Microsoft pushes crypto standards forward

When used properly, cryptography will impede even the most capable of attackers. One of the keys to using it properly is to implement and even to require the use of the latest crypto standards.
On Tuesday Microsoft made several announcements of changes in pursuit of stronger cryptography:
- As of January 1, 2016, Microsoft will no longer allow certificate authorities in the Microsoft Root Certificate Program to issue certificates for SSL or code signing that use the SHA-1 hashing algorithm. SHA-2 is the preferred method now.
- The company issued a security advisory recommending disabling the use of the RC4 stream cipher. At the same time they announced that Internet Explorer 11 will discourage the use of RC4.
- They announced that Internet Explorer 11 turns on TLS version 1.2 by default.
Unlike most other standards, cryptography standards have a definite shelf life. Research and Moore's law conspire to weaken techniques which were state of the art in their day.
But software written to implement the standards has to be modified in order to support the new standards, so users and other software companies often resist the changes. That's why it takes a company with some nerve, and probably a lot of market muscle, to move the standards forward. Both Google and Microsoft have been leaders in this regard.
The deprecation of SHA-1 is an especially bold move, even if it gives more than two years of warning. SHA-1 is a cryptographic hash algorithm. Also called a message digest, a cryptographic hash is a one-way transformation of a block of data into a value of a fixed size. There should be no way, based on the hash value, to determine anything about the data on which it was based, and even a small change in the data should result in a substantially different hash. When an algorithm generates the same hash value for two different input blocks, we say there is a collision.
Before SHA-1 there was a hash called MD5. Designed over 20 years ago by Ron Rivest (the 'R' in RSA), MD5 has since been shown to be subject to hash collisions and other weaknesses. Research has found possible weaknesses in SHA-1, although no actual attacks have been developed, or at least none have been publicly demonstrated.
SHA-2 was developed as a stronger alternative. Though algorithmically similar to SHA-1, SHA-2 generates a larger hash. The SHA-3 standard was recently finalized, but such things take a long time to be widely-deployed. (When the Microsoft advisory says that they will require SHA-2, it presumably means they anticipate supporting SHA-3 when the time comes.)
SHA-2 is at, or at least near a level of deployment such that it can be used in a certificate without too much concern for problems. The fact that Microsoft is making SHA-2 mandatory for inclusion in its Root Certificate program gives developers incentive enough to address any problems that remain. (They need to start by convincing their own people. I just checked and the EV-SSL certificate for Office 365 — login.microsoftonline.com — uses SHA-1.)
The RC4 cipher is even older than the MD5 hash; it too was created by Ron Rivest, in 1987. The cipher is the part of encryption that actually encrypts. It takes plaintext (unencrypted data) as input and generates encrypted data. A stream cipher (as opposed to a block cipher) operates on streamed data, one character at a time. For over ten years now, problems have been demonstrated in the RC4 cipher, and yet it is still widely used.
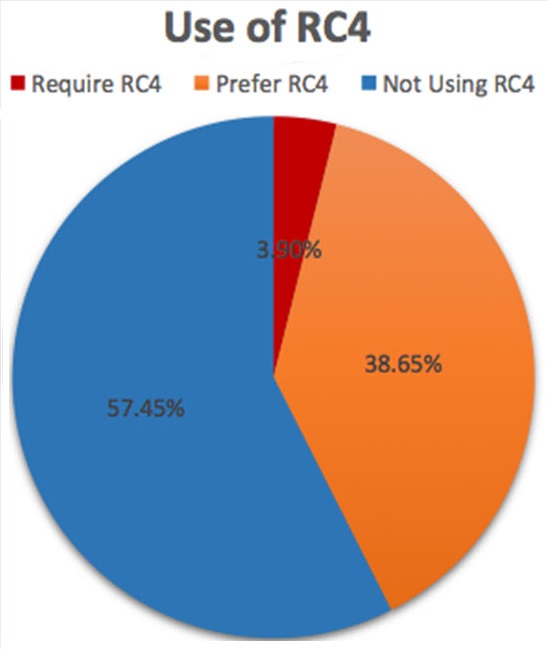
When endpoints, such as a web browser and a web server, connect and set up an encrypted communications channel, part of the negotiation is to determine which cipher will be used. Prioritized lists are exchanged and the highest-priority cipher that matches both is used. What Microsoft will be doing in IE11 is not to eliminate RC4, but to deprioritize it so that other, more secure ciphers will be used. At the same time Microsoft urges other developers to do the same.
The RC4 changes are coming to Windows 7, Windows 8, Windows 8.1, Windows RT, Server 2008 R2, and Server 2012. They are not coming to Windows XP and not even to Windows Vista.
The third change, in which Internet Explorer 11 will turn on TLS 1.2 by default, is the least disruptive of the three. TLS is Transport Layer Security and is the successor to Secure Sockets Layer (SSL), although the name SSL is often used when referring to TLS. The main advances in new versions of TLS are the incorporation of newer, high-security and high-performance suites of ciphers and the removal of older, less secure ciphers. Certain attacks, such as the BEAST attack, do not work against TLS 1.2 implementations.
IE has supported TLS 1.2 (a standard that was finalized over 5 years ago) for a long time, but not turned it on. Users could turn it on themselves. Google Chrome on Windows uses the same Windows Crypto settings as IE, so its behavior will change as well. Firefox, which implements their own cryptography library, is behind the times on this, not even supporting TLS 1.2 yet.
The benefits of turning on TLS 1.2 by default are automatic in many cases. If the server supports 1.2 (Microsoft claims 16% of servers do) then it and the client will negotiate with a more secure set of ciphers.
These crypto standards are just one of the ways that using newer versions of software tends to make you more secure. Microsoft's market power should also drive some vendors to update their own products so that they work well with Microsoft's. It's all good for all of us.