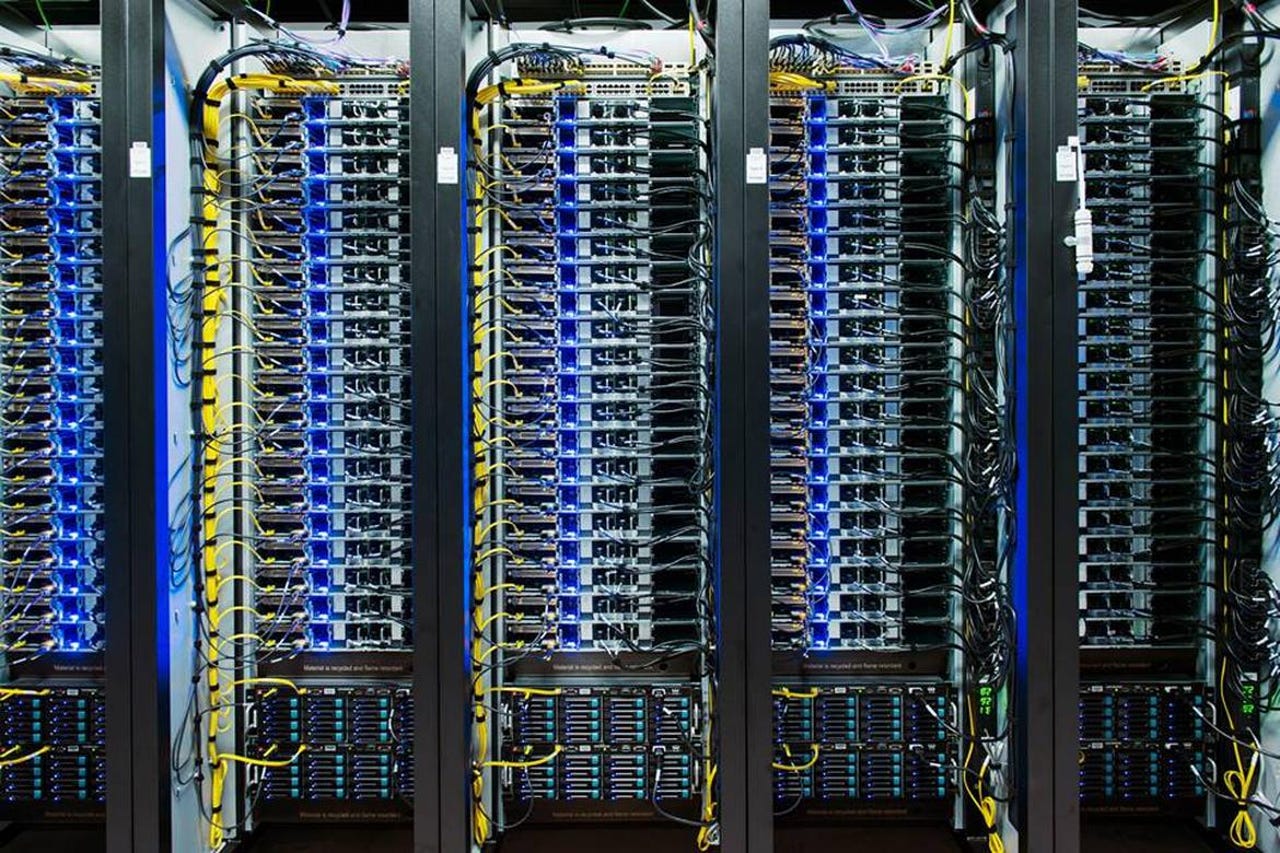
'Largest' denial-of-service attack hit Asian datacenter this year

The largest ever distributed denial-of-service (DDoS) attack happened earlier this year, according to a threat intelligence and monitoring service.
Internet of Things
Arbor Networks said the attack had traffic of up to 334 Gbps, accounting for tens of thousands of connections, targeting one Asian network operator.
DDoS attacks are commonplace nowadays: activists and hackers often target a website or company with a flood of traffic, bringing their systems to a halt. But it's rare to see an attack driving so much traffic.
These attacks leverage a technique that amplifies the traffic attackers generate through hijacking computers' bandwidth, while at the same time masking the source of the attack. These attacks are typically shorter in length -- around 90 percent last less than an hour. But they pack a punch.
These kinds of attacks are increasingly common, the company said. During the three-month period there were just 25 attacks larger than 100 Gbps in size, marking an increase in how these kinds of attacks occur.
But the company said that the majority of these attacks could be mitigated with network filters, which block traffic from spoofed addresses.
"Attacks that are significantly above the 200Gbps level can be extremely dangerous for network operators and can cause collateral damage across service provider, cloud hosting and enterprise networks," said Arbor Networks' Darren Anstee in remarks.