Mac OS X SMS ransomware - hype or real threat?
In need of a fresh example that cybercriminals are actively looking for ways to monetize infected Mac OS X hosts?
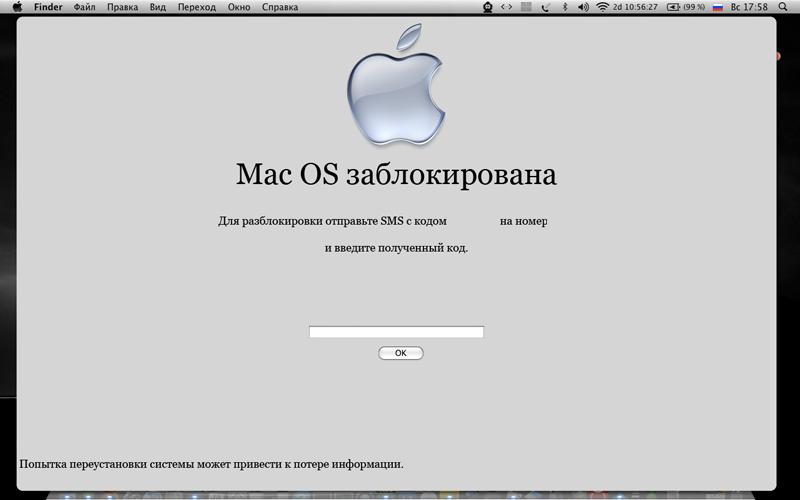
Early-stage discussions at several web forums, including a PoC (proof of concept, source code included) Mac OS X blocker as well as potential GUIs for the ransomware, offer an insight into the potential to monetize OS X infected hosts using SMS-based ransomware.
Is Mac OS X ransomware just a hype, or a real threat? Let's take a brief retrospective of known OS X monetization strategies used by cybercriminals, discuss the ransomware threat on the Windows OS, and go through some pretty self-explanatory ransomware layouts for the OS X based ransomware.
What have originally started as a complaint from a single user who claims to have been victimized by SMS-based ransomware on his Mac OS X, motivated others to not just come up with possible layouts for the OS X ransomware GUI, but also, release a proof of concept blocker.
In its current version, the PoC blocker doesn't extort money, instead it demonstrates its ability to intercept all attempts to close down and exit the application, with the author and other participants commenting that "although it was built as a PoC, anyone can add additional features including auto-starting features, perhaps even spreading functionality".
- Consider going through related ransomware posts: iHacked: jailbroken iPhones compromised, $5 ransom demanded; New LoroBot ransomware encrypts files, demands $100 for decryption; New ransomware locks PCs, demands premium SMS for removal; Scareware meets ransomware: “Buy our fake product and we’ll decrypt the files”; Who’s behind the GPcode ransomware?; How to recover GPcode encrypted files?
Sadly, they are right. And while the commonly shared attitude between the people participating in the discussion is in the lines of "harmless joke having nothing to do with malware", ransomware is virtual extortion, or the monetization of disrupting an end user's productivity. Another participant in the discussion is pretty straightforward in his ambitions by saying "Guys, we are ready. Looking forward to it".
How widespread is the ransomware threat on the Windows OS? Pretty widespread. According to Fortinet's February Threatscape report:
- Most notable was the number one chart-topping malware variant, HTML/Goldun.AXT, which works by disseminating a binary malware file that downloads the ransomware "Security Tool" and, once executed, locks up applications until a cleansing tool is purchased to restore the computer. While this example accounts for the majority of activity detected this period, the Security Tool ransomware was also distributed through SEO attacks as well.
- Consider going through related Windows-based ransomware research: SMS Ransomware Displays Persistent Inline Ads; SMS Ransomware Source Code Now Offered for Sale; 3rd SMS Ransomware Variant Offered for Sale; 4th SMS Ransomware Variant Offered for Sale; 5th SMS Ransomware Variant Offered for Sale; 6th SMS Ransomware Variant Offered for Sale
The laws of demand and supply fully apply within the cybercrime ecosystem. Therefore, it's only a matter of time before someone starts developing this malware segment, either driven by personal financial gains, or by someone else's demand for such a malicious release.
What do you think? Is Mac OS X ransomware a real threat, or a hype, with cybercriminals basically experimenting in the short term?
TalkBack.