Hackers turn China security report into Trojans

Hackers have embedded viruses into a security report which linked the Chinese army to cyberattacks on U.S. companies, infecting computers that download digital versions of the 60-page report.
When downloaded, the tainted versions would allow hackers to remotely control infected computers after users attempted to read the report which was released last week by U.S. IT security vendor, Mandiant.
A blog post by Symantec said hackers used the report as "bait", embedding a malware called, Trojan.Pidief, into fake reports which displayed a blank PDF document when opened. Unbeknownst to users, the tainted report would trigger the exploit code for Adobe Acrobat and Reader Remote Code Execution Vulnerability.
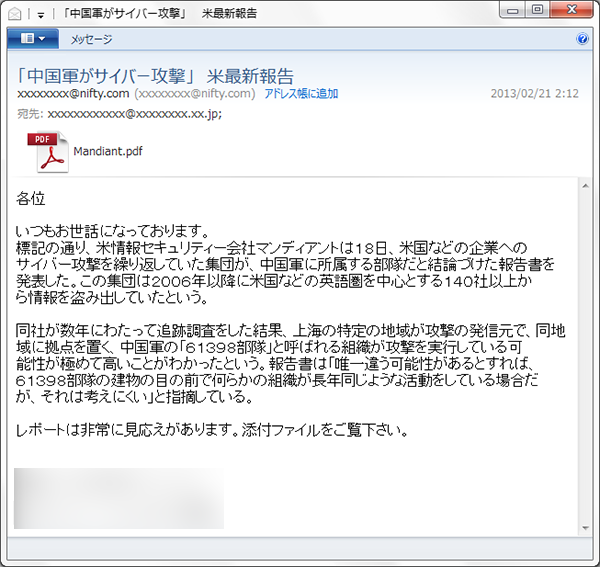
Symantec highlighted an e-mail in Japanese purported to be from someone in the media industry which contained a PDF attachment of the fake Mandiant report.
In its report, Mandiant pointed to a 12-storey building in Shanghai, China, which it claimed was operated by a government-sponsored online epionage group. Known as APT1, the hacker group had targeted U.S. businesses and government organizations, the security vendor said, noting that the high number of APT1 IP addresses "betrays the true location and language of the operators".
The Chinese Ministry of Defence had refuted the claims and called out the report for lacking any technical basis to conclude the source of attacks were from China.