MongoDB server leaks 11 million user records from e-marketing service

On Monday, a security researcher specialized in finding exposed databases has identified an unsecured MongoDB server that was leaking the personal details of nearly 11 million users. The server appears to belong to an email marketing firm based in California.
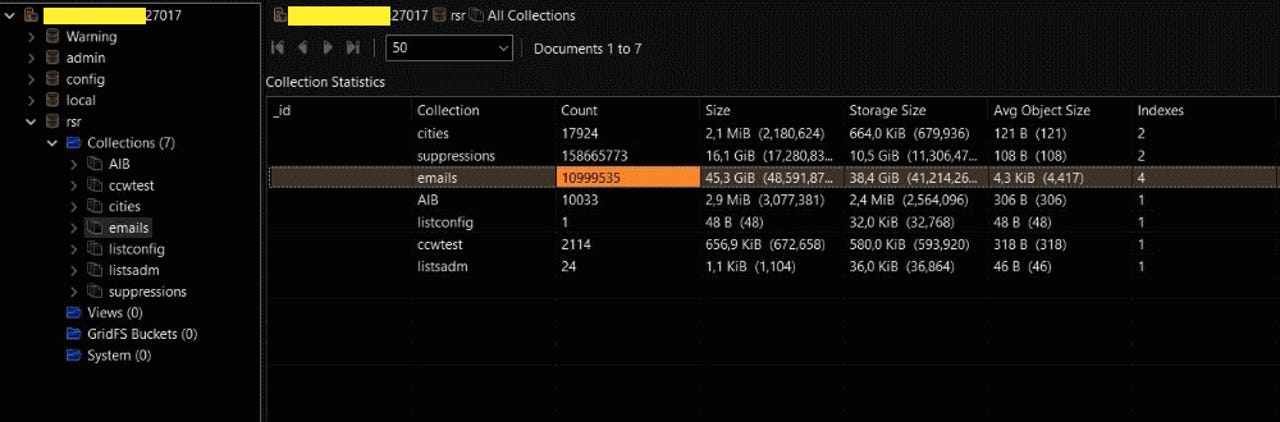
The data, contained in a 43.5GB dataset, included full names, email addresses, gender information, and physical addresses such as state, city, and ZIP code for 10,999,535 users.
All email addresses contained in this database were Yahoo-based, suggesting this was only a small part of a larger dataset, most likely stored on multiple servers.
Besides personal user information, the data also contained DNS details and email delivery status information about messages a user had received.
Bob Diachenko, the security researcher who discovered the breach and shared his findings with ZDNet, says the database had been left exposed online since at least September 13, the date when the Shodan search engine had last indexed it, and tagged it as a "compromised" server.
The database received this marker because, besides its normal content, it also included a table named "Warning" that contained a data collection with the following text:
"Your Database is downloaded and backed up on our secured servers. To recover your lost data: Send 0.4 BTC to our BitCoin Address and Contact us by eMail with your server IP Address and a Proof of Payment. Any eMail without your server IP Address and a Proof of Payment together will be ignored. You can apply for a backup summary within 12 hours. Then we will delete the backup. You are welcome!"
This is your typical ransom note that has been popping up on exposed MongoDB databases since late 2016.
The group behind this particular attack asked for ransom payments of 0.4 Bitcoin ($2,400) via the "3GKioTFrCFYcTmZR4DXPGatTXXp6Ugcq79" Bitcoin address. That address currently holds four payments for a total of 1.6 Bitcoin.
Also: Apple reassures customers after teen is busted for hacking it CNET
A Google search reveals that this particular message, Bitcoin and email address, have appeared in other cases reported by other MongoDB server owners based in China in late June [1, 2].
Since MongoDB ransomers tend to rotate email addresses and messages at various intervals, the presence of this note on the exposed server suggests the database was also exposed in late June when that particular database ransom campaign was in full force.
Furthermore, the two Chinese server owners reported that attackers wiped their databases in an attempt to force a payment for a "back-up" operation that clearly did not take place.
This detail also suggests that this particular email marketing database had also been wiped in June, restored, and continued to operate without proper security controls even after such a disruptive security incident.
While initially it was not clear who was the owner of this database, one small suffix in several records --such as "Content-SaverSpy-09092018"-- suggested this data may belong to a company named SaverSpy.
Also: 7 tips for SMBs to improve data security TechRepublic
Combining a simple Google search along with the nature of the user records found in the exposed database led both this reporter and Diachenko to believe the data belonged to SaverSpy.com, a daily deals website. The SaverSpy.com website claims to operate under the Coupons.com brand, but a Quotient spokesperson told ZDNet today that SaverSpy is only part of an affiliate program.
Both ZDNet and Diachenko alerted the operators of the SaverSpy website about the exposed server. While we have not heard back from the company, the server was secured earlier today.
Earlier this month, Diachenko also discovered a server belonging to Veeam, a data management firm, which was exposing over 445 million records.
UPDATE September 18, 13:40 ET: Article updated with statement from Quotient.
These are 2018's biggest hacks, leaks, and data breaches
Previous and related coverage:
What is malware? Everything you need to know
Cyber attacks and malware are one of the biggest threats on the internet. Learn about the different types of malware - and how to avoid falling victim to attacks.
Security 101: Here's how to keep your data private, step by step
This simple advice will help to protect you against hackers and government surveillance.
VPN services 2018: The ultimate guide to protecting your data on the internet
Whether you're in the office or on the road, a VPN is still one of the best ways to protect yourself on the big, bad internet.
Five computer security questions you must be able to answer right now
If you can't answer these basic questions, your security could be at risk.
Critical infrastructure will have to operate if there's malware on it or not
Retired US Air Force cyber-security expert shares his thoughts on the future of critical infrastructure security.
Ordinary Wi-Fi devices can be used to detect suspicious luggage, bombs, weapons
Researchers turn ordinary WiFi devices in rudimentary scanners that can identify potentially dangerous objects hidden inside bags or luggage.