Nokia 'hijacks' mobile browser traffic, decrypts HTTPS data

Nokia has caused a stir by performing, in the words of one security researcher, "man in the middle attacks" in order to compress data and speed up the loading of Web pages on some of its phones.
The Finnish phone giant has since admitted that it decrypts secure data that passes through HTTPS connections -- including social networking accounts, online banking, email and other secure sessions -- in order to compress the data and speed up the loading of Web pages.
But, Nokia says that there is nothing to worry about.
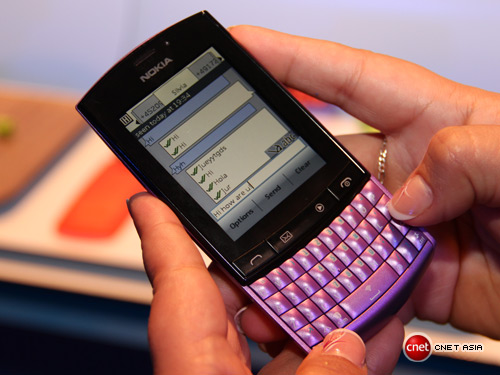
Researcher Gaurang Pandya discovered that browser traffic from his Nokia (Series 40) "Asha" phone was being routed through Nokia's servers. This is no different to how Opera Mini works or even the BlackBerry browser, and remains popular in areas where the cell service is poor or in developing nations where cash doesn't grow on trees.
Nokia, however, goes one step further, the researcher says. A second post by Pandya, published this week, stated that Nokia was "man in the middle" attacking HTTPS traffic on its user's phones. In simple terms, HTTPS traffic was being routed through Nokia's servers, and could be accessed by Nokia in unencrypted form.
From the tests that were preformed, it is evident that Nokia is performing Man In The Middle Attack for sensitive HTTPS traffic originated from their phone and hence they do have access to clear text information which could include user credentials to various sites such as social networking, banking, credit card information or anything that is sensitive in nature.
He notes that whether be it "HTTP or HTTPS sites when browsed through the phone," Nokia has "complete information unencrypted (in clear text format) available to them for them to use or abuse."
He also noted that in Nokia's privacy statement, it states: "The URLs of such sites which you access with the Nokia Browser are stored by Nokia." However, it does point out that: "Your browsing is not associated to any personally identifiable information and we do not collect any usernames or passwords or any related information on your purchase transactions, such as your credit card number during your browsing sessions."
Nokia responded to the claims and issued a statement. The phone maker points out that this practice is solely so "users can get faster Web browsing and more value out of their data plans." After all, Nokia phones are still popular in developing countries where data is expensive and reducing one's bills is an absolute necessity.
We take the privacy and security of our consumers and their data very seriously.
The proxy servers do not store the content of web pages visited by our users or any information they enter into them. Nokia has implemented appropriate organizational and technical measures to prevent access to private information. Claims that we would access complete unencrypted information are inaccurate.
But the phone maker also said:
When temporary decryption of HTTPS connections is required on our proxy servers, to transform and deliver users' content, it is done in a secure manner.
In other words, yes Nokia does decrypt your secure browsing data but it's not a big deal.
The problem stands that Nokia hasn't told anyone it does this. What Nokia says in its privacy policy and what the security researcher discovered does not seem to add up. While the practice of wanting to cut down on user data bills is far from a bad thing -- Opera does this, RIM does this with BlackBerry smartphones -- these companies openly state what the process is.
There is almost no doubt that Nokia not doing anything with user or customer data. It isn't one giant nefarious scheme to harvest usernames and passwords to acquire vast amounts of money from bank accounts because the company's finances stink. (Besides, Nokia is based in Finland, a member of the EU. If Nokia was abusing user data and its customers' privacy, the European authorities would come down so hard on the company, it would -- at least the state it is in -- bankrupt it.)
Nokia should learn from this. What it is doing isn't bad as such. If Nokia was up-front about the whole process, there may have been rumblings from the security industry but there wouldn't have suffered a public relations napalm to the company's reputation.