IE9 and Tracking Protection: Microsoft disrupts the online ad business

The more closely I look at the new Tracking Protection feature in Internet Explorer 9, the more astonished I am that it came from one of the world’s largest corporations.
If Internet Explorer 9 becomes widely adopted and if Tracking Protection is widely used—and those are two tricky assumptions—it has the potential to seriously disrupt the online advertising business. Microsoft made this feature widely available last week in the Release Candidate build of IE9 (if you missed it, here's my review of the IE9 RC). Using the RC, it takes exactly two clicks to download a Tracking Protection List (TPL) and begin blocking third-party cookies, tracking pixels, web beacons, hit counters, analytics scripts, and other tools of the modern web designed to assemble a profile of your movements and activities on the web.
Oh, and it blocks ads, too.
In this post, the first in a series, I’ll show how Tracking Protection works. I’ve also put together a screenshot gallery that shows the entire sequence of actions and includes some tips on how to manage Tracking Protection Lists.
Screenshot gallery: Using Tracking Protection Lists in IE9
Part 2: Privacy protection and IE9: who can you trust?
The underlying idea behind Tracking Protection isn’t new. Third-party tools and extensions have been adding similar privacy-protecting features to web browsers for a long time, usually in the form of a browser extension, add-on, or plug-in. Adding this feature into the browser itself, however, as Microsoft has done, is a first.Here’s how Microsoft’s solution works:
1. Someone—anyone—creates a list of domains and substrings that they want to block (or allow) as third-party content on a web page.
2. The author formats that list using Microsoft’s Tracking Protection List specification and posts it on the web.
3. Someone—anyone—creates a link to the URI for that list, using a short snippet of JavaScript. The link does not have to be on the same web server where the TPL itself is hosted.
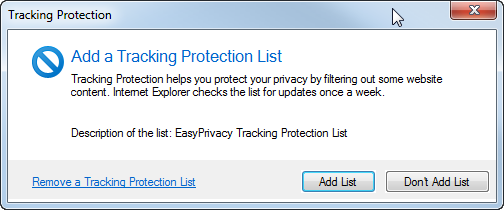
4. An IE9 user clicks that link, which brings up a dialog box like this one:
5. The IE9 user clicks Add List, which copies the formatted file to a system folder and configures IE to immediately begin using the rules contained on that list.
From that point on, IE9 checks the TPL before sending an HTTP request to a third-party site. Here’s a simplified example, with a page that includes an advertisement and a tracking pixel from two third-party sites.
Because xyz-ads.com is on the Block list, no request is sent to its server and the space where the ad should go remains blank. But abc-analytics is on an Allow list, so that request goes through. XYZ Ads is out of luck. It didn’t get to serve an ad, and it didn’t gather any information from the visitor. ABC Analytics, on the other hand, gets its tracking database updated.
Here are a few other facts worth knowing about Tracking Protection:
- TPLs affect third-party content only and are ignored for direct requests. If example.com is on a Block list, IE9 will reject any third-party requests to that domain but will serve up the page normally if you go to a page that is hosted directly on the example.com domain.
- You can install multiple Tracking Protection lists and enable or disable any list at any time. You can also remove a list.
- From the Manage Add-ons dialog box in IE9, you can inspect the contents of any Tracking Protection List and copy it to a text file.
- TPLs include an auto-update mechanism. The default update period is 7 days, but a list publisher can set this value to any interval between 1 and 30 days.
- If you have multiple lists, IE9 uses a hierarchy to resolve conflicts. Allow rules trump Block rules. Thus, if the same domain or substring is on one list with a Block entry and another with an Allow entry, third-party content from that domain will be allowed.
- If you use a Personalized Filtering List in Manual mode, its settings override any entry on a TPL.
Currently, five TPLs from four organizations are available for IE9 users (I expect this number to rise as more groups discover its possibilities). I’ve taken a close look at all five of these lists, For the surprising details, see Part 2: Privacy protection and IE9: who can you trust?.