Weebly confirms hack; millions of Foursquare accounts also exposed

(Image: File photo)
Another day, another hack.
Weebly and Foursquare are the latest in a long line of tech companies under scrutiny for their security practices. On Thursday, breach notification site LeakedSource posted details of the attacks in a blog post explaining what happened.
More than 43.4 million accounts were stolen in the attack, thought to have been carried out in February.
DON'T BREAK THE LAW
According to a sample of the data seen by ZDNet, each record in this mega breach contains a username, email address, password, and IP address. Stolen passwords were stored with bcrypt, a strong system for scrambling passwords.
In a statement, the company confirmed the breach.
"At this point we do not have evidence of any customer website being improperly accessed," said a spokesperson. "We do not store any full credit card numbers on Weebly servers, and at this time we're not aware that any credit card information that can be used for fraudulent charges was part of this incident."
The company said it was notifying customers and working to initiate password resets and requirements.
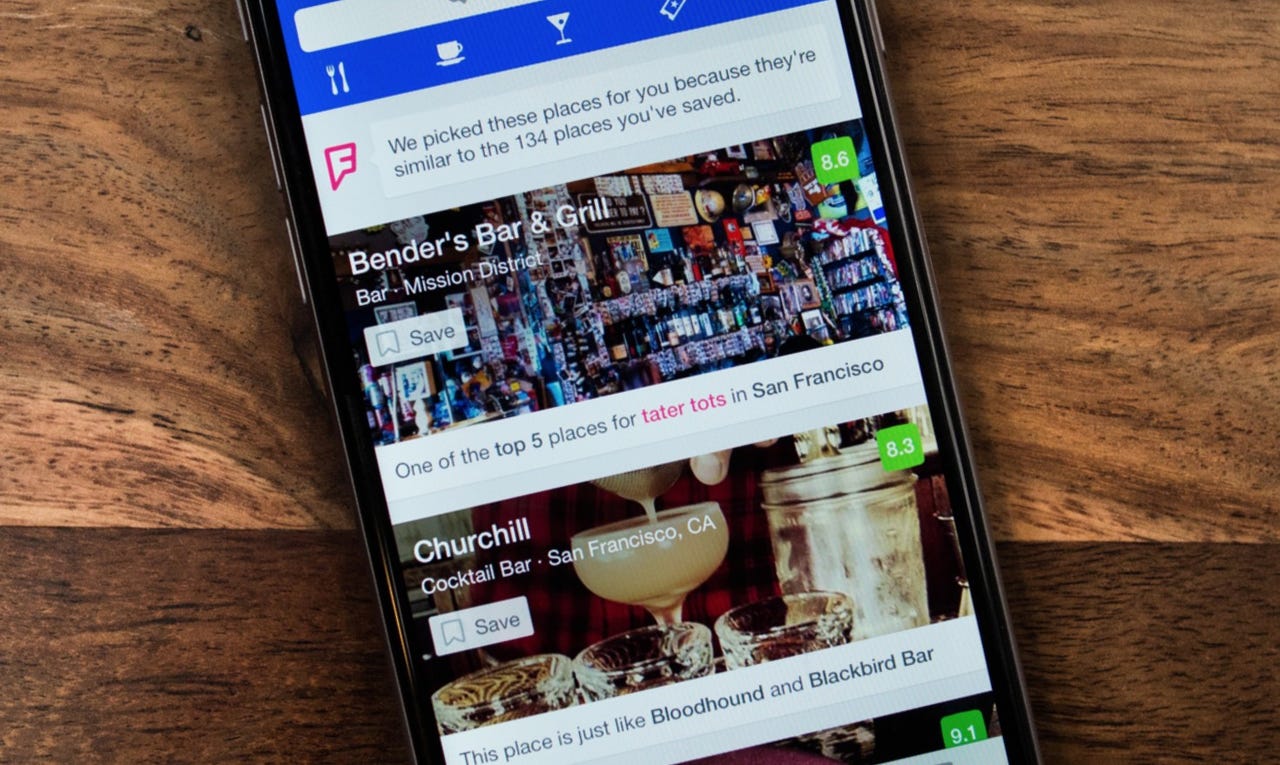
The notification site also published details of what it alleges to be a Foursquare breach.
It's not known when Foursquare, a location-based check-in site, was attacked, but the group claims more than 22.5 million accounts were stolen in the alleged breach.
According to another sample given to us, each record contains an email address, first and last name, gender, their location, Facebook ID, and Twitter username.
We were able to verify the portion of the accounts that we received by enumerating disposable email accounts with the site's password reset function (you can read more about how we verify breaches).
When reached, a spokesperson denied a breach.
"We have done an internal investigation and no breach has occurred," said a spokesperson.