LulzSec hacks Military Singles

Lulz Security (LulzSec), a hacktivist group loosely associated with the hacktivist group Anonymous, is claiming responsibility for a hack exposing 170,937 accounts from dating website Military Singles. The accounts have been posted publicly and appear to have authentic credentials for logging into e-mail addresses hosted on military domains.
Here's what LulzSec had to say on PasteBin:
The website http://www.militarysingles.com/ was recently closed day ago or so, so we dumped email db There are emails such as @us.army.mil ; @carney.navy.mil ; @greatlakes.cnet.navy.mil ; @microsoft.com ; etc..
Total Dump 170937 Accounts.
Download : http://www.embedupload.com/?d=4DR1M2FVGT http://www.mirrorcreator.com/files/OOFIKKI6/military.rar_links
Someone claiming to be an administrator of Military Singles posted the following comment on Data Breaches:
We at ESingles Inc. are aware of the claim that someone has hacked MilitarySingles.com and are currently investigating the situation. At this time there is no actual evidence that MilitarySingles.com was hacked and it is possible that the Tweet from Operation Digiturk is simply a false claim.
We do however take the security and privacy of our members very seriously and will therefore treat this claim as if it were real and proceed with the required security steps in order to ensure the website and it’s database is secure.
Admin, MilitarySingles.com
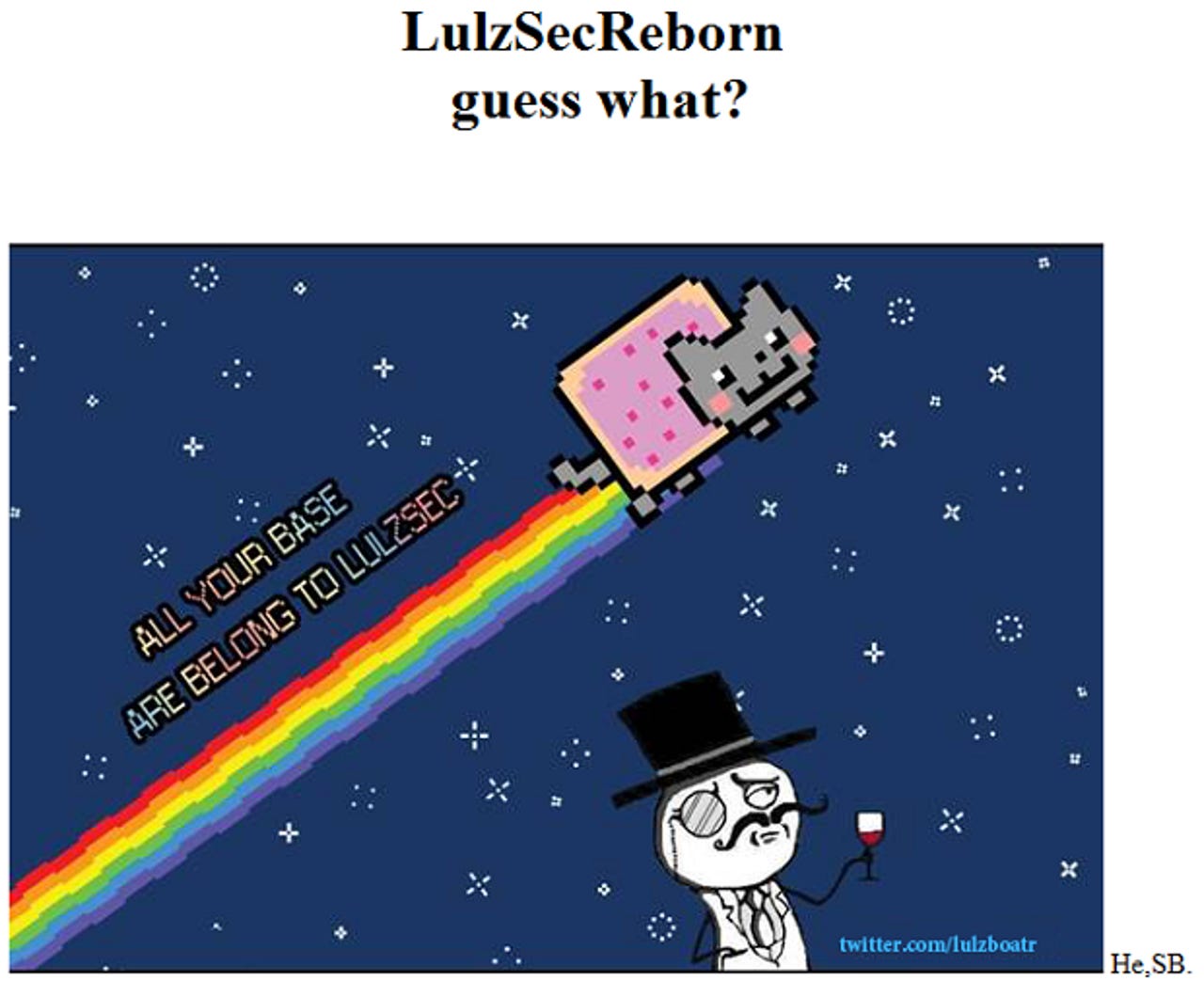
LulzSec responded by calling the administrator stupid and posting a message for all to see over at militarysingles.com/esvon/files/index.html (pictured above). This is a typical LulzSec move: demonstrating its access to a hacked website with a Nyan Cat signature.
If you know anyone who uses MilitarySingles.com, make sure they change their password on the site, as well as on any other service they may have used it. This includes any U.S. military websites.
Oh, and for those who told me I was wrong when I said LulzSec wasn't coming back on April Fools' Day as part of "Project Mayhem 2012", here's a quote from what I wrote last week:
Let me make something very clear before I attempt to debunk this one: LulzSec is still around. The group’s members are still very close to Anonymous and they haven’t gone anywhere. While the group did disband some nine months ago and while some of its members have been arrested, LulzSec’s members are still alive and well. The thing to remember is that if LulzSec does return, the group will do so in style, not via a video announcement that claims lots of things will start happening next month, followed by even more crazy things in nine months.
Now, here's what LulzSec Reborn said on Twitter:
wtf is project mayhem? #LulzSecReborn And so it started ... http://pastebin.com/JRY3cA5T @ODigiturk http://www.databreaches.net/?p=23736 Stupid Administrator "There is no evidence militarysingles is hacked" Well guess what?https://www.militarysingles.com/esvon/files/index.html About that bulls*** on 1st of April we don't know who is planning that...
The Twitter account lulzboatR already has some 1,000 followers. How long do you think it will be before it catches LulzSec, which has over 365,000 followers and hasn't tweeted since July 2011? Last time, LulzSec went on a hacking spree for 50 days straight. Can we expect this to happen again? LulzSec saw a handful of its members arrested earlier this month. Is it going to seek revenge or is it just back to business as usual?
See also:
- Anonymous: LulzSec returns on April Fools' Day?
- Anonymous hacks Panda Security in response to LulzSec arrests
- LulzSec mastermind helps FBI arrest notorious hacktivists
- LulzSec hackers 'brought down' by own leader
- AntiSec hackers release 'largest cache yet' of law enforcement data
- LulzSec disbands: Final cache includes AT&T internal data and 750,000 user accounts