How to secure consumer gadgets in the workplace

Preventing a security meltdown when staff bring their own laptops and phones to work
The era when the IT department decided which laptops and phones workers would use in the office is ending: today employers are starting to embrace the idea that staff should be able to use their own laptops and smartphones in the workplace.
As many as a quarter of employers in the UK run bring-your-own computing schemes, where staff are given allowances or discounts to buy their own computers or phones to use in their day job, while employees in many other organisations will be using their own hardware to access work systems or store company data, whether the CIO likes it or not.
Allowing workers to use their personal devices at work has its risks, ranging from letting viruses and data-stealing trojans inside the corporate network to letting sensitive data out.
Dr Richard Clayton, security researcher at Cambridge University, warned that consumer tech poses a malware threat to businesses, as consumers are often less diligent than corporate IT managers at updating their antivirus suite and patching their software against the latest vulnerabilities.
"About one in 20 machines have something bad on them and almost none of their owners are aware that their machines are infected," he said.
"In an organisation where all of the defences are around the edges of the corporation once you get a breach then the thing runs wild because there's almost no protection inside."
Bringing consumer machines into the workplace also increases the chance of corporate data loss - as staff carry sensitive corporate data around with them on their personal laptops and smartphones, theres an increased risk of that data falling into the wrong hands if the device is lost or stolen.
"If someone loses their laptop, an individual might just go and buy another one and not tell anyone, and the IT manager has no way of knowing that the data has been lost," said Guy Bunker, security consultant and member of the security user group the Jericho Forum.
Once sensitive data is outside of the company firewall, the organisation has lost control of where that data might end up.
For example, today there are many services that allow consumers to back-up their data in the cloud - where data is copied to a third party's datacentre and is accessible over the internet.
If a member of staff backs up corporate data using a cloud service, the organisation's IT department has no way of checking whether the third party can be trusted not to access or share that data.
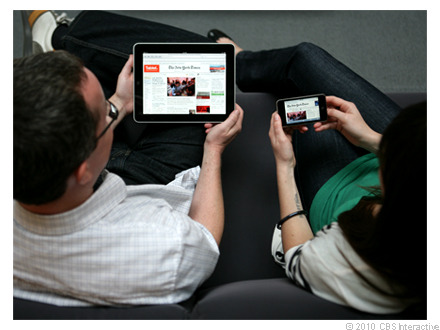
Consumer devices like the Apple iPad and iPhone are increasingly finding their way into the workplace
(Photo credit: Josh P. Miller/CNET)
How to secure consumer devices in the workplace
Fortunately none of the security issues surrounding the consumerisation of IT are insurmountable - an organisation can make consumer devices as secure as those bought in-house by putting the right security policies and technologies in place.
"The mantra is don't do anything you wouldn't do normally," Bunker said.
"Look at your audit and compliance and security and data loss prevention requirements and say 'Can I make sure that the consumer devices will be as secure as if I own the hardware myself?'
"If you can't guarantee that then think again - it doesn't mean that you can't do this because we know that some huge companies already do do consumerisation of IT.
"It just means sitting back and thinking 'I need to make sure that when they get their machines there's a security stack on it which I can audit against'."
See page two for tips on how to secure a corporate network when letting staff choose their own machines at work.
Key steps that organisations can take to secure consumer tech are:
Install a security suite on the consumer device
Putting a security software suite on the consumer device - be it mobile computer or smartphone - allows the IT department to audit its OS and applications in order to check that its software is secure.
The security suite will ensure that the device's antivirus protection is up to date, that software and web browser plug-ins have been patched and that programs that conflict with corporate use policies are not installed.
Scan all traffic on the corporate network for malware
Given the uncertainty over the software that employees will install or the websites they will browse on their own device, an organisation going down the consumerisation route should scan all traffic passing into the corporate network for rogue code. A simple antivirus product that scans for malware code signatures should be installed at the gateway to the corporate network.
Implement password protection and storage encryption
Password-protecting consumer devices will make it more difficult for third parties to get access to corporate data if those devices are lost or stolen.
Creating an encrypted partition on the consumer device's storage will also provide an area where the employee can securely store sensitive corporate data.
Sensitive information can be kept secure on consumer devices
(Photo credit: Shutterstock)
Bring in acceptable use policies
Organisations should lay down ground rules spelling out how staff can use the machine inside or outside or work, Bunker said - for instance, setting out what types of data should not be saved to the device, what types of websites should not be browsed and who else should be allowed to use the device.
Install data loss prevention technologies
By installing data loss prevention (DLP) technologies within the corporate network, an organisation can help ensure that sensitive data is not likely to be stolen from consumer devices, Bunker said.
DLP monitors data that is stored on the corporate network, performing functions such as making sure that sensitive data is not copied to unencrypted storage or that data can't be copied to removable media such as memory sticks or DVDs.
Start using virtual desktops
One way for organisations to retain centralised control over the security of data and the integrity of the corporate network, while still allowing staff to use their own computers and smartphones, is by using virtual desktops.
Virtual desktops are basically made up of an operating system and software applications that are run on a secure centralised server and then streamed across a secure network connection to the employee's smartphone or PC.
The organisation can build all of the security safeguards necessary to protect the corporate network and data into the virtual machine - everything from data loss prevention technologies to up-to-date security software suites.
Whenever staff want to access the corporate network they can access all of their data and corporate software by connecting to the virtual desktop, which has all of the necessary security built-in.
Virtual desktops can also be set up so that employees cannot save corporate data to their device, helping to ensure that data stays on the organisation's servers.
Use digital rights management to protect corporate data
Digital rights management (DRM) may be more familiar to consumers as copy protection on film or music downloads, but it can also be used by organisations to protect data stored on employee's personal devices, Bunker said.
DRM technologies allow data to be modified to set which corporate users have access to that data and over what time period.
When a member of staff leaves the company or loses a device containing that data, the IT manager can then remove that person's rights to access that corporate data - minimising the chances of it falling into the wrong hands.