Malware Watch: Free Mac OS X screensavers bundled with spyware
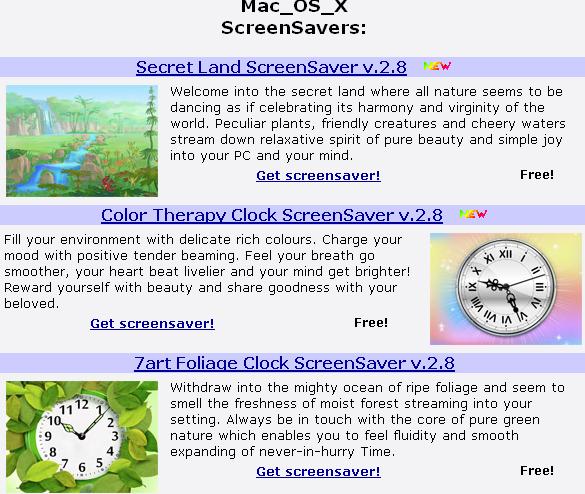
Researchers from Intego have discovered the OSX/OpinionSpy spyware in 29 free Mac OS X screensavers currently online at 7art-screensavers(dot)com.
According to the company's security alert, despite the fact that the "market research" program also known as RelevantKnowledge, claims to collect only browsing and purchasing information, a deeper investigation reveals a much more intrusive approach.
More details on what the spyware does once it's executed, and the list of the screensavers bundled with it:
- It opens an HTTP backdoor using port 8254
- It injects code, without user intervention, into Safari, Firefox and iChat, and copies personal data from these applications. Code injection is a form of behavior similar to that of a virus, and this malware “infects” applications when they are running to be able to carry out its operations. (It infects the applications’ code in the Mac’s memory, and does not infect the actual applications’ files on the user’s hard disk.)
- It regularly sends data, in encrypted form, to a number of servers using ports 80 and 443. It sends data to these servers about files it has scanned locally, and also sends e-mail addresses, iChat message headers and URLs, as well as other data. This data may include personal data, such as user names, passwords, credit card numbers, web browser bookmarks, history and much more
- If a user deletes the original application or screen saver that installed this spyware, the spyware itself will remain installed and continue to operate.
The authors of these screensavers have bundled the RelevantKnowledge application within the installation process, which naturally cannot continue unless the user accepts the EULA describing the program as the "Trees of Knowledge".
The RelevantKnowledge spyware/adware app, is a well known Windows based pest, with a surprisingly high number of people still willing to install it, in order to access the freeware application used as the lure. The risks involved? Excluding the intrusive, spyware-like practices of the application, in 2006, several researchers discovered a remotely exploitable flaw within the application, allowing anyone to perform keylogging and monitoring of active windows content on every host running it.
Clearly, the people attempting to monetize their screensavers using RelevantKnowledge, are not just borrowing tricks from the playbook of the Windows malware author, using the ubiquitous "freeware application" as a lure, but have ported the spyware to Mac OS X.
Mac OS X malware (New Mac OS X malware variant spotted; Mac OS X SMS ransomware - hype or real threat?) is no longer an urban legend, and neither are the remotely exploitable flaws targeting Apple's OS, or the third party apps/plugins running on it.
What do you think? Talkback.