Microsoft unveils plans for stronger encryption and tighter controls over Office 365 data

For organizations accustomed to running on-premises servers, handing over business-critical services to a third party is not an easy decision.
That's especially true in a world where the very example of Edward Snowden offers a nightmare scenario for a CIO:
You trust your own data center employees, and you know how to keep an eye on them. But when you're using somebody else's servers in a faraway data center, how can you protect yourself from a rogue employee who wants to steal your data for political purposes or to sell to a competitor?
In the post-Snowden era, answering tough questions about data security is what keeps executives at American cloud providers up at night.
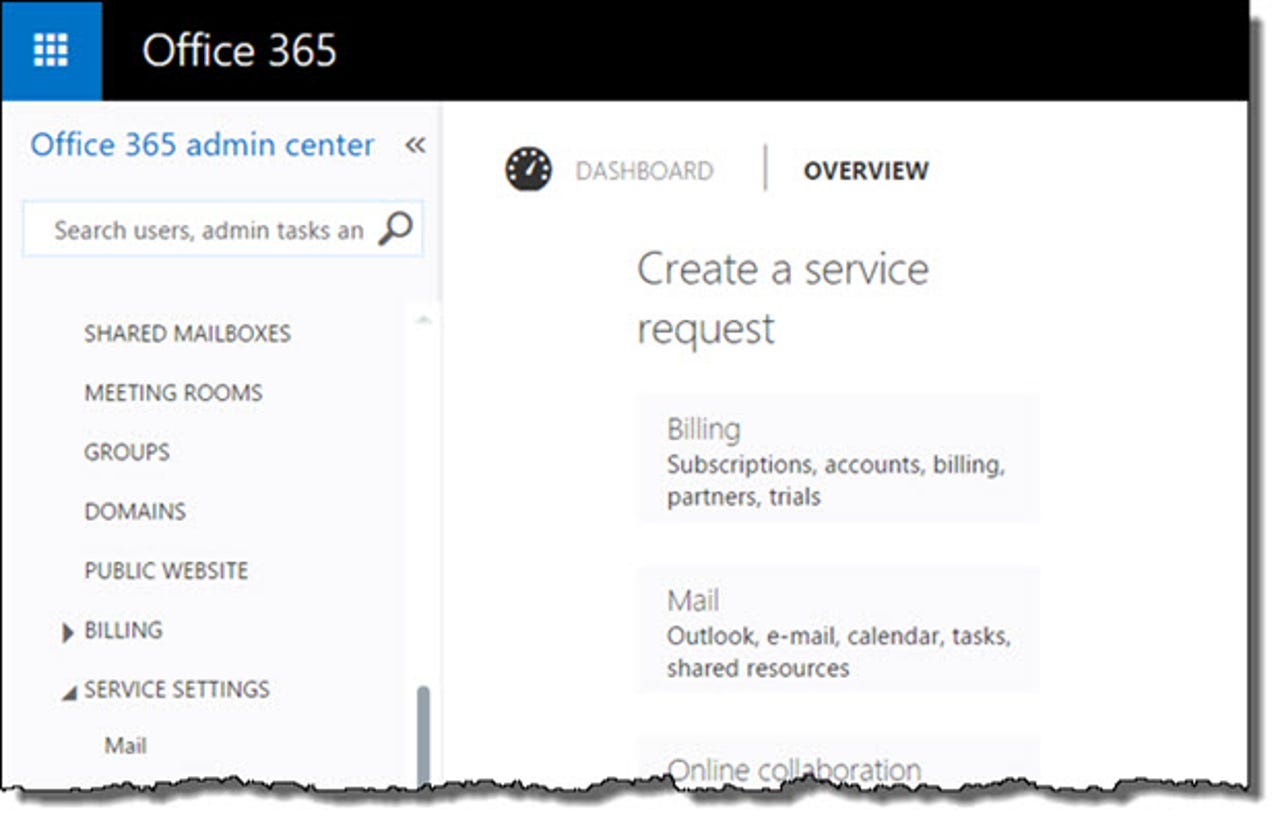
Microsoft, which has been steadily migrating its Exchange and SharePoint customers to Office 365, announced its latest security moves at the RSA conference yesterday.
The changes affect Microsoft's paid business services, Office 365 and Microsoft Azure.
The biggest changes in store are improvements in encryption for Office 365. Email is currently stored on BitLocker-encrypted disks and encrypted as it moves in and out of the data center. By the end of this year, Microsoft says, it will also implement content-level encryption, so that data will be protected even if someone gains access to the unencrypted disk contents. (This change was already in place for files stored in SharePoint Online.)
And within the next year, subscribers to Microsoft's business and enterprise Office 365 plans will be given the option to use customer-generated encryption keys to encrypt data on Microsoft's servers. That makes it possible for the customer to render that data unreadable by revoking the encryption keys.
Another new Office 365 feature, Customer Lockbox, is intended to reassure customers about unauthorized access to their data. Office 365 services aren't run the way a customer would run the on-premises equivalents. Instead, Microsoft has architected the centers so that almost all actions that might allow access to data are done through automated processes.
For the rare instances when a support engineer needs to perform an action that might allow access to data, such as repairing a corrupted mailbox, customers are now in the middle of the workflow, Microsoft says. In those cases, with the customer's approval, engineers get a temporary, time-limited account that allows just enough access to perform that support task.