Lenovo says Superfish not a 'security concern', own advisory marks it highly severe

Sacrificing one of the core pillars of its devices' security chain for ad revenue was all in an effort to allow users to "discover interesting products while shopping", a Lenovo statement said in response to the Superfish furore.
Lenovo said that Superfish was shipped on its notebook devices between September and December 2014. In January, as a result of user feedback, the product was disabled by Superfish on its end, and Lenovo stopped preloading the software.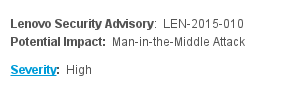
"We will not preload this software in the future," the Chinese hardware manufacturer said.
The company dismissed security concerns that Superfish was able to hijack SSL/TLS connections via a self-signing root certificate authority that had the same private key on each and every Lenovo device upon which Superfish was installed.
"We have thoroughly investigated this technology, and do not find any evidence to substantiate security concerns," Lenovo's statement said.
"We know that users reacted to this issue with concern, and so we have taken direct action to stop shipping any products with this software. We will continue to review what we do and how we do it in order to ensure we put our user needs, experience, and priorities first."
However, a security advisory published by Lenovo rated the incident as highly severe.
"Superfish intercept HTTP(S) traffic using a self-signed root certificate. This is stored in the local certificate store and provides a security concern," the advisory said.
The advisory also revealed the model numbers for notebooks that suffered from having Superfish preloaded:
- E-Series: E10-30
- Flex-Series: Flex2 14, Flex2 15, Flex2 14D, Flex2 15D, Flex2 14 (BTM), Flex2 15 (BTM), Flex 10
- G-Series: G410, G510, G40-70, G40-30, G40-45, G50-70, G50-30, G50-45
- M-Series: Miix2 - 8, Miix2 - 10, Miix2 - 11
- S-Series: S310, S410, S415; S415 Touch, S20-30, S20-30 Touch, S40-70
- U-Series: U330P, U430P, U330Touch, U430Touch, U540Touch
- Y-Series: Y430P, Y40-70, Y50-70
- Yoga-Series: Yoga2-11BTM, Yoga2-11HSW, Yoga2-13, Yoga2Pro-13
- Z-Series: Z40-70, Z40-75, Z50-70, Z50-75
It took mere hours, once the Superfish flaw was known, for the Superfish private key to be extracted by security expert Robert Graham.
"The consequence is that I can intercept the encrypted communications of SuperFish's victims (people with Lenovo laptops) while hanging out near them at a cafe Wi-Fi hotspot," he said.
For a significant breakdown of the Windows security chain that left users vulnerable to man-in-the-middle attacks, Lenovo revealed that it didn't receive a major payday to take such action.
"The relationship with Superfish is not financially significant; our goal was to enhance the experience for users," Lenovo said.
Soon after the SSL hijacking behaviour of Superfish was revealed, client-side instructions to remove Superfish from Lenovo devices were pieced together.
For web developers and administrators worried that Lenovo users may still be using Superfish self-signed certificates on their sites instead of the proper SSL certificates they should be using, Glip has published instructions to prevent Superfish from running with a single HTML meta tag.
In an interview with The Wall Street Journal, Lenovo CTO Peter Hortensius said that security concerns raised by Superfish are "theoretical concerns".
"We have no insight that anything nefarious has occurred," he said. "Our reputation is everything, and our products are ultimately how we have our reputation."
Microsoft told ZDNet in a statement that it is "looking into reports on this third-party issue".