How was this Windows Store app able to download adware to a Windows 10 PC?

One of the biggest selling points of the Windows Store is its promise of safety. Apps have to be approved to make it into the store, and the sandbox in which apps run should prevent them from causing any damage or installing malware or unwanted software.
That doesn't mean developers can't try shady tricks. But their options are extremely limited, which is why I was surprised to find an app in the Windows Store last week that actually succeeded in downloading adware to a Windows 10 PC.
An unsophisticated user might have been fooled into going one step further and running that software, resulting in the installation of an annoying piece of adware and potentially much worse.
I had used the app, a bare-bones BitTorrent client called Torrenty, on a different PC several months ago but hadn't tried it recently. After installing the current version from the Store, I was surprised to see this curious message at startup:
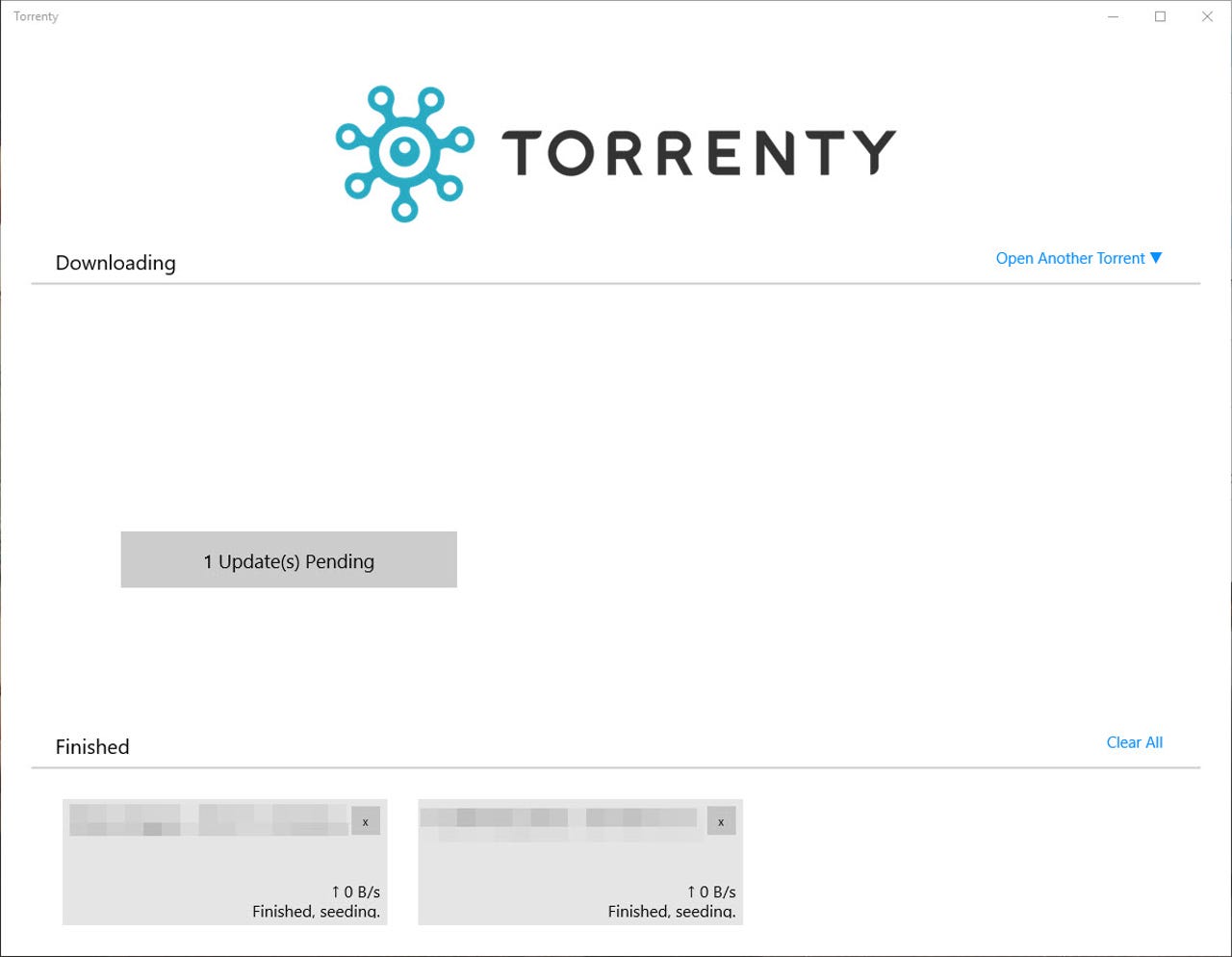
Clicking that official-looking update button immediately begins an untrusted download
That "1 Update(s) Pending" message doesn't look like an ad; it appears to be part of the user interface. Clicking that button opened a web page that immediately tried to download a program called Setup.exe.
