Microsoft and industry partners seize key domain used in SolarWinds hack

Microsoft and a coalition of tech companies have intervened today to seize and sinkhole a domain that played a central role in the SolarWinds hack, ZDNet has learned from sources familiar with the matter.
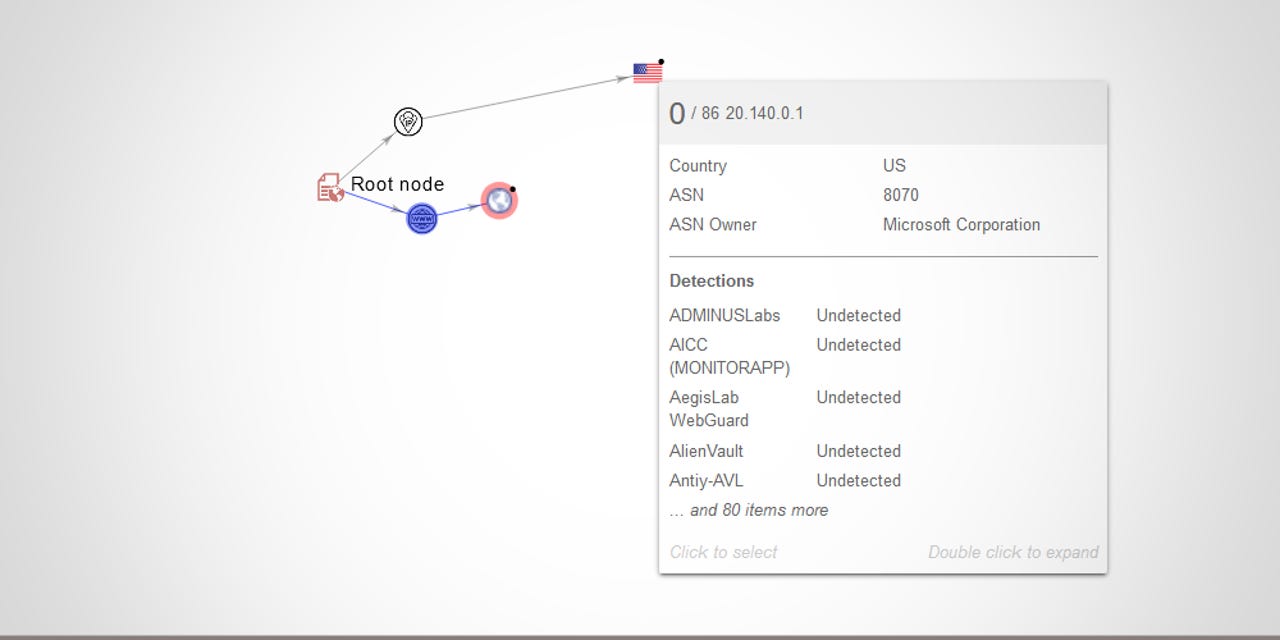
The domain in question is avsvmcloud[.]com, which served as command and control (C&C) server for malware delivered to around 18,000 SolarWinds customers via a trojanized update for the company's Orion app.
SolarWinds Orion updates versions 2019.4 through 2020.2.1, released between March 2020 and June 2020, contained a strain of malware named SUNBURST (also known as Solorigate).
Once installed on a computer, the malware would sit dormant for 12 to 14 days and then ping a subdomain of avsvmcloud[.]com.
According to analysis from security firm FireEye, the C&C domain would reply with a DNS response that contained a CNAME field with information on another domain from where the SUNBURST malware would obtain further instructions and additional payloads to execute on an infected company's network.
Takedown to prevent last-ditch hacks
Earlier today, a coalition of tech companies seized and sinkholed avsvmcloud[.]com, transferring the domain into Microsoft's possession.
Sources familiar with today's actions described the takedown as "protective work" done to prevent the threat actor behind the SolarWinds hack from delivering new orders to infected computers.
Even if the SolarWinds hack became public on Sunday, the SUNBURST operators still had the ability to deploy additional malware payloads on the networks of companies that failed to update their Orion apps and still have the SUNBURST malware installed on their networks.
In SEC documents filed on Monday, SolarWinds estimated that at least 18,000 customers installed the trojanized Orion app update and most likely have the first-stage SUNBURST malware on their internal networks.
However, the hackers do not appear to have taken advatange of all these systems and only carried out a handful of carefully-orchestrated intrusions into the networks of high-profile targets.
SolarWinds Updates
This was confirmed in a report on Monday from US security firm Symantec, which said that it discovered the SUNBURST malware on the internal networks of 100 of its customers, but it did not see any evidence of second-stage payloads or network escalation activity.
Similarly, Reuters also reported on Monday, confirmed with independent sources by ZDNet, that many companies that installed the trojanized Orion app update did not discover evidence of additional activity and escalation on internal networks, confirming that hackers only went after high-profile targets.
Since Sunday, when the SolarWinds hack came to light, the number of confirmed victims has grown to include:
- US cybersecurity firm FireEye
- The US Treasury Department
- The US Department of Commerce's National Telecommunications and Information Administration (NTIA)
- The Department of Health's National Institutes of Health (NIH)
- The Cybersecurity and Infrastructure Agency (CISA)
- The Department of Homeland Security (DHS)
- The US Department of State
Sinkholing efforts underway to discover all victims
Currently, the avsvmcloud[.]com domain redirects to an IP address owned by Microsoft, with Microsoft and its partners receiving beacons from all the systems where the trojanized SolarWinds app has been installed.
This technique, known as sinkholing, is allowing Microsoft and its partners to build a list of all infected victims, which the organizations plan to use to notify all affected companies and government agencies.
"This is not the first time a domain associated with malware has been seized by international law enforcement and even by a provider," ExtraHop CTO Jesse Rothstein told ZDNet in an email, referring to Microsoft's previous takedown and sinkholing efforts against the Necurs and TrickBot botnets.
Current takedown and sinkholing efforts also include representatives for the Federal Bureau of Investigation and the Cybersecurity and Infrastructure Security Agency, looking to find other US government agencies that might have been compromised.
Due to SolarWinds' extensive US government clientele, government officials are treating the SolarWinds compromise as a national security emergency. A day before the SolarWinds breach became public, the White House held a rare meeting of the US National Security Council to discuss the hack and its repercussions.
Indicators of compromise and instructions on how to discover and deal with a SUNBURST malware infection are available from Microsoft, FireEye, and CISA.
UPDATED on December 16: In an emailed statement FireEye formally confirmed a coordinated takedown of the SUNBURST C&C domain, together with Microsoft and GoDaddy. The explained that what ZDNet sources described as "protective work" was a killswitch mechanism found in the SUNBURST domain that could stop attackers from escalating infections. Full statement below:
"As part of our commitment to our customers and community, FireEye continues to take action to protect organizations from the SolarWinds supply chain attack. We disclosed the supply chain attack shortly after we discovered it, and we provided information on related malicious activity and coordinated with partners to disable some malware related to this activity.
"SUNBURST is the malware that was distributed through SolarWinds software. As part of FireEye's analysis of SUNBURST, we identified a killswitch that would prevent SUNBURST from continuing to operate.
"Depending on the IP address returned when the malware resolves avsvmcloud[.]com, under certain conditions, the malware would terminate itself and prevent further execution. FireEye collaborated with GoDaddy and Microsoft to deactivate SUNBURST infections.
"This killswitch will affect new and previous SUNBURST infections by disabling SUNBURST deployments that are still beaconing to avsvmcloud[.]com. However, in the intrusions FireEye has seen, this actor moved quickly to establish additional persistent mechanisms to access to victim networks beyond the SUNBURST backdoor. This killswitch will not remove the actor from victim networks where they have established other backdoors. However, it will make it more difficult to for the actor to leverage the previously distributed versions of SUNBURST."