New Koobface campaign spoofs Adobe's Flash updater
The malware campaign is relying on compromised legitimate web sites, now representing 77% of malicious sites in general, and on hundreds of automatically registered Blogspot accounts with the CAPTCHA recognition process done on behalf of the users already infected by Koobface, compared to the gang's previous reliance on commercial CAPTCHA recognition services.
Here some of the most popular messages posted on Facebook for the time being:
Coongratulations! You are on TV! Funny vide0 with me :) HHolly sshit! Are you rreally in thiss viideo? Hollyy shhit! You are on hiidden cameera! Nicee! YYour boooty lookks greaat on thiss videoo! Saw thhat vvideo yesterdday... How coulld you do succh a thingg? Sweet!! Yourr ass loooks greaat on thiss video!! WWow! Is tthat reeally you in thaat videeo? You must see this vide0 now! :) You werre caughtt on our hiddeen camera!!
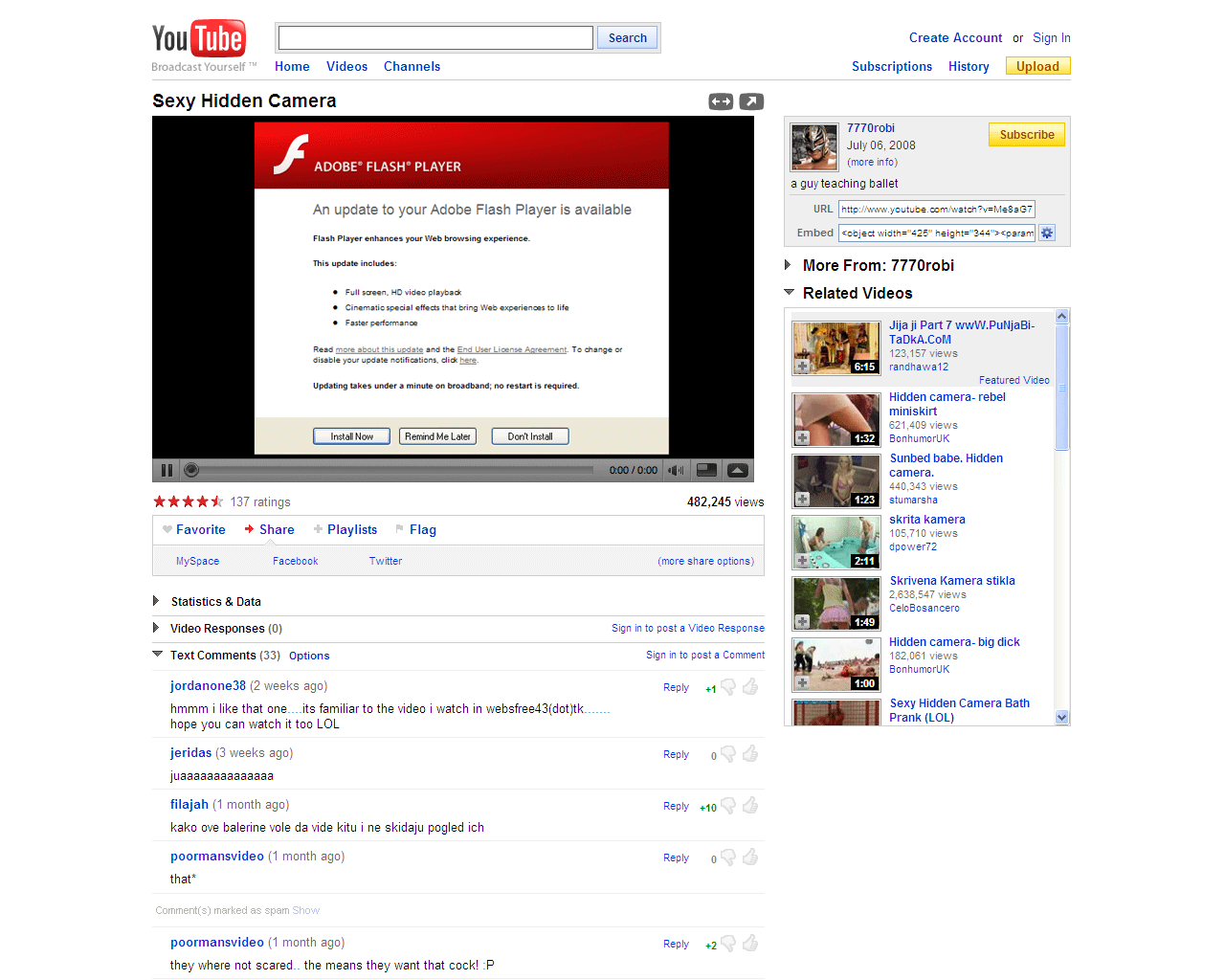
Upon visiting any of the URls issued by Koobface-infected Facebook users, a redirection to a (infected IP)/go.js? 0x3E8/youtube/console=yes/ takes place which is not only serving the setup.exe Koobface malware, but is also launching a pop-up with a scareware domain that is automatically rotated every 24 hours in order to evade detection. This double-layer monetization applied by the Koobface gang started taking place at the end of September, and remains active with the gang earning revenue by participating in a scareware affiliate network known as "Crusade Affiliates".
- Go through related posts: Gallery: Social engineering tactics of the Koobface botnet; Koobface worm joins the Twittersphere; Koobface Facebook worm still spreading; 56th variant of the Koobface worm detected