Microsoft's Live Search (finally) adds malware warnings
According to a post by Christian Seifert, Software Design Engineer at Live Search Anti-Spam & Anti-Malware Team, as of today, users of Microsoft's search engine would receive warnings upon clicking on a potentially malware serving web site. In comparison, Google and Yahoo Search both introduced malware warnings within their search results in May, 2008.
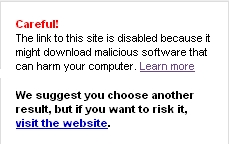
Upon clicking on a link that's identified as a malware serving one, the following message appears in a box :
"Careful! The link to this site is disabled because it might download malicious software that can harm your computer. Learn more. We suggest you choose another result, but if you want to risk it, visit the website."
Users should always keep in mind that adaptive cybercriminals are increasingly taking advantage of legitimate web services, and using them as infection vectors, which on the majority of occasions remain undetected by the malware warnings offered by the most popular search engines. Moreover, during the last two quarters of 2008, more "malicious doorways" started getting SQL injected within legitimate sites in order to trick the search engine's crawlers into believing that the malicious site they've just crawled is malware free. How are they achieving that? Through multiple redirections with the first pack of domains not serving anything malicious so that a crawler would eventually give up on the site.
No matter the dynamically changing tactics on behalf of malicious attackers, the core infection method that they efficiently take advantage of remains the same (at least for now) - outdated and already patched client-side vulnerabilities which you should have taken care of a long time ago.