With Microsoft Edge set as the default browser, the software downloaded in a matter of seconds, with a Run button appearing at the bottom of the browser window.
Both Microsoft Edge and Google Chrome allowed a potentially dangerous download
Google Chrome downloaded a variant of the Setup file without complaint, leaving it in the Downloads folder with a shortcut at the bottom of the Chrome window, ready to run.
With Firefox set as the default browser, that web page led to a different destination:
Mozilla Firefox (using Google's Safe Browsing service) blocked the download
That Setup program could have installed anything, including ransomware or a password-stealing keylogger. As it turned out, the threat was relatively mild: a free BitTorrent client called BitLord (a Windows desktop program) wrapped in an adware downloader.
A Virustotal analysis found that 24 of 56 antivirus scanners detected the file as a potentially unwanted program or adware, with several specifically calling out the offender, Download Assistant.
The unwanted software that it tried to install is a cross-platform (OS X and Windows) browser add-in, PremierOpinion, which reportedly delivers pop-up surveys and places unwanted ads in the browsers it's attached to. When you search for that product name in Google, the first three results are instructions for removing the software.
Google's Safe Browsing service offers this Site Status report for ezsoftdownloads.com, which includes a blood-red exclamation point icon, followed by the word Dangerous, also in blood-red type. The description matter-of-factly reports that the site "send[s] visitors to dangerous websites" and that "[s]ome pages on this website install malware on visitors' computers."
If you try to visit ezsoftdownloads.com in a web browser, you'll get nowhere. The domain appears to be set up exclusively to host shady downloads.
The Safe Browsing report also notes, "Dangerous websites have been sending visitors to this website, including backbacon.co." That was the destination of the original URL called from the Windows Store app. The Backbacon home page merely says it's a "web service," with no additional details and only an email link "for more information." A third-party security service traces Backbacon to servers hosted at Amazon Web Services. The domain itself is registered using a proxy service, so there's no easy way to track down its owner
Via Twitter, a reader named raylee supplies this snippet of code from the app, suggesting that Backbacon is an underground ad network that displays sketchy content in the space where ads would normally appear and then redirects clicks, in this case (and at least two others) to executable files.
Ironically, Firefox was able to use Google's Safe Browsing service to block the dangerous site, but the URL in the Windows Store app included a custom link for Chrome, which allowed the adware to avoid detection.
This is depressingly familiar behavior for random web searches, where this category of misleading software routinely shows up in search results.
But it's not supposed to happen from a sandboxed and supposedly screened app from the Windows Store.
I reported the app to a contact at Microsoft and it was removed from the Windows Store almost immediately. Its listing page is still in place, for now, with almost 2400 reviews giving the app high marks overall.
This sort of behavior is difficult to stop, of course. Apps can launch web links, which in turn can redirect to content that wasn't there during the original app approval process. The effort would be pointless on iOS or Android (or, ahem, Windows RT), which allow execution of code only from trusted sources. But the desktop operating systems, Windows and OS X, which have app stores but also allow executables from other sources, can't easily prevent a web link from jumping out of the sandbox and onto the user's desktop.
That possibility, which one hopes is remote, is still worth noting and training users to be aware of.
Reached for comment, a Microsoft spokesperson replied: "Microsoft has a thorough review process for app submissions, based on a strict set of certification requirements. No approach is perfect, so we encourage people to report any issues they may encounter with Windows Store. For most issues, customers can use the "report concern to Microsoft" link in the Store. For infringements concerns, people can use our online tools or email reportapp@microsoft.com directly."