Is Mozilla's Firefox 'click-to-play' feature a sound response to drive-by malware attacks?
According to a blog post by Mozilla's software engineer Jared Wein, Mozilla plans to introduce 'click-to-play' feature in upcoming versions of their flagship Firefox browser.
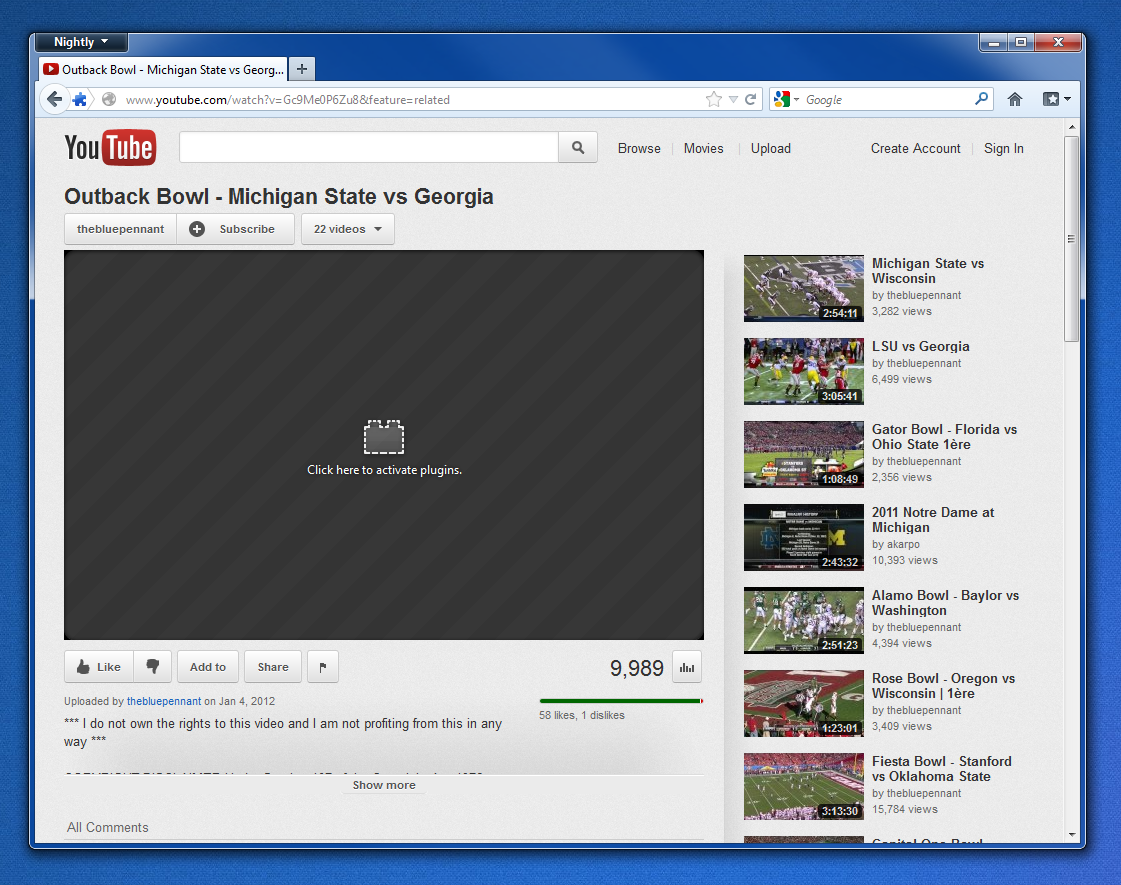
The feature -- available to NoScript users for years -- aims to prevent the systematic exploitation of browser plugin based client-side exploitation campaigns, by allowing end users to choose whether they would want to active content to load in the first place.
A logical question emerges - is this a sound response to preventing the currently ubiquitous exploitation of client-side vulnerabilities on end and corporate PCs, especially in times when the average user is running a number of remotely exploitable third-party applications and browser plugins?
Not necessarily. How come? Pretty simple.
Basically, what Mozilla's 'click-to-play' feature really does, is slowing down the systematic exploitation of client-side vulnerabilities, not preventing it. On the majority of occasions, drive-by malware attacks are launched with a social engineering element in an attempt to increase the probability for a successful infection.
Cybercriminals entice end users and provoke end user interaction by promising something in return for clicking on the malicious link found found in spamvertised emails. If the end user originally clicked on a link promising him a video clip, access to personal data, notification, or verification email, Firefox's 'click-to-play' feature will only slow down the exploitation process, as the end user will eventually enable the showing of active content in an attempt to access the promised content.
Moreover, as we've seen in the past, cybercriminals are masters of visual social engineering, successfully impersonating well known brands, consumer products, and product features, such as for instance Firefox's security alert, and SafeBrowsing initiative's warning page. It would take long before they start mimicking Mozilla's 'click-to-play' feature, offering additional advice to users for enabling it in order to view the promised content.
What do you think? Is Mozilla's 'click-to-play' feature a sound response to preventing drive-by malware attacks? Or are social engineering elements embedded in these campaigns undermining the usability of Mozilla's feature?
Talkback.