New study details the dynamics of successful phishing
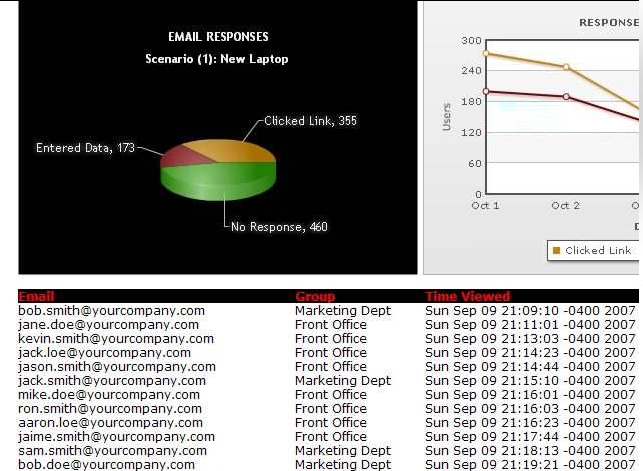
In a recently presented study by the Intrepidus Group, the company behind the PhishMe.com spear phishing awareness service allowing companies to ethically attempt to phish their employees on their way to build security awareness, presents some interesting key findings based on 32 phishing scenarios tested against a total of 69,000 employees around the world. Here they are:
- 23% of people worldwide are vulnerable to targeted/spear phishing attacks
- Phishing attacks that use an authoritative tone are 40% more successful than those that attempt to lure people through reward-giving
- Men and women are both equally susceptible to phishing
- On an average 60% of corporate employees that were found susceptible to targeted spear phishing responded to the phishing emails within three hours of receiving them
- People are less cautious when clicking on active links in emails than when they are requested for sensitive data
Metrics are invaluable, but in this case the obsession with metrics can result in more insecurities since it excludes the possibility of blended threats. For instance, last year I was closely monitoring a similar blended Skype phishing campaign, where the cybercriminals (IkbMan) were attempting to optimize the click-through rate of their campaign by serving client-side exploits to the visitors, "just in case" if they find the site suspicious and do not enter any accounting data. For the time being the exploit is served instantly upon visiting the phishing site, however, the possibility for serving it only if the user hasn't entered anything and is leaving the site is always there.
- Go through related phishing trends and tactics: Research: 76% of phishing sites hosted on compromised servers; Microsoft study debunks phishing profitability; Phishers increasingly scamming other phishers; DIY phishing kits introducing new features; Phishers apply quality assurance, start validating credit card numbers; Lack of phishing attacks data sharing puts $300M at stake annually
Considering one of the key points from Intrepidus Group's study, namely that "People are less cautious when clicking on active links in emails than when they are requested for sensitive data", a phishing email should be treated as spam, namely (in a perfect world) it shouldn't be even allowed to reach the employee's mailbox. Otherwise, it appears that the trade-off for coming up with quality metrics on the current degree of security awareness in regard to phishing, is the potential exposure of the tested population against potential blended threats.
With managed localization services in the sense of dedicated translators of messages to be used in spam, phishing, and malware campaigns already a fact, the cybercrime ecosystem will soon be talking in a native language, and with the increasingly automated phishing tools whose features were once available to a more sophisticated crowd of cybecriminals, now available for free - the future of phishing looks promising.
The only threat that can outpace its growth is the threat posed by the much more efficient and sophisticated financial data targeting tactic of using crimeware targeting each and every E-banking site simultaneously upon successful infection.