Linux-based Qubes OS sandboxes VMs for added security

Last week saw the release of Qubes, a Linux-based operating system that's aiming to make a virtue of sandboxed security.
The aim of Qubes, developed by Joanna Rutkowska and her Warsaw-based IT security company Invisible Things Lab, is to make it as hard as possible for rootkits and malware to install on a system by strictly dividing processes and running them in their own sandboxes. Most OSes have a monolithic kernel, something Rutkowska says is inherently insecure.
Rutkowska made tech headlines some years back after she and her team developed the Blue Pill rootkit. By placing the main operating system (the then newly released Windows Vista) in a virtualised environment, the rootkit could elude almost every type of security algorithm known at the time. While this is often touted as 'hardware hacking', Rutkowska finds that description inaccurate: the fault, she argues, is not directly in the hardware, but in the operating system putting all its eggs in one fat kernel.
In Qubes, processes can only access the parts of the system they are meant to access. All functions are divided into sandboxes (specifically, domains), which are lightweight virtual machines based on Xen. Each domain has its own coloured box, so users get a visualisation of the divisions in the processes they are running.
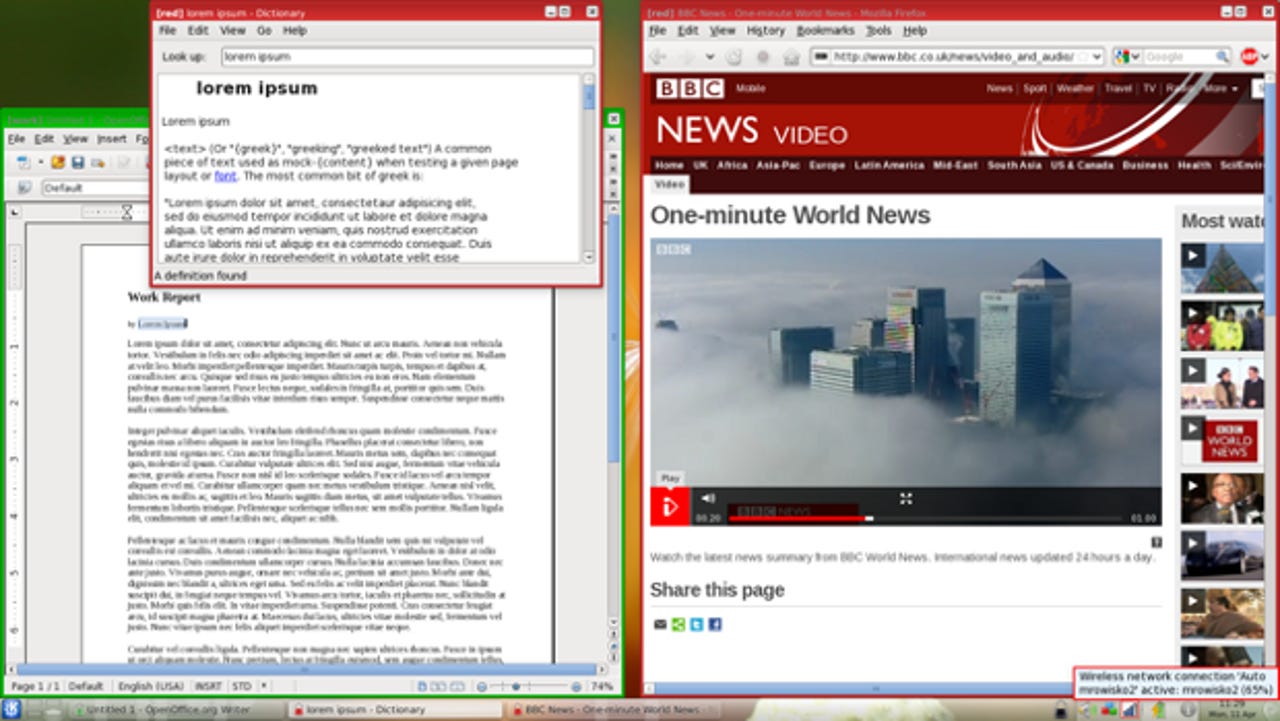
In simple terms (and this is all customisable), the effects of clicking on a harmful link are neutralised because all browser-based actions are performed in a browser domain that has very limited access to the backend, rather than an application domain that does offer such possibilities. To put it in Rutkowska's words: why should a game of Tetris have access to the kernel?
There is a price to be paid however, as Qubes is not exactly light on hardware requirements: even when the VMs are light and only run the processes they are meant to run, Qubes still demands 4GB of memory, a semi-x64 processor and 20GB of hard drive space.
Rutkowska stops short of calling her OS absolutely secure. "A hypothetical exploit for your favourite web browser would work against Firefox running inside one of the Qubes VMs just as well as it worked for the same browser running on normal Linux," she wrote on her blog. "The difference that Qubes makes is that this attacked browser might be just your for-personal-use-only browser, which is isolated from your for-work-use-only browser, and for-banking-use-only browser."
Road to Qubes
Developing Qubes took a bit longer than expected, with the release date for the stable version originally set for the end of 2011.
"It's easy to write a proof of concept for something," Rutkowska told Central European Processing, "and it's way more difficult to turn it into something actually usable for everyday work." Even then, Rutkowska tried to keep to the original plan as much as possible. "We tried to stick to the roadmap we more or less sketched three years ago when designing it."
The desktop OS is purely aimed at the business-to-business market. "Our current business model involves selling commercial licences for the Qubes code (otherwise released under GPL) to vendors, so that they could build their own customised products on top of Qubes, or customised, professional Qubes editions, targeting some specific target audiences," Rutkowska wrote.
Currently, Invisible Things Lab is working on Qubes 2.0, which should also have Windows extensions, making it possible to run Windows applications. "I already have a few Windows VMs running on my laptop. We should be publishing Qubes 2.0 'beta 1' sometime soon, I hope," Rutkowska said.