LinkedIn will pay $1.25 million to settle suit over password breach

LinkedIn has agreed to pay $1.25 million to settle a class-action suit that alleged the company failed to protect the passwords and private information of its premium subscriber customers.
The case dates back to June 2012 when the company reported that Russian hackers stole more than six million passwords from the social networking site, about 5 percent of LinkedIn's user base. Shortly thereafter, a user launched a class-action lawsuit claiming LinkedIn violated its own user agreement and privacy policy.
The suit specifically pointed out that LinkedIn failed to salt the passwords before storing them. The salt adds a dimension to the hash that makes it more difficult to uncover the protected data. The suit also referenced preliminary reports that said hackers used an SQL injection attack, which lets hackers access databases via a Web site.
The settlement covers individuals and entities in the U.S. who paid for premium subscriptions between March 15, 2006 and June 7, 2012, which is about 800,000 Americans, according to a New York Times report.
Under the settlement terms laid out by Judge Edward J. Davila of the U.S. District Court for the Northern District of California plaintiffs are eligible to make a claim against the $1.25 million settlement fund, which will first pay out fees for the plaintiff's lawyers.
Plantiffs must apply to share in the settlement. The actual amount paid to each claimant will depend on the number of claims submitted.
And money left over after all payments have been satisfied will be donated to three nonprofit organizations: the Center for Democracy & Technology, the World Privacy Forum and the Carnegie Mellon CyLab Usable Privacy and Security Laboratory. If the amount to be paid to each plaintiff turns out to be less than $10 based on the number of claims, the settlement agreement may be revised.
In a statement, LinkedIn said it agreed to the settlement "to avoid the distraction and expense of ongoing litigation."
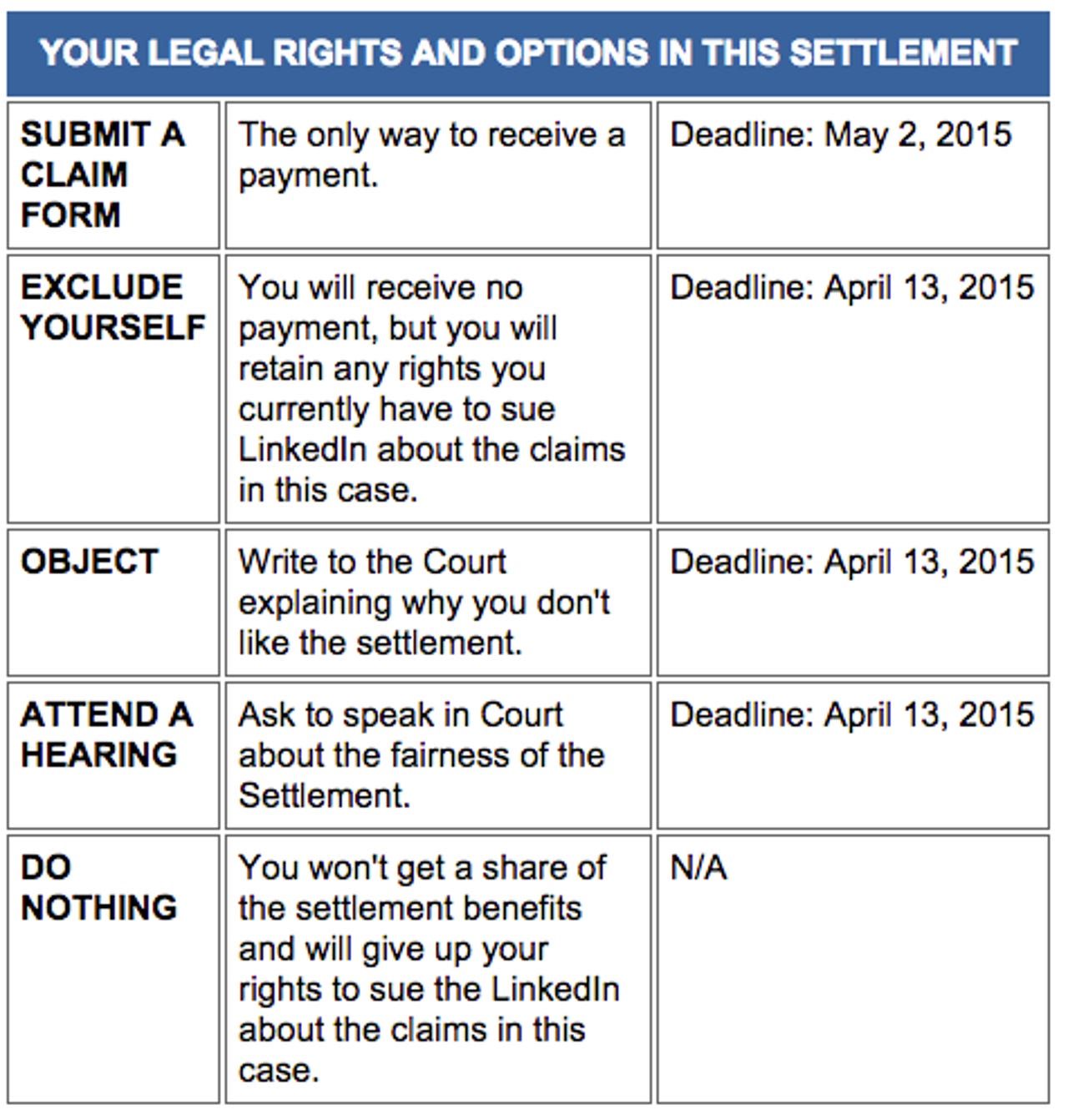
Plaintiffs have a number of options available as part of the settlement: