Hacktivists stole 100 million records in 2011

The data comes from Verizon's 80-page "2012 Data Breach Investigations Report" (DBIR, PDF). Here's the relevant excerpt:
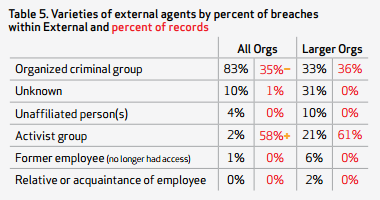
The most significant change we saw in 2011 was the rise of "hacktivism" against larger organizations worldwide. The frequency and regularity of cases tied to activist groups that came through our doors in 2011 exceeded the number worked in all previous years combined. But this was not restricted to our caseload alone; the other organizations participating in this report also spent a great deal of effort responding to, investigating, and prosecuting hacktivist exploits. It was extremely interesting to piece these different perspectives together to form a global view of investigations into activist groups and their victims. 3% of all external attacks may not seem like much (though remember we're dealing with over 850 incidents here, and notice related motives are higher than that; plus we suspect some "unknown" agents are actually activists), but this trend is probably the biggest and single most important change factor in this year's DBIR.
That is not to say that hacktivsm is new; the term has been standard lexicon since it was coined by the Cult of the Dead Cow hacker collective in the late 90’s. Back then, it mostly consisted of website defacements, coordinated denial of service attacks, and other antics to express disagreement, obtain bragging rights, or "just because." The major shift that occurred in 2011 was that activist groups added data breaches to their repertoire with much heightened intensity and publicity. In other words, 2011 saw a merger between those classic misdeeds and a new "oh by the way, we're gonna steal all your data too" twist.
But even that's not the whole story. Although activist groups accounted for a relatively small proportion of the 2011 caseload, they stole over 100 million records. That's almost twice the amount pinched by all those financially-motivated professionals we discussed earlier. So, although ideological attacks were less frequent, they sure took a heavy toll.
The report is based on security-breach investigations conducted by the Australian Federal Police, The Dutch National High Tech Crime Unit, the Irish Reporting and Information Security Service, the Police Central e-Crime Unit, and the United States Secret Service.
"We welcome these collaborators and firmly believe the more data we can share with the industry, the better we can understand and prepare for the threats we collectively face," a Verizon spokesperson said in a statement. "As always, the DBIR includes only confirmed data breaches worked either by Verizon or one of the aforementioned agencies. We believe that with each passing year, the data grows and evolves helping to paint a more complete picture of the current state of cybercrime."
See also: