs and MacBook devices that include Apple's latest line of T2 security chips.
While exploitation is still pretty complex, the technique of combining the two exploits has been mentioned on Twitter and Reddit over the past few weeks, having been tested and confirmed by several of today's top Apple security and jailbreaking experts.
With @checkra1n 0.11.0, you can now jailbreak the T2 chip in your Mac. An incredible amount of work went into this and it required changes at multiple levels.
— Jamie Bishop (@jamiebishop123) September 22, 2020
There’s too many people to tag, but shoutout to everyone who worked on getting this incredible feature shipped.
checkm8 + blackbird and the T2 SEP is all yours...
— Siguza (@s1guza) September 5, 2020
If exploited correctly, this jailbreaking technique allows users/attackers to gain full control over their devices to modify core OS behavior or be used to retrieve sensitive or encrypted data, and even plant malware.
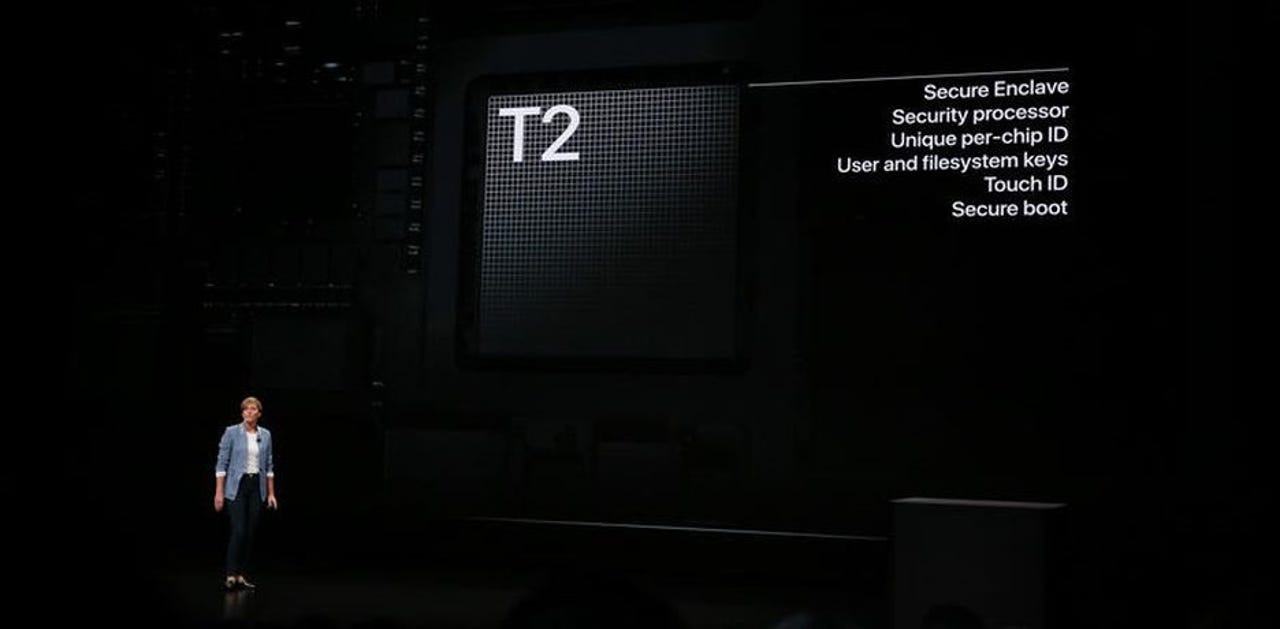
What are T2 chips?
For Apple users and ZDNet readers that are not aware of what T2 is, this is a special co-processor that is installed alongside the main Intel CPU on modern Apple desktops (iMac, Mac Pro, Mac mini) and laptops (MacBooks).
T2 chips were announced in 2017 and began shipping with all Apple devices sold since 2018.
Their role is to function as a separate CPU, also known as a co-processor. By default, they handle audio processing and various low-level I/O functions in order to help lift some load off the main CPU.
However, they also serve as a "security chip" —as a Secure Enclave Processor (SEP)— that processes sensitive data like cryptographic operations, KeyChain passwords, TouchID authentication, and the device's encrypted storage and secure boot capabilities.
In other words, they have a significant role in every recent Apple desktop device, where the chips underpin most security features.
How the jailbreak works
Over the summer, security researchers have figured out a way to break T2s and found a way to run code inside the security chip during its boot-up routine and alter its normal behavior.
The attack requires combining two other exploits that were initially designed for jailbreaking iOS devices — namely Checkm8 and Blackbird. This works because of some shared hardware and software features between T2 chips and iPhones and their underlying hardware.
According to a post from Belgian security firm ironPeak, jailbreaking a T2 security chip involves connecting to a Mac/MacBook via USB-C and running version 0.11.0 of the Checkra1n jailbreaking software during the Mac's boot-up process.
Per ironPeak, this works because "Apple left a debugging interface open in the T2 security chip shipping to customers, allowing anyone to enter Device Firmware Update (DFU) mode without authentication."
"Using this method, it is possible to create an USB-C cable that can automatically exploit your macOS device on boot," ironPeak said.
This allows an attacker to get root access on the T2 chip and modify and take control of anything running on the targeted device, even recovering encrypted data.
Danger to users
The danger regarding this new jailbreaking technique is pretty obvious. Any Mac or MacBook left unattended can be hacked by someone who can connect a USB-C cable, reboot the device, and then run Checkra1n 0.11.0.
The news isn't especially great for travelers during security checks at border crossings or for enterprises that employ large fleets of Macs and MacBook notepads, all of which are now exposed to attacks and having their secrets pilfered in classic evil maid attacks.
However, the new jailbreaking method also opens the door for new law enforcement investigation tools that could allow investigators to access suspects' Macs and MacBooks to retrieve information that would have been previously encrypted.
Unpatchable
Unfortunately, since this is a hardware-related issue, all T2 chips are to be considered unpatchable.
The only way users can deal with the aftermath of an attack is to reinstall BridgeOS, the operating system that runs on T2 chips.
"If you suspect your system to be tampered with, use Apple Configurator to reinstall bridgeOS on your T2 chip described here. If you are a potential target of state actors, verify your SMC payload integrity using .e.g. rickmark/smcutil and don't leave your device unsupervised," ironPeak said.
Apple did not return a request for comment.