Malvertising campaign hits US users hard over Presidents' Day weekend

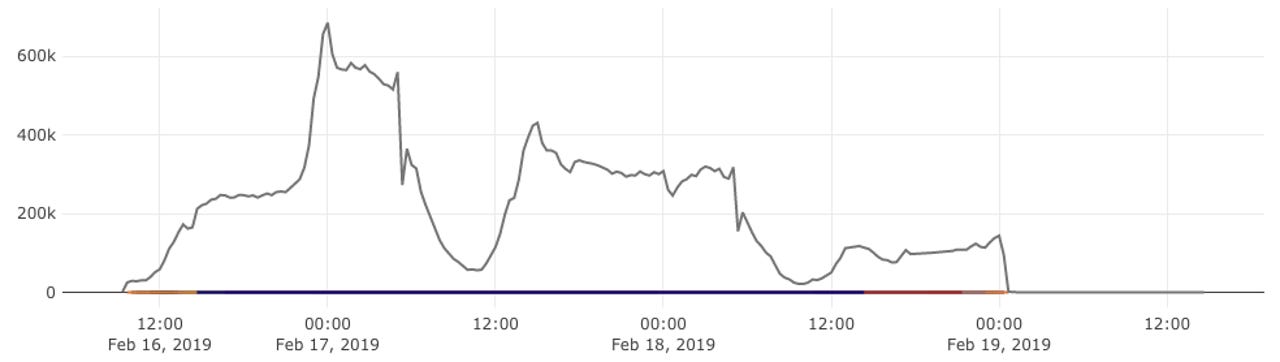
A massive malvertising campaign has hit US users over the extended Presidents' Day weekend, according to Confiant, a company that tracks bad ads.
In a private report shared with ZDNet, Confiant researchers say they've seen as many as 800 million malicious ad impressions part of this malvertising campaign.
When clicked, the ads would redirect users to a wide variety of malicious sites.
"Landing pages for these types of campaigns tend to rotate, but the ones we've seen were not malware loaders," Jerome Dangu, Confiant CTO, told ZDNet in an interview today. "Instead they were more phishing-oriented."
The end goal was to trick users into entering their personal and financial information in order forms for all sorts of fake products. Crooks would collect these details and later sell or use them for other fraudulent operations.
Confiant has been tracking this group for months as "eGobbler," a name inspired by the Thanksgiving holiday --when researchers spotted this threat actor's campaigns in action for the first time.
"Although these attackers have been around for months, they concentrated their efforts over the Presidents' Day holiday weekend, correctly assuming that they would be successful during a time when ad operations teams are offline or less available to troubleshoot security issues," the company wrote in its report.
eGobbler campaign targeted US users only
The security firm says eGobbler's malicious ads were configured to appear only for US-based users. This is the third malvertising campaign that Confiant has tracked in the past six months that has targeted the US.
The first was the ScamClub operation, detected in November 2018 and which hijacked over 300 million browser sessions over 48 hours to redirect users to adult and gift card scams.
The second was the VeryMal group that also targeted US users, hijacking over five million web sessions to redirect Apple users to pages offering malware-laced software downloads.
While Confiant has not officially confirmed this just yet, it appears that eGobbler has also targeted Apple users as well.
Confiant researchers say the eGobbler group used a JavaScript API to look up the user's GPU chipset type, filtering traffic for Apple A11 or A12 custom-made GPU chipsets.
On the surface, based on their Apple-centric targeting preferences, it may look like that the three operations are related, however, researchers have not drawn any official conclusions on this issue.
"There is no obvious connection that we've been able to make just yet," Dangu told ZDNet.
Ad blockers, a temporary, but flawed solution
When we asked if ad blockers are a good solution for preventing bad ads from loading inside people's browsers, the Confiant CTO warned that blocking ads might not be the best solution for the health of the Internet in the long term.
"We wouldn't take the stance that ad blockers are positive because that's not a solution against ad-fraud but rather a recipe for killing the advertising industry as we know it," he said. "Put simply, we encourage executives across [the ad] industry to adopt solutions like ours in order to prevent the need for an ad-blocker."
In other words, the Confiant CTO says that if ad platforms would do a better job at policing their adverts, users wouldn't feel the need to block ads in the first place.
The advertising industry has already started to look into imposing a minimum threshold for the quality of online ads with the adoption of the "Better Ads Standards," however, Dangu argues that ad platforms should also look into security their platforms from abuse by criminal operations as well.
Cybercrime and malware, 2019 predictions
Related security coverage:
- Microsoft removes eight cryptojacking apps from official store
- White hats spread VKontakte worm after social network doesn't pay bug bounty
- Rietspoof malware spreads via Facebook Messenger and Skype spam
- Another WordPress commercial plugin gets exploited in the wild
- New macOS security flaw lets malicious apps steal your Safari browsing history
- Hacker puts up for sale third round of hacked databases on the Dark Web
- Cryptomining malware spread via US, UK and Australian government sites TechRepublic
- Google bans cryptocurrency mining extensions for Chrome CNET