LulzSec's leader, Sabu, revealed?

A day after LulzSec's release of Arizona law enforcement information for "Operation Anti-Security," the Internet is now abuzz with behind-the-scenes LulzSec chat logs and purported personal information about LulzSec's leader, Sabu, being discovered.
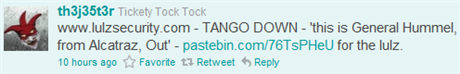
First up, a massive amount of research posted on Twitter by th3j35t3r is making the rounds as it yields results that claim to completely out who Sabu, LulzSec's leader, actually is:
In summary, here is the information claimed to belong to Sabu as per the research:
Name(s): Xavier Kaotico, Xavier de Leon Email: sabu@pure-elite.org, xavier@pure-elite.org, xavier@sentinix.org, xavier@tigerteam.se Age: 30 as of 2011-06-21 Location: Possibly New York City, NY (has lived there) Websites: sabu.net, pure-elite.org, confinement.org Profession: Independent IT consultant Interests: Python programming, Linux, network security, exploit development
A look at the links contained within the research shows that the information mined is as claimed. For example:
Whether or not this is the same Sabu that leads LulzSec remains to be seen. If correct, this information potentially places the leader of LulzSec right here on U.S. soil; something the FBI will certainly take interest in. Have a look at the research yourself and see how much weight you feel it deserves.
Next, guardian.co.uk has posted a massive chat log of LulzSec's that was leaked. All said, we gain a rather interesting glimpse into an organization that appears far more human than the nonchalant, witty game-face they put on. To quote:
LulzSec is not, despite its braggadocio, a large – or even coherent – organisation. The logs reveal how one hacker known as "Sabu", believed to be a 30-year-old security consultant, effectively controls the group of between six and eight people, keeping the others in line and warning them not to discuss what they have done with others; another, "Kayla", provides a large botnet – networks of infected computers controlled remotely – to bring down targeted websites with distributed denial of service (DDoS) attacks; while a third, "Topiary", manages the public image, including the LulzSec Twitter feed.
They turn out to be obsessed with their coverage in the media, especially in physical newspapers, sharing pictures of coverage they have received in the Wall Street Journal and other papers. They also engineered a misinformation campaign to make people think they are a US-government sponsored team.
They also express their enmity towards a rival called The Jester – an ex-US military hacker who usually attacks jihadist sites, but has become embroiled in a dispute with Anonymous, WikiLeaks and LulzSec over the leaked diplomatic cables and, more recently, LulzSec's attacks on US government websites, including those of the CIA and the US Senate.
With so many people waiting for these individuals to be brought to justice for their actions -- regardless of how justified LulzSec and their supporters feel they are --we may just see this whole thing unravel right before our eyes shortly.
That, or the Lulz boat will simply continue to sail on despite this latest wave of information and any arrests that may potentially result from it. But don't forget that even if LulzSec falls, we still have Anonymous to keep an eye on as well. And never mind the localized sects of LulzSec that seem to operate for different causes non-inclusive of Sabu's leadership.
With LulzSec's claim of more information ready to be leaked on Monday, it will be interesting to see how events unfold (or lack thereof) throughout the weekend in light of the information above.
What are your thoughts? Do you agree with what LulzSec has done so far, or are you pining away for the moment these individuals are captured? Let us hear from you in the comments section below!
-Stephen Chapman SEO Whistleblower