Microsoft says hackers have exploited zero-days in Windows 10's Edge, Office, IE; issues fix

Five bulletins are rated as critical and concern remote code execution vulnerabilities affecting Edge, Internet Explorer, Adobe Flash Player, Office, Windows, and Skype for Business.
Microsoft's October Patch Tuesday fixes dozens of critical flaws, among them five affecting Internet Explorer, Edge, and Office that have already been under attack.
Tuesday's update addresses 49 vulnerabilities within 10 security bulletins. Five bulletins are rated as critical and concern remote code execution vulnerabilities affecting Edge, Internet Explorer, Adobe Flash Player, Office, Windows, and Skype for Business.
According to Microsoft, there were four so-called zero-day flaws, or previously unknown bugs that were being exploited in the wild. However, none has been publicly disclosed before now.
All these bugs serve as a reminder for users to be cautious when clicking on links or opening attachments from unknown sources.
The IE zero-day is an information-disclosure flaw, CVE-2016-3298, contained in two bulletins. It could allow an attacker to "test for the presence of files on disk". However, an attacker must lure a target to a malicious website to exploit the bug.
Office contains a memory-corruption vulnerability, CVE-2016-7193, which could allow an attacker to take control of a system if the current user is logged on with administrative user rights.
An attacker could exploit this flaw by emailing a malicious attachment or convincing a user to visit an attack site by way of a link.
The Windows Graphics Component also contains a remote code execution vulnerability, CVE-2016-3393, which could be attacked via links to a malicious website or harmful attachments.
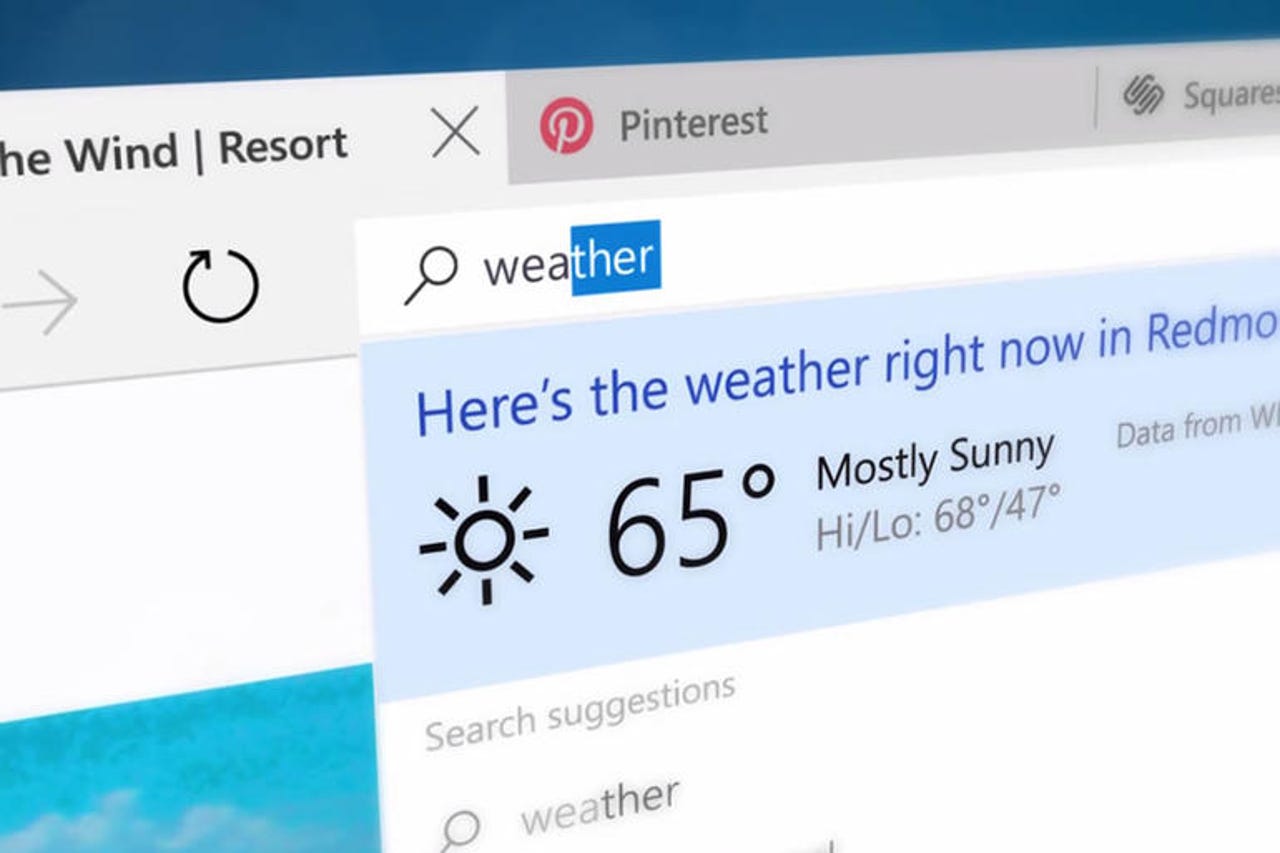
The Edge zero-day is also a remote code execution flaw, CVE-2016-7189, stemming from an issue with the browser's scripting engine. An attacker would need to convince a user to visit a malicious website.
October also marks the first time Microsoft has used its new 'rollup' model for Windows 7, 8.1, Windows Server 2008 R2, Windows Server 2012 and Server 2012 R2, where rollups address both security and reliability issues in a single update.
From here on in, the monthly rollups will be published to Windows Update (WU), WSUS, SCCM, and the Windows Update Catalog, refreshing the previous month's rollup.
Microsoft last week highlighted the three choices admins will have for applying updates under the rollout model.
The 'security-only quality update' contains all new security fixes for the month, which is published to WSUS and Windows Update Catalog, but not Windows Update.
The 'security monthly quality rollup' includes new fixes for that month plus fixes from previous monthly rollups. Consumers install it from Windows Update, while admins can use WSUS and the Windows Update Catalog.
There's also a 'preview rollup', which offers a preview of non-security fixes that are scheduled for release in the next monthly rollup, as well as fixes from the previous monthly rollup. This preview is published on the third Tuesday of the month, as opposed to Patch Tuesday on the second Tuesday of each month.
Microsoft notes that from early 2017 it will begin adding older fixes to the preview rollup so that it eventually becomes "fully cumulative" and ensures PCs with the latest monthly rollup are fully updated.
The .NET Framework is also moving to the monthly rollup model and will include "security and reliability updates to all versions of the .NET Framework as a single monthly release, targeting the same timing and cadence as Windows".
UPDATE: Since this article was first published, Microsoft has admitted to an error in its security bulletin and has provided the following statement: "As part of October's Security Update release, CVE-2016-7189 was mislabeled in bulletin MS16-119 as exploited. There is no evidence of any active attacks using this vulnerability and the bulletin text has been corrected."