New security flaw opens iPhone, iPads to covert keylogging

On the back of Apple being scrutinized over an SSL flaw, researchers claim to have discovered another vulnerability which could allow hackers to log your keystrokes before sending such data to a remote server.
First spotted by Ars Technica, the security team at FireEye have developed a proof-of-concept application which could, in theory, run in the background of your mobile device and log your keystrokes without your knowledge.
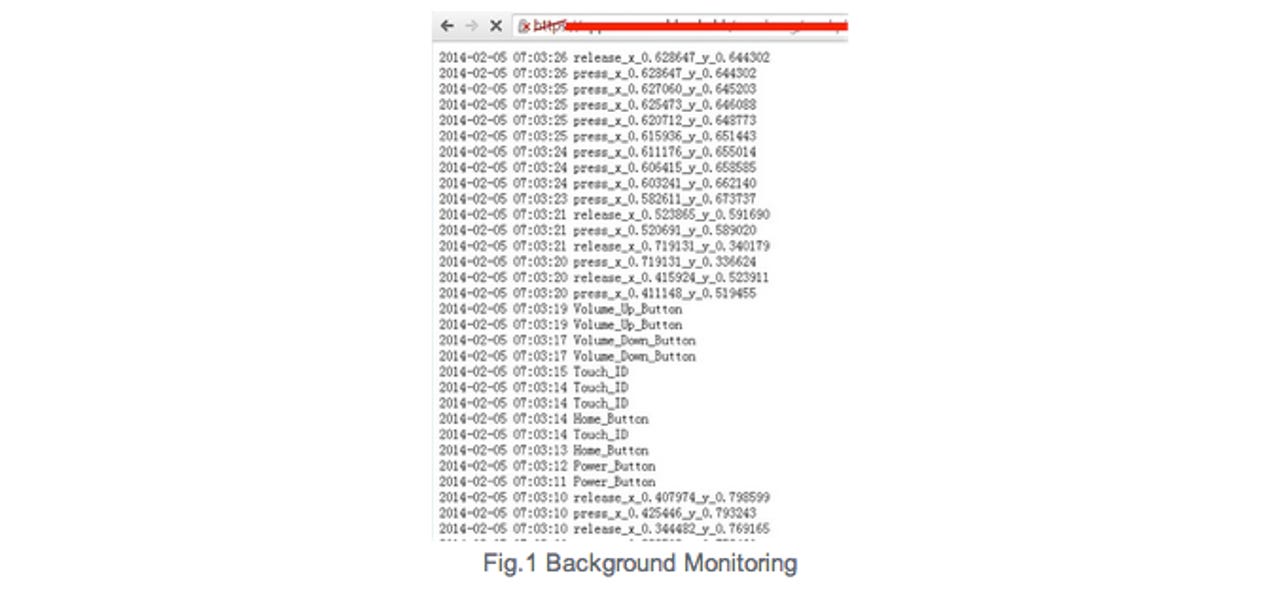
In a blog post, the researchers say that this background monitoring can take place on both jailbroken and non-jailbroken devices running iOS 7. After developing the "monitoring" application on non-jailbroken iOS 7 devices, the team tweaked the app to record all the user touch/press events in the background, including touches on the screen, home button pressing, volume button pressing and TouchID, before sending this data to a remote server of their choosing.
FireEye says that this type of "flaw" could be used by potential attackers in order to break in to user accounts and spy on them, by duping them in to downloading a malicious application, conducting a phishing campaign, or by exploiting another remote vulnerability of an application.
The demo app exploited the latest 7.0.4 version of iOS system on a non-jailbroken iPhone 5s successfully, but the team verified the vulnerability also exists in other iOS versions. However, the researchers do not detail the workarounds.
Furthermore, FireEye states that disabling iOS7's "background app refresh" feature will not block the vulnerability as it can still be bypassed -- as an example, an app can play background music without the use of this feature, and so a malicious application could use similar techniques.
According to Ars, a separate brief was posted detailing the research but was quickly removed. Reportedly, part of the brief stated:
"FireEye successfully delivered a proof-of-concept monitoring app through the App Store that records user activity and sends it to a remote server. We have been collaborating with Apple on this issue."
The latest scrutiny of Apple security comes as the tech giant quickly released a patch last Friday for an overlooked SSL encryption flaw which left iPhone, iPad and Mac devices open to man-in-the-middle (MITM) attacks. The SSL (Secure Socket Layer) vulnerability allowed hackers to intercept and steal communications data including email and login credentials due to a lack of SSL/TLS hostname checking, which meant that data which should have been encrypted was not.
However, the patch only covers the iPhone 4 and up, 5th generation iPod Touch and 2nd generation iPad. It is not known when a patch will be issued for Mac computers.