LulzSec disbands: Final cache includes AT&T internal data and 750,000 user accounts

Update: Title corrected. Thousand, not million. Too many zeros.
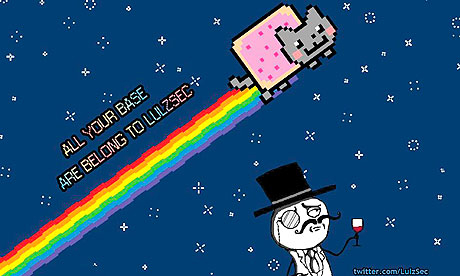
After fifty days of releasing vast caches of confidential data, from police units through to government departments, LulzSec announced on its Twitter feed this evening that it is to disband.
But it seems that LulzSec wasn't in it for the 'lulz' after all.
The problem for groups shrouding themselves in anonymity is that they can never truly gauge the public or press response to their actions.
Just as it was with Wikileaks and Anonymous, and the impact that 4chan and its crucial elements of anonymity have had on memes and popular culture, these viral constructs are unpredictable, difficult to manage and ultimately, all but impossible to maintain.
What is clear, however, that the supposed six that are mentioned in their press release as being the ones behind the subversive group have called it a day.
In a statement via its official Twitter feed this evening:
"Again, behind the mask, behind the insanity and mayhem, we truly believe in the AntiSec movement. We believe in it so strongly that we brought it back, much to the dismay of those looking for more anarchic lulz. We hope, wish, even beg, that the movement manifests itself into a revolution that can continue on without us.
The support we've gathered for it in such a short space of time is truly overwhelming, and not to mention humbling. Please don't stop. Together, united, we can stomp down our common oppressors and imbue ourselves with the power and freedom we deserve."
After delving into the latest release, around three quarters of a million usernames and passwords across a number of different sites have been hacked, collected and now disseminated to thousands of other users. These login accounts include details of the Battlefield Heroes game, as well as for the website Hackforums.net.
More usernames and passwords relate to the NATO Bookshop, for which the URL of the page now simply redirects to the NATO homepage. It is unclear whether these accounts relate to NATO operations or internal network access.
A screenshot appears to show evidence that a Navy website was hacked into and text replaced with LulzSec slogans. The user appears to be using Ubuntu Linux. Whether this makes a difference or not is unclear at this stage.
Also in this vast cache of data appear to be internal AT&T files, relating to its 4G LTE roll-out, as well as details of just over 90,000 IBM personal phones.
It does not appear any customer data from AT&T has been compromised.
Looking further into the cache, there are IP addresses for organisations such as Disney, EMI and Universal.
No doubt, many may feel cheated in this release. Without the shock and awe of previous torrented caches of hacked data, this release also includes a vast list of IP addresses with simple credentials of "root" and "password". It also includes AOL related data, which will mean little to so many.
There are, however, a few theories as to why they disbanded today.
Fifty days is a set milestone and they knew it from the start. Today is the birthday of George Orwell, who died in 1950, which may or may not be coincidental. However, considering the person running the Twitter feed, known as Topiary, is British and lives within the United Kingdom -- based not only on the writing style and the references to time zones -- it's unlikely that this is the case. It's now the 26th and the releases came at midnight.
Their identities have been compromised after a series of embarrassing confrontations between white hat versus black hat hackers. The spat has continued between the Jester and LulzSec after the Jester took down their website, along with other Pastebin posts which purport the names of key members of the hacktivist network. Plus, one alleged member of LulzSec, Ryan Cleary, is still in custody in England after his part in the hack on SOCA which means governments are hot on their tails.
They got bored and along with disorganisation, lacking expectations in media coverage, or a slow-down in Twitter followers as a way of gauging reaction that may have put them off their activities. It's possible that this is the case, but something just seems amiss about their recent activities. The Arizona police department leaks alone were far more damaging -- seemingly at least -- than the final cache released this evening.
The motions have already been put in place and it is for us, the general population, to take the reigns of #AntiSec into our own hands and revolt against our governments. Considering so many of us voted in our respective governments, it's unlikely that will happen.
What is interesting, however, is whether this will result in a domino effect in other parts of the world.
With revolutions fully in swing across North Africa and the Middle East, if LulzSec is trying to replicate the anti-government feeling across other parts of the world, this will most likely not succeed.
Unlike with Wikileaks, the diplomatic cables releases 'legitimised' the protests and ultimately the revolutions that occurred, by implicating nation states of wrongdoing by other, more democratic nations.
Whether the world can now breathe a sigh of relief, knowing that the group have disbanded -- at least publicly, it seems -- there is no doubt a group willing to perform very much the same functions, under a different name and a unique ideology.
Related content: