Microsoft has a subdomain hijacking problem

techrepublic cheat sheet
A security researcher has pointed out today that Microsoft has a problem in managing its thousands of subdomains, many of which can be hijacked and used for attacks against users, its employees, or for showing spammy content.
The issue has been brought up today by Michel Gaschet, a security researcher and a developer for NIC.gp.
In an interview with ZDNet, Gaschet said that during the past three years, he's been reporting subdomains with misconfigured DNS records to Microsoft, but the company has either been ignoring reports or silently securing some subdomains, but not all.
Researcher: Only 5%-10% got fixed
Gaschet says he reported 21 msn.com subdomains that were vulnerable to hijacks to Microsoft in 2017 [1, 2], and then another 142 misconfigured microsoft.com subdomains in 2019 [1, 2].
Further, the researcher also privately shared with ZDNet another list of 117 microsoft.com subdomains that he also reported to Microsoft last year.
Of all the reported misconfigured subdomains, Gaschet told ZDNet that Microsoft only addressed a few. The researcher puts the number at somewhere between 5% and 10% of all the subdomains he reported.
Blame DNS misconfigurations
Gaschet told ZDNet the OS maker usually fixes big subdomains, like cloud.microsoft.com and account.dpedge.microsoft.com, but leaves the other subdomains exposed to hijacks.
The researcher said that most of the Microsoft subdomains are vulnerable to basic misconfigurations in their respective DNS entries. The researcher says this 2014 blog post from Detectify explains the problem in depth.
"The root cause/mistake is a forgotten DNS entry pointing to something that doesn't exist anymore, or never existed, like a typo in the DNS entry content," Gaschet told ZDNet.
Subdomain hijacks lead to spam on microsoft.com
But until now, these misconfigurations have never caused Microsoft any problems or headaches, despite being an attractive attack surface.
In a hypothetical scenario, an attacker could hijack one of these subdomains and host phishing pages to harvest login credentials for Microsoft employees, business partners or even its end-users.
The scenario is not something that has not been seen before.
Luckily, no dangerous threat groups have noticed this problem.
Sadly, others have.
Today, Gaschet pointed out on Twitter that at least one spam group has figured out they could hijack Microsoft's subdomains and boost their spammy content by hosting it on a reputable domain.
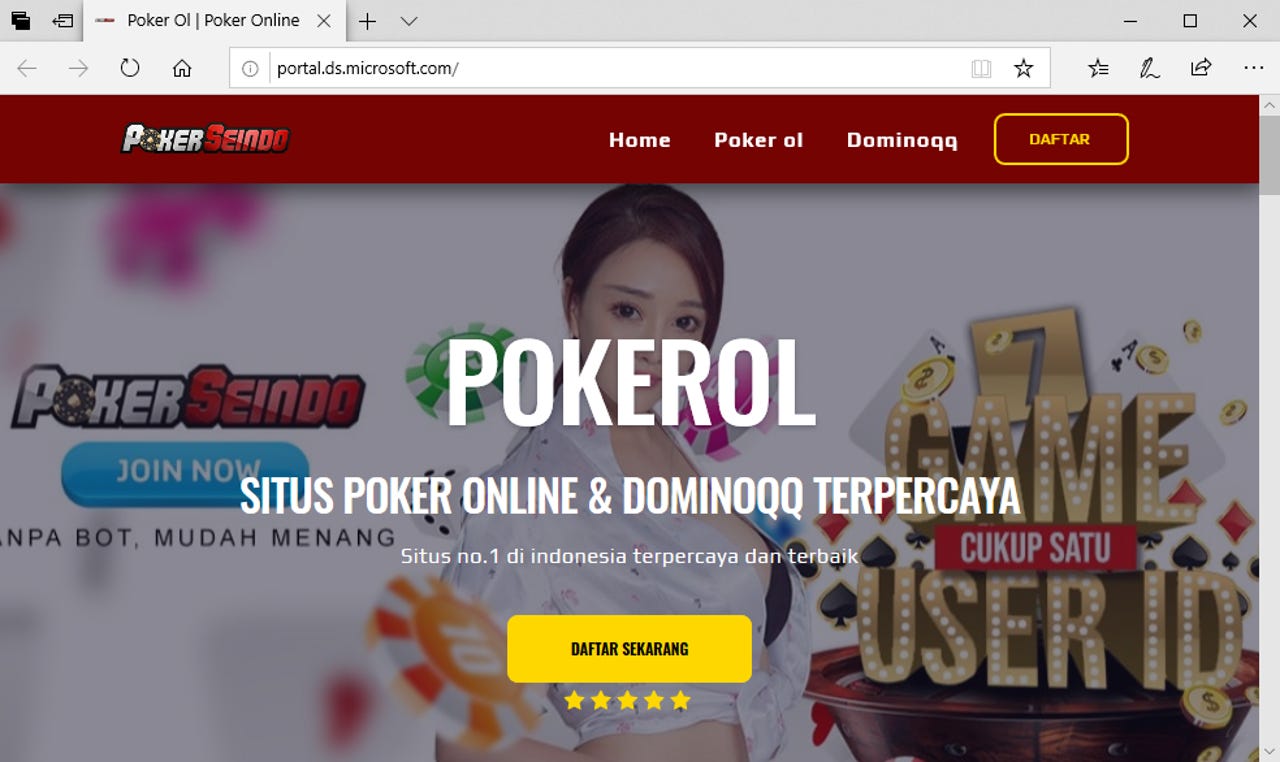
Gaschet says he spotted ads for Indonesian poker casinos on at least four legitimate Microsoft subdomains. These include portal.ds.microsoft.com, perfect10.microsoft.com, ies.global.microsoft.com, and blog-ambassadors.microsoft.com.
"The issue disclosed involving ad spam has been mitigated," a Microsoft spokesperson told us after ZDNet reached out to the company. Microsoft also recommended that users exercise caution when clicking on links or opening unknown files that may lead them to malicious sites, although it did not address how come these sites end up being hosted on its domain, or other issues Gaschet raised in a Twitter thread today.
https://t.co/XAJfbsE4ht
— Michel Gaschet (@Michel_Gaschet) February 18, 2020
This kind of stuff, this is what you get by putting subdomain takeover out of scope, and don't fix critical subdomain takeover from good peoples, rarely thanks them and generally not respond to them. Great job, @msftsecresponse 👏
On Twitter, Gaschet guessed that one of the reasons why Microsoft is not prioritizing fixing these issues is because "subdomain takeovers" are not part of the company's bug bounty program, which means any reports are not getting prioritized, even despite the severity of the issues being reported.
Gaschet, who is a developer for NIC.gp, the official registrar for the Guadeloupe .gp top-level domain, urged Microsoft to revamp how it manages its DNS records, which he said are the source of most of these misconfigurations.
Article updated on February 19, 9am ET with comment from Microsoft.