NetSeer suffers hack, triggers Google malware warnings

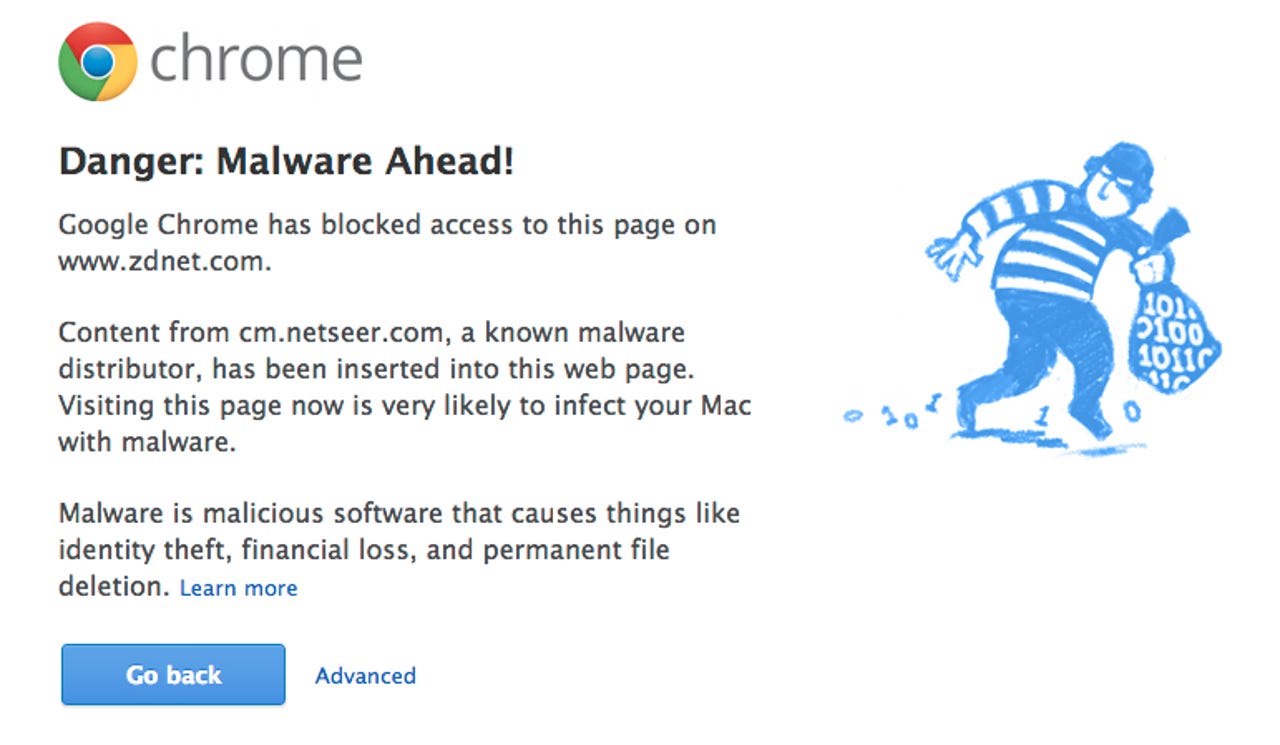
If you visited ZDNet earlier today and were warned by Google that you were entering a site with known malware, you weren't alone.
Internet advertising network NetSeer suffered a hack to its front-end Web site today that rippled across the Web sites of its advertising partners. The alerts warned visitors who were using the Chrome browser that the Web site they were visiting was a "known malware distributor."
A spokesperson for NetSeer confirmed the successful hacking attempt at around 5:30 a.m. PT, but noted that it did not affect its advertising network infrastructure.
The company is currently working with Google to rectify the situation.
A NetSeer spokesperson confirmed that its corporate network had been infected with malware, and Google subsequently added its domain to a list of malware-affected Websites. Because NetSeer's corporate site has the same domain name as its advertising network, Google triggered warnings on end-user machines warning users to avoid any Web page that happened to include an ad served from NetSeer's servers.
But, visitors to these Web pages were not at risk of being served up malware from the NetSeer advertising network, the company said.
"Our operations team went into all-hands-on-deck mode and we have successfully cleaned the site of the malware issue. We are also working with Google to do an expedited review of the site and remove the site from the malware impacted site-list so that browsing behavior can be restored for all users," a NetSeer spokesperson said.
The company said that it is currently in the process of notifying partners and customers.
Internet Explorer's SmartScreen filter—designed to mitigate such incidents for Windows users—did not block any Web pages, according to ZDNet's Ed Bott.
The Street, a known financial news site, said it has discontinued using Google advertisements "until the issue is resolved."
The New York Times was affected for a while, as was The Huffington Post among dozens of other high profile Web sites and news agencies. Some news outlets, notably The Guardian, tweeted their online following to warn that they were seeing issues, but there was no risk and they should ignore any warnings.
Hello, Chrome users. We're aware some of you are seeing malware warnings about Guardian articles. Please ignore; no risk.
— Guardian Tech (@guardiantech) February 4, 2013
Update at 1:50 p.m. ET: A NetSeer spokesperson said the company is "pleased to announce" that Google has removed the ad network from the list of sites impacted by malware.
Update at 5:15 p.m. ET: Unconfirmed reports suggest that the issues with NetSeer may have temporarily come back to haunt Chrome users. We've put in more questions to NetSeer and will update once we hear back.
IDG's Martyn Williams tweeted the following image of sister site CNET being blocked by Google Chrome. Here's the picture:
Update at 7:30 p.m. ET: A Google spokesperson said that while they do not comment on individual cases, "Safe Browsing is working as intended." They also noted in a blog post that explains how tricky it can be to clean a site of malware completely.
Update at 8:35 p.m. ET: A NetSeer spokesperson looped back to ZDNet with additional comment regarding further 'red warning' pages from Google Chrome users.
After we found and removed the infected files this morning, we were removed from the Google list of malware infected web sites. NetSeer was placed on the list a few hours later although we are unsure what triggered this second incident. We have been collaborating with Google throughout the day and they have been very responsive. As of approximately 4:00 p.m. PT (7:00 p.m. ET, I can confirm NetSeer is off the list. We are still investigating and cooperating with Google to ensure future continued compliance